Chimamaka Ukaga
615 posts

Chimamaka Ukaga retweetledi

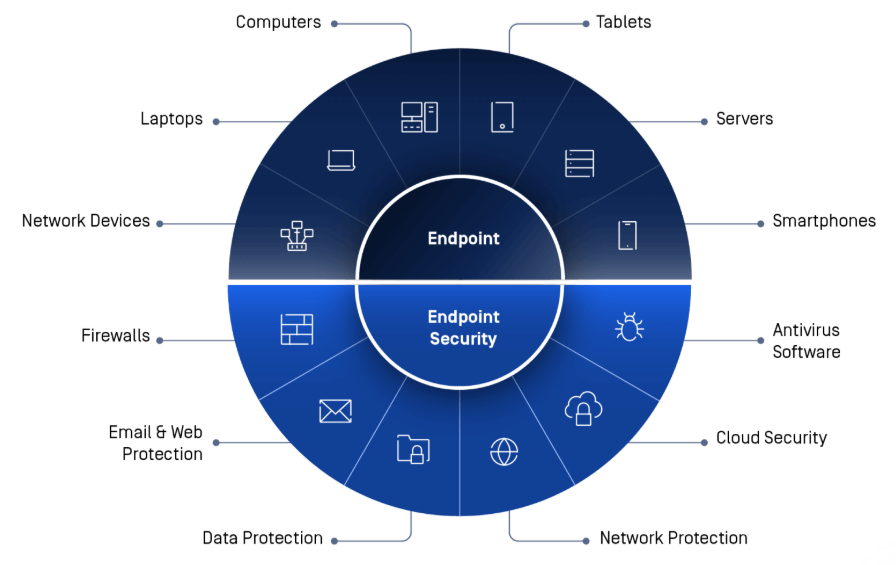
What Is Endpoint Security?
An endpoint is any device that connects to a network.
Examples include:
- Laptops
- Servers
- Mobile devices
- Workstations
Each endpoint represents a potential entry point for attackers.
Endpoint security focuses on protecting these devices through:
- Antivirus and anti-malware tools
- System monitoring
- Patch management
- Access controls
Many cyber attacks begin with a compromised endpoint, which is why securing them is a key part of an organization’s overall defense strategy.
#Cybersecurity #EndpointSecurity #CybersecurityAwareness
English
Chimamaka Ukaga retweetledi

