
Guido Grillenmeier
55 posts




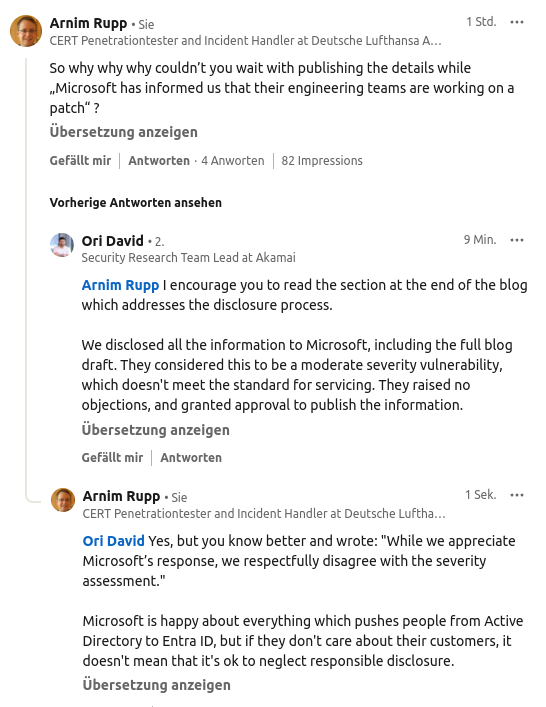



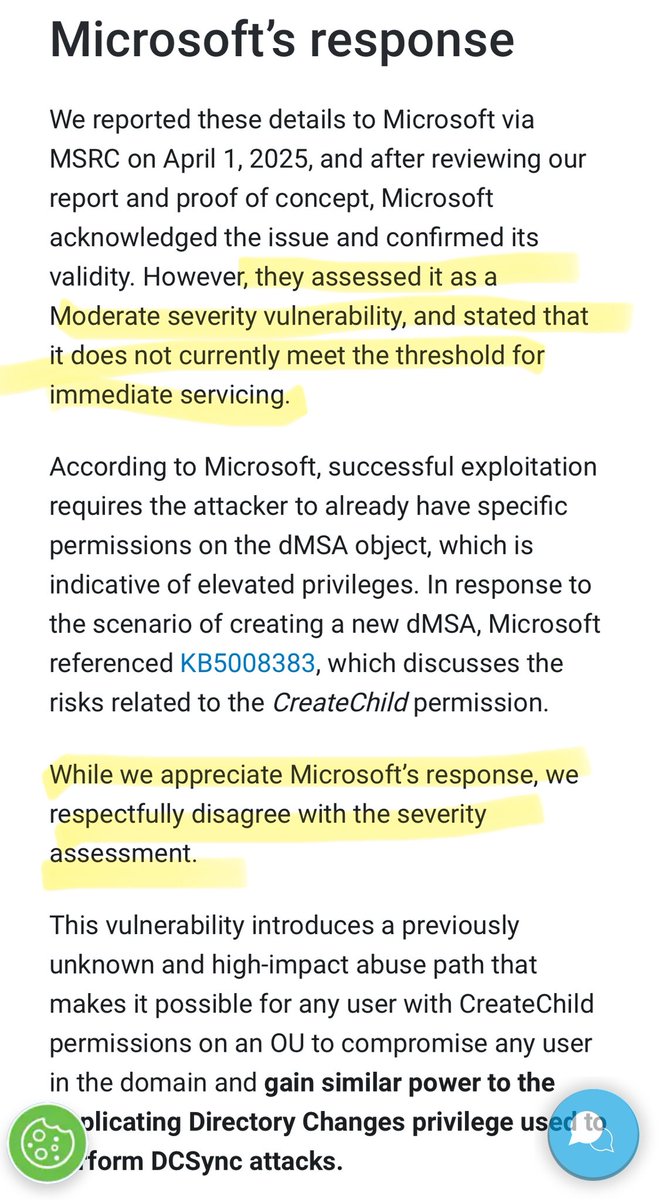
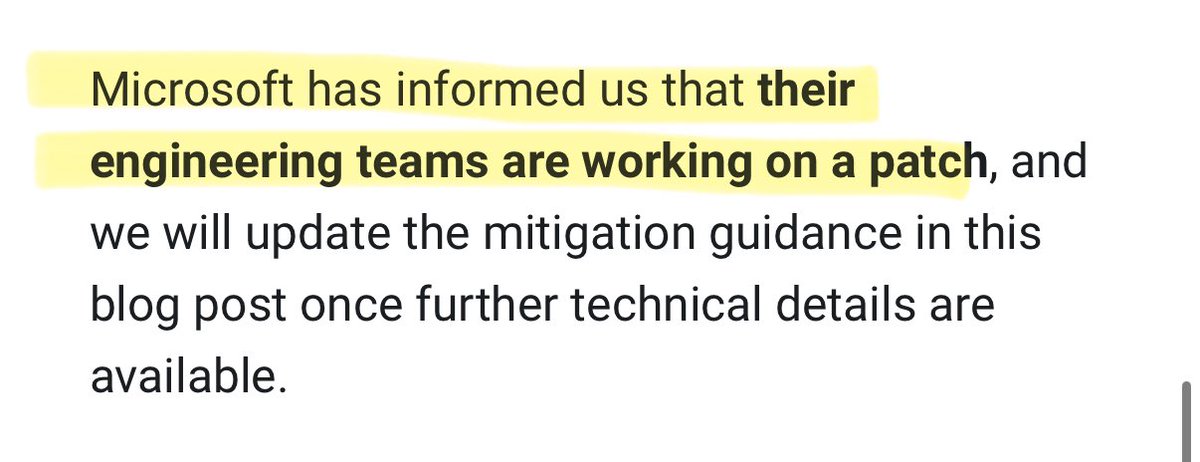
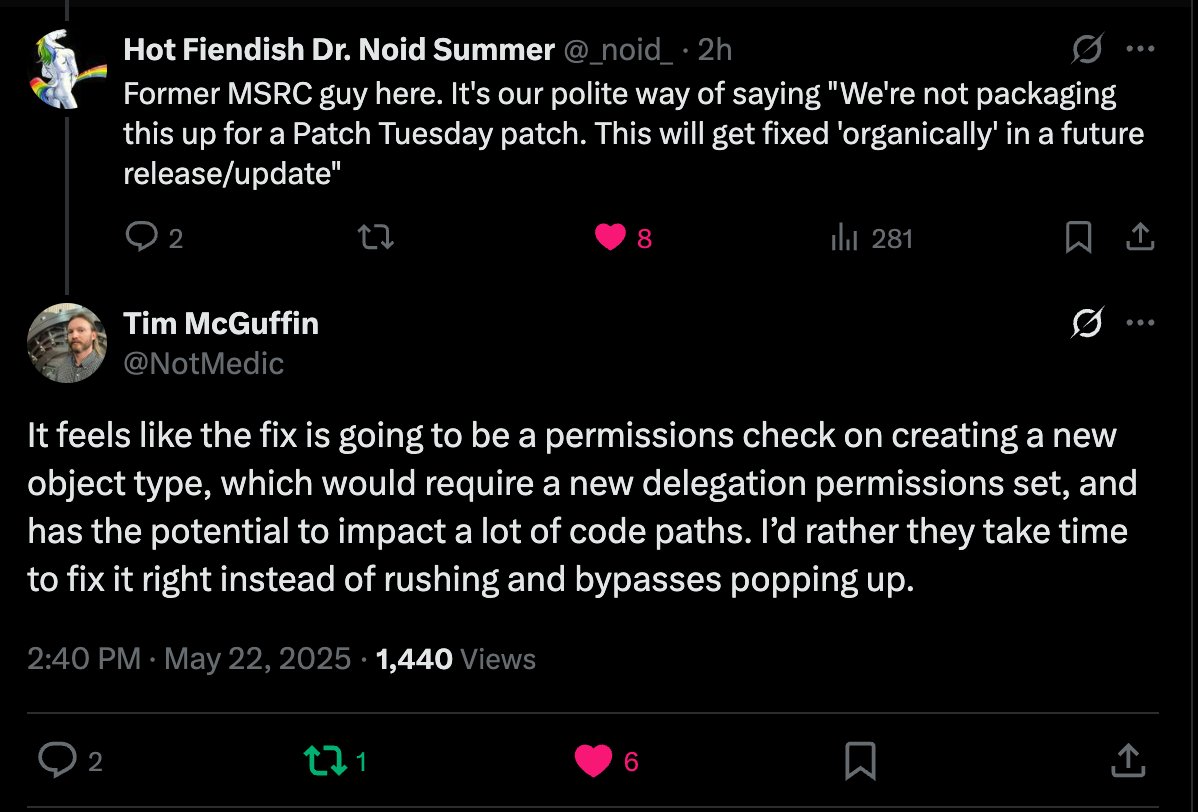
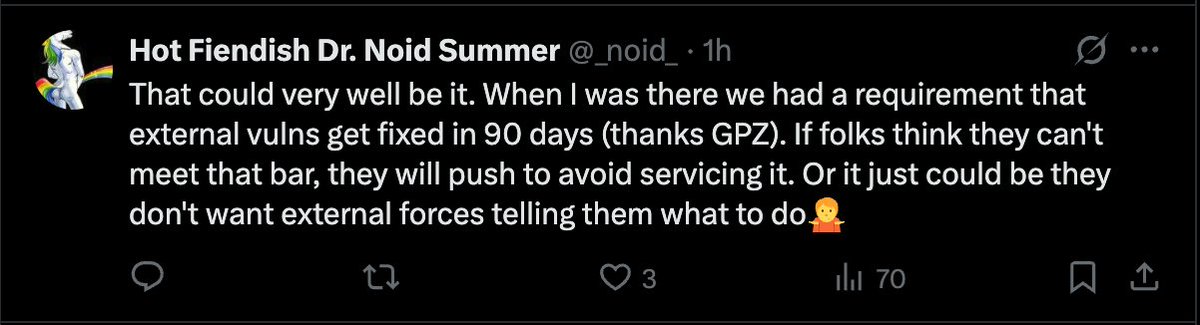
#BadSuccessor - a textbook example of why the security ecosystem is broken - A privilege escalation vuln in Windows Server 2025 AD (via dMSA) - Full domain compromise with default config - Microsoft was told, agreed it’s real, but rated it "moderate" - No patch, No fix - No code execution needed - No need to touch the DC - No RPC, no ntds.dit - Just a write to one attribute on an account you can create - Rubeus already supports dMSA abuse (since February) - Metasploit module is in the works Researchers published everything