
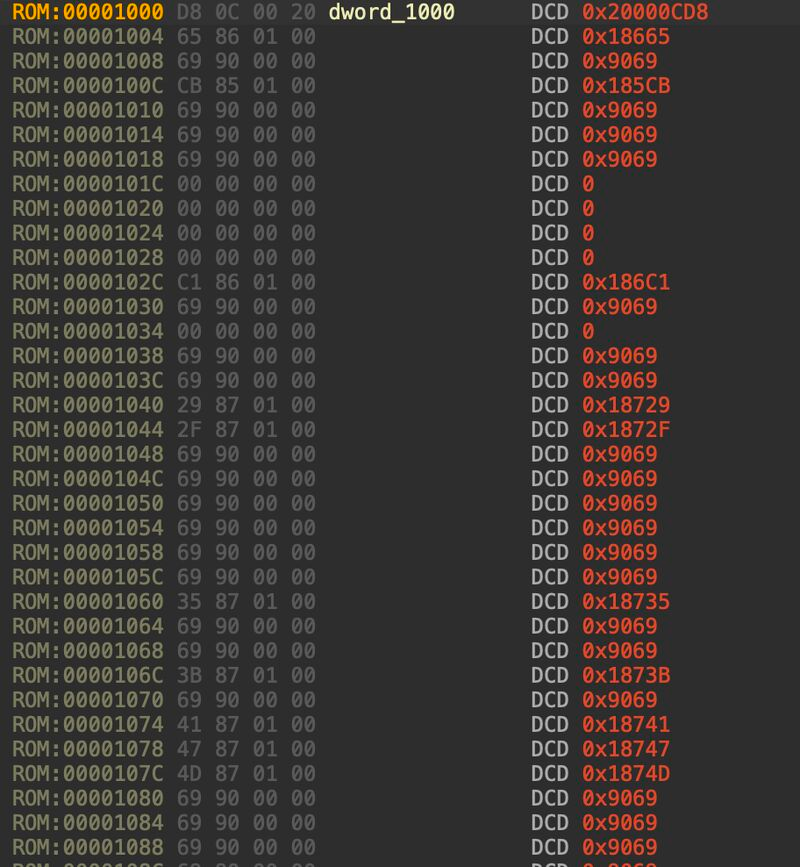
Reverse Engineering Mask ROM @gabrielcybersecurity/note/p-190487513?utm_source=notes-share-action&r=2ut046" target="_blank" rel="nofollow noopener">substack.com/@gabrielcybers…
English
Gabriel Gonzalez
2.6K posts

@GabrielGonzalez
https://t.co/EJcsZWyUMW




Gabriel Gonzalez was recently featured in a ETAS podcast to discuss his research on drone hacking through injection attacks. Check out the podcast to explore “fault injection attacks... and how they can be used to bypass embedded security features.” …rowsautomotivesoftware.buzzsprout.com/1841523/episod…














¿Cómo se podría hackear la red eléctrica española? ¿Qué es una red OT? ¿Qué herramientas existen para auditar sistemas industriales? Para contestar a estas y más preguntas, nos acompaña @GabrielGonzalez , Director de Hardware Hacking en IOActive. youtube.com/watch?v=GzNZ1R…