Day 100 - #100DaysOfCybersecurity 🎉 (Final Day)
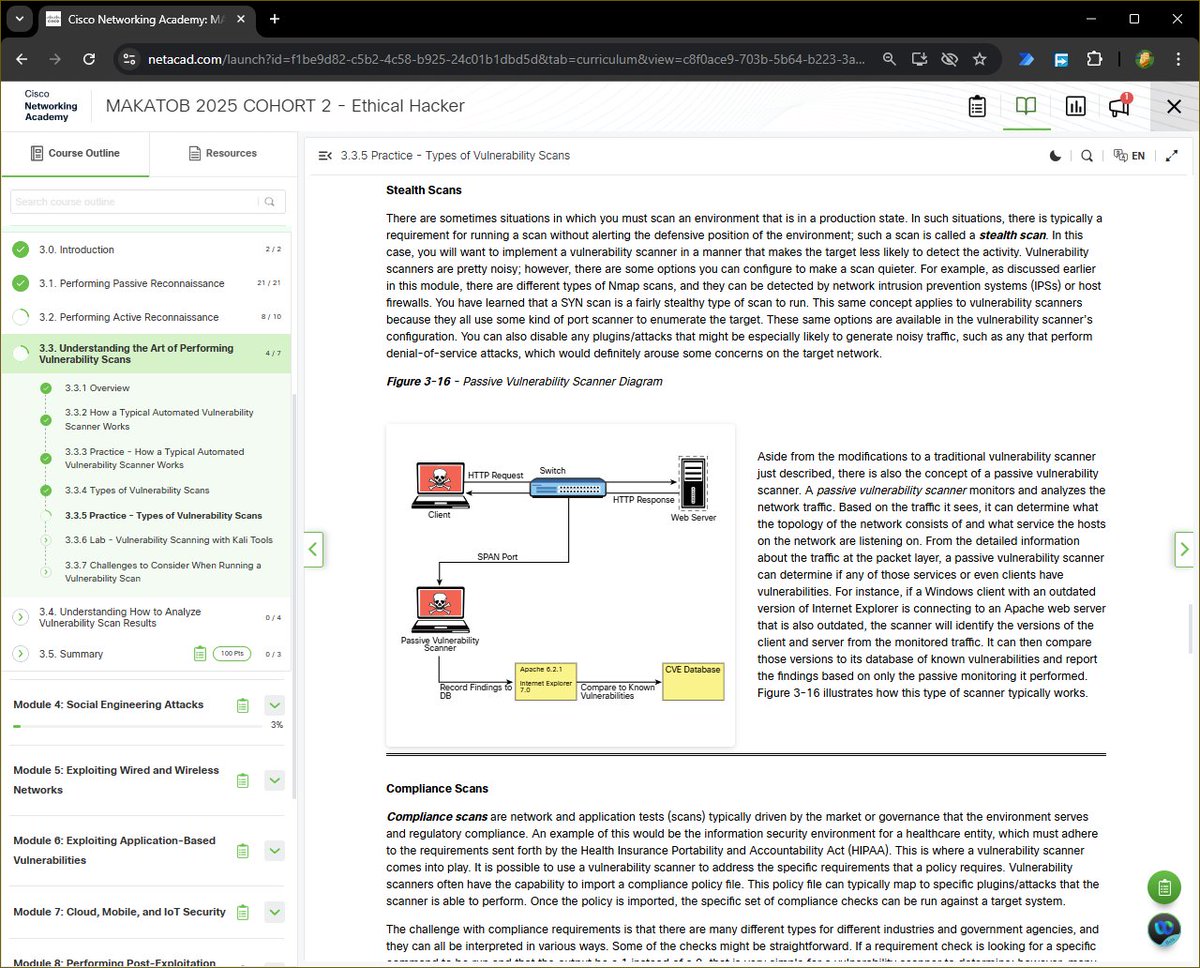
Today marks the completion of my 100 Days of Cybersecurity Challenge, and I wrapped it up by diving into a critical concept in vulnerability management: Types of Vulnerability Scans.
After building a strong foundation in reconnaissance, and packet crafting, today I tied everything together by exploring how vulnerabilities are systematically discovered in real-world environments.
What I Learned Today:
Vulnerability scanning is about strategy, context, and accuracy.
Here are the key scan types I explored today:
Unauthenticated Scans
Simulate an external attacker’s view.
-Useful for identifying exposed services, but limited visibility.
Authenticated Scans
Provide deeper insight by logging into the system (with credentials).
-More accurate results, fewer false positives.
Discovery Scans
Focus on identifying the attack surface (hosts, ports, services).
- This builds directly on tools like Nmap.
Full Scans
Run all available checks and plugins.
- Powerful but can be noisy and resource-intensive.
Stealth Scans
Designed to reduce detection (e.g., SYN scans, reduced noise).
- Important in production or monitored environments.
Compliance Scans
Validate systems against regulatory standards (e.g., security policies).
- Critical for enterprise and regulated industries.
⚙️ Key Insight
Vulnerability scanners follow a structured workflow:
- Discover hosts & services (often using tools like Nmap)
- Identify software versions
- Match against known vulnerabilities (CVE databases)
- Generate findings (which must be validated)
⚠️ One major lesson:
False positives are real, and validation is just as important as detection.
🧠 Why This Matters
This ties directly into everything I’ve been learning:
Recon - identifies targets, builds profile
Enumeration - reveals services
Scanning - uncovers weaknesses
It’s the bridge between finding systems and actually assessing their security posture.
🚀 Reflection - 100 Days Later
What started as curiosity has evolved into structured, hands-on cybersecurity practice.
Cybersecurity goes beyond tools, it’s about understanding systems, thinking critically, and validating everything.
This is just the beginning.
@jay_hunts @ireteeh @segoslavia
#RedTeamer #Cybersecurity #EthicalHacking #VulnerabilityAssessment #Nmap #RedTeam #LearningInPublic