anyway. Because… "we respectfully disagree with Microsoft’s assessment". So yeah, let’s just drop an end-to-end domain takeover technique online to prove a point. To be fair, Windows Server 2025 isn’t widely deployed yet, so the real-world blast radius today is limited. But this isn’t about today - it’s about trust, process, and what happens when security decisions are driven by vendor priorities and researcher egos. What this tells me: 1. Microsoft either: - Can’t assess bugs anymore - Or stopped caring about on-prem AD completely (because Entra ID is what they want to sell) 2. And the offensive sec crowd? - They knew this would hit hard - But chose to burn the world anyway - Because their urge to be right > everyone else’s security In the end, both sides look bad. Microsoft, for being dysfunctional or apathetic Researchers, for chasing clout over coordinated disclosure Congrats. In a rare show of unity, both sides managed to screw this up. Blog: akamai.com/blog/security-… LinkedIn: linkedin.com/feed/update/ur… Metasploit issue: github.com/rapid7/metaspl…












#ICYMI In this HIP podcast session, @shorinsean talks with @alsugano about his experiences on the front lines in helping companies prevent or recover from the #Hafnium attack. 🎧 Listen to the full episode now: bit.ly/3aeRgkz




#IdentityManagementDay is today. To bring #cybersecurityawareness, what do experts from @SemperisTech @bitglass @CloudentityTEAM & @DigitalGuardian have to say about building a stronger digital perimeter? @InfoSec_Review asks: bit.ly/3aaUFRg



