fidgeting bits retweetledi

Hey, I'm going to ask you something just in case.
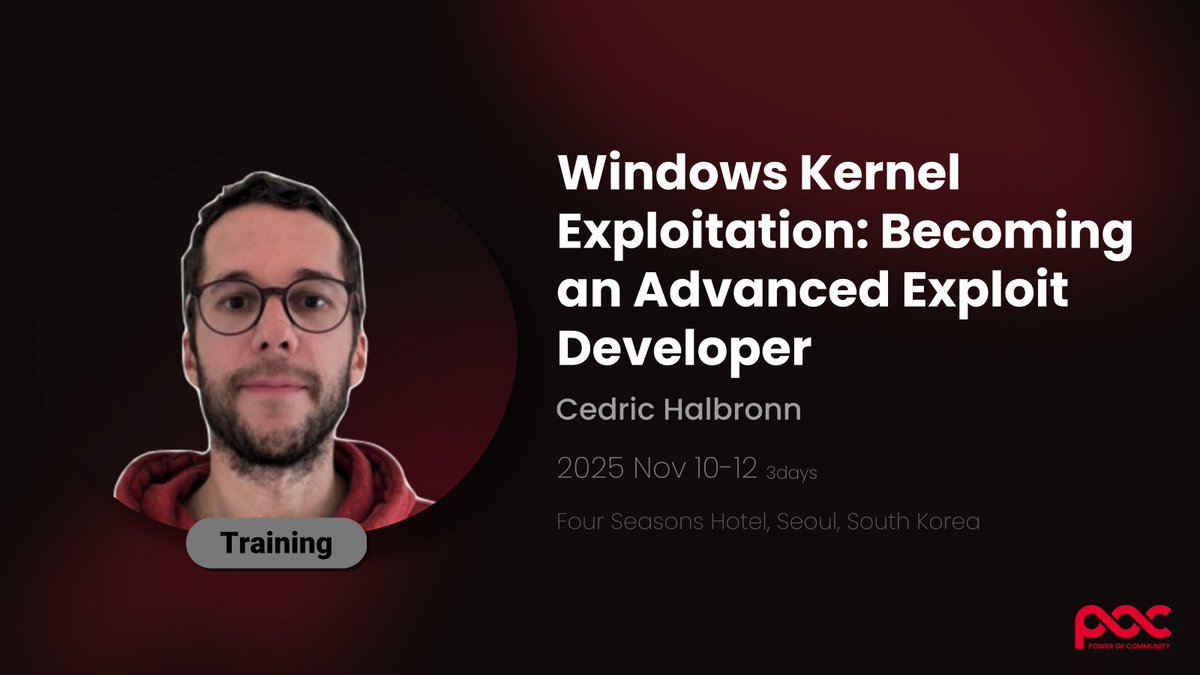
I teach a Linux kernel exploitation course and I wanted to differentiate to the class the kinds of randomizations we see in memory. Even without KASLR or any other configurable randomization, if you check a slub cache right after booting up, the slab base address is subject to some randomization, independent of the cache as far as I can tell.
I spent some time investigating this and there's a point during the boot that there's no randomization, but it'll appear somehow. My guess is that some randomization will happen after the other processors are set up (maybe APIC is undeterministic). I even checked the first kmem caches being set up and kmalloc allocations. I didn't finish my analysis, and couldn't come up with a good hypothesis that could explain this behavior. Do you know anything about this? Thank you, and I've checked your book several times during my analysis.
English