English
Chimamaka Ukaga retweetledi

Day 91 - #100DaysOfCybersecurity 🔐
Today was about resting and recharging.
Learning cybersecurity consistently requires a lot of focus and discipline, so I intentionally took today to slow down, reflect, and regain energy for the days ahead.
To mark the Easter season, I treated myself to a nice meal that I cooked myself. You’ll just have to take my word for it because I won’t be posting the food 😄.
Later in the evening, I joined two cybersecurity community sessions, and both turned out to be incredibly valuable.
First was the Guardians Of the Cyber Realm Sunday Community Meeting. The session focused on Resume Building & Job Positioning, and our honorable speaker Miss. @_DeejustDee shared practical insights on how to structure a CV/resume effectively, position our skills for the roles we are targeting, and present our experience in a way that stands out to recruiters.
She shared several useful tips and ideas on how to stay compose to ace an interview, and her professionalism, combined with a bit of witty humor 😅made the session not only informative but also engaging and relatable.
The second session was the Cybersecurity Xlass on X Spaces, hosted by our very own able community leader @cyberjeremiah
In the session, I had the opportunity to briefly share my cybersecurity learning journey from the past week.
It was inspiring listening to others talk about their progress, challenges, and lessons learned as well. Community spaces like this remind me that growth in cybersecurity is not just about studying tools and concepts, but also about learning from others and supporting each other’s journey.
My Reflection 💡
Even on a rest day, being part of supportive communities can still bring learning opportunities and motivation.
Today was a great reminder that balance, community, and consistency are all part of the journey.
Tomorrow, I will get back into learning.
@jay_hunts @ireteeh @segoslavia
#RedTeamer #Cybersecurity #LearningInPublic #CybersecurityCommunity #CareerGrowth



English
Chimamaka Ukaga retweetledi

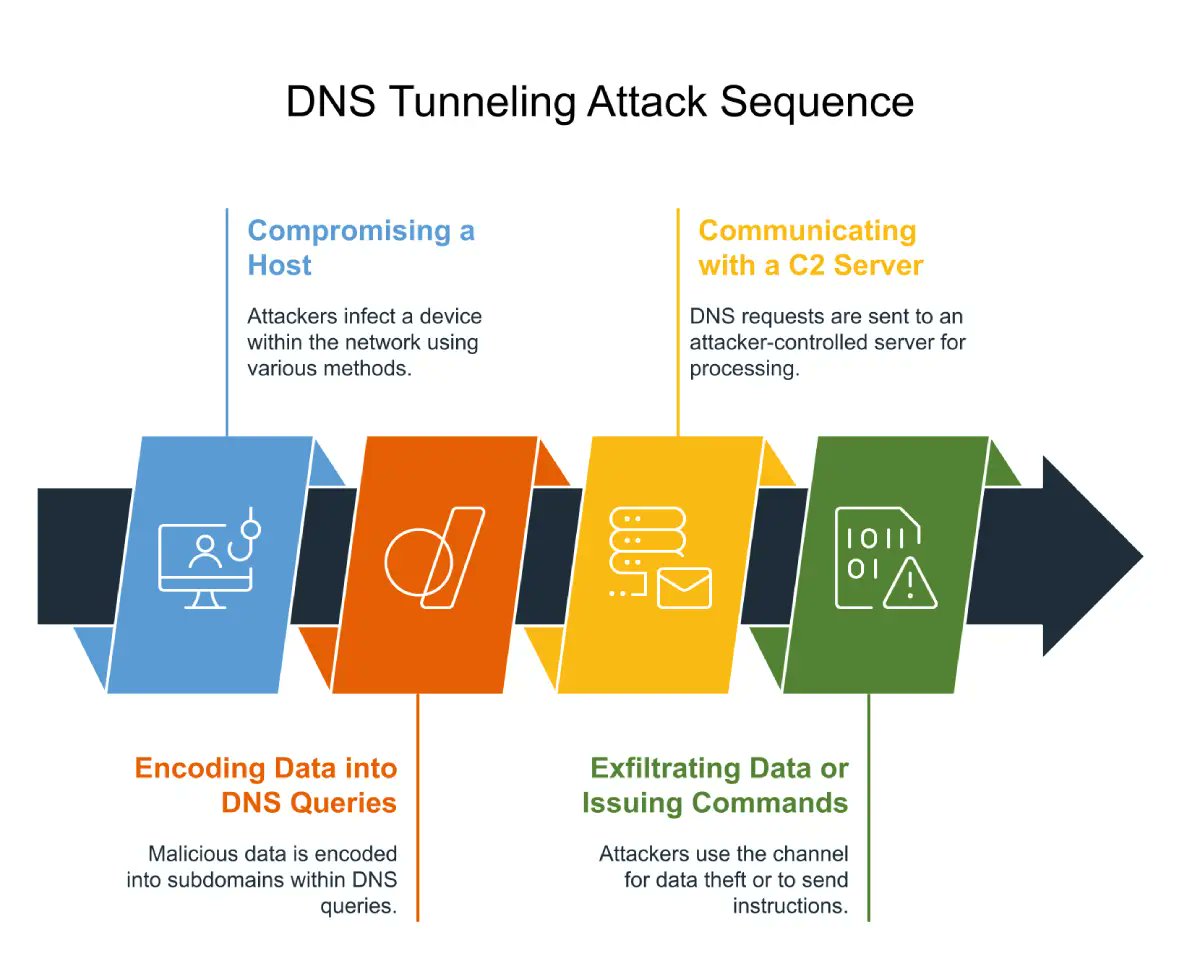
Detecting DNS Tunneling
Attackers sometimes abuse DNS to secretly move data in and out of a network.
This technique is called DNS tunneling.
Instead of normal domain lookups, attackers encode data inside DNS queries.
For example, a query might look like this:
data123.attacker-domain.com
The encoded data is hidden inside the subdomain.
Because DNS traffic is usually allowed through firewalls, attackers can use it to bypass security controls.
During traffic analysis with Wireshark, suspicious indicators may include:
- Extremely long DNS queries
- High frequency of DNS requests
- Encoded or random-looking domain names
Monitoring DNS traffic is an important step in detecting covert communication channels.
#Networking #Infosec #LearningInPublic #LearningJourney
English
Chimamaka Ukaga retweetledi

Day 92 - #100DaysOfCybersecurity
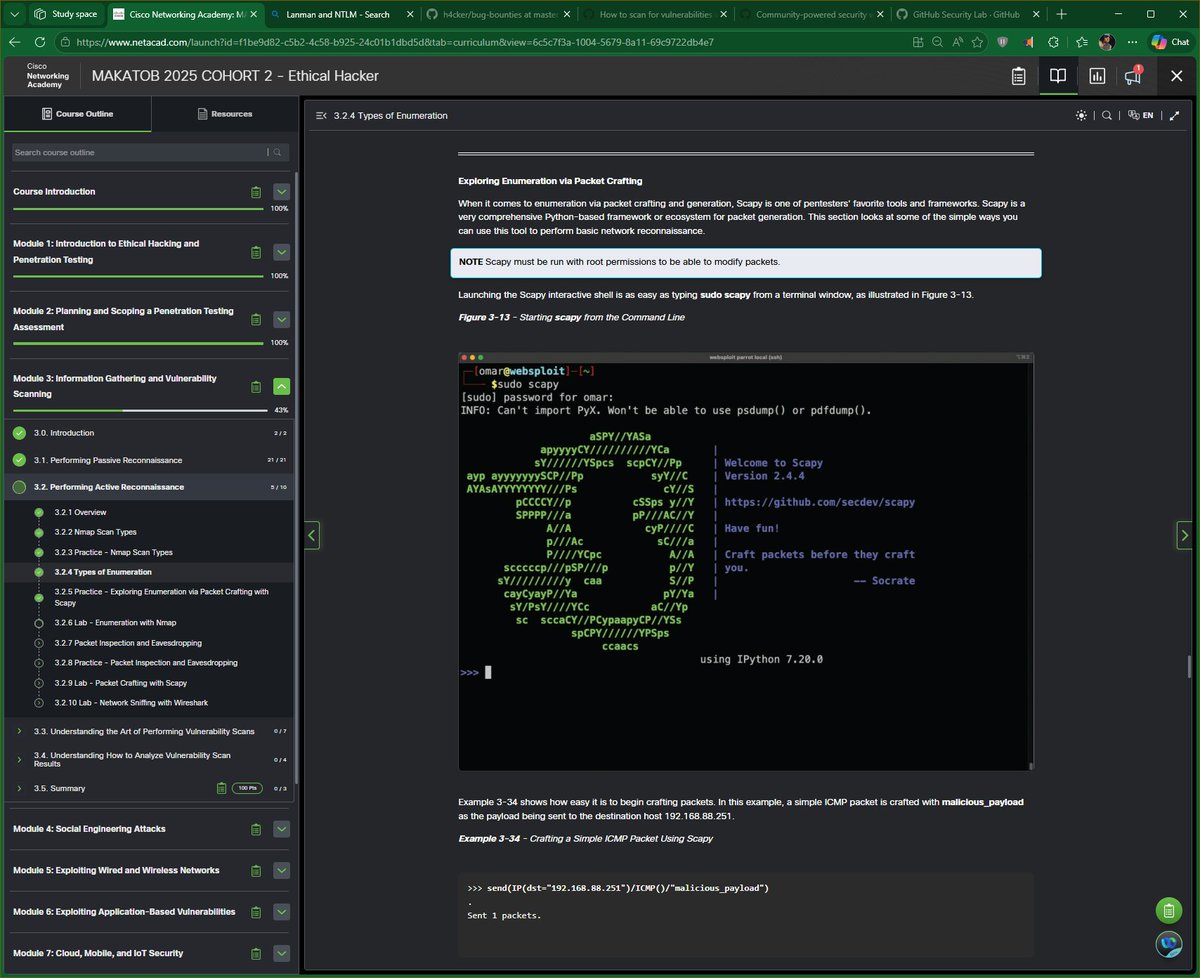
Today I continued Module 3 of my Ethical Hacker course, focusing on an important phase of active reconnaissance: Enumeration.
Enumeration goes beyond simple scanning.
While scanning identifies open ports and services, enumeration extracts detailed information from those services, helping a penetration tester better understand the target environment.
Types of Enumeration I Learned Today
🔎 Host Enumeration
This involves identifying systems on a network. Tools like Nmap or Masscan can perform host discovery scans to determine which devices are active within a subnet.
👤 User Enumeration
Attackers attempt to discover valid usernames within a system. For example, using SMB (Server Message Block) over TCP port 445, tools like Nmap scripts can enumerate user accounts from Windows systems.
👥 Group Enumeration
This technique identifies user groups and their memberships within a system. Understanding group roles helps attackers determine privileged accounts or administrative groups.
📁 Network Share Enumeration
Shared folders and network resources can expose sensitive data. Tools such as Nmap SMB scripts, smbclient, or enum4linux can reveal shared directories and permissions.
🌐 Web Application Enumeration
Once a web server is discovered, the next step is mapping the web application’s attack surface. Tools like Nmap http-enum scripts or Nikto help identify directories, admin panels, and potential vulnerabilities.
⚙️ Service Enumeration
This process identifies services running on a host and gathers additional details such as software versions, configurations, and authentication mechanisms.
Exploring Packet Crafting with Scapy
I also explored Scapy, a powerful Python-based framework used for packet crafting and network experimentation.
With Scapy, penetration testers can:
- Craft custom packets
- Send probes to target systems
- Analyze network responses
- Build custom scanning scripts
For example, a simple ICMP packet can be crafted and sent to a host to observe how the system responds.
Key lesson 💡
Enumeration is where reconnaissance becomes deep intelligence gathering. By combining tools like Nmap, enum4linux, smbclient, Nikto, and Scapy, a penetration tester can reveal users, services, shares, and system configurations that may later lead to exploitation.
Next step: Hands-on labs to practice the enumeration techniques I just learnt.
@jay_hunts @ireteeh @segoslavia
#RedTeamer #Cybersecurity #EthicalHacking #PenetrationTesting #Nmap #Scapy


English
Chimamaka Ukaga retweetledi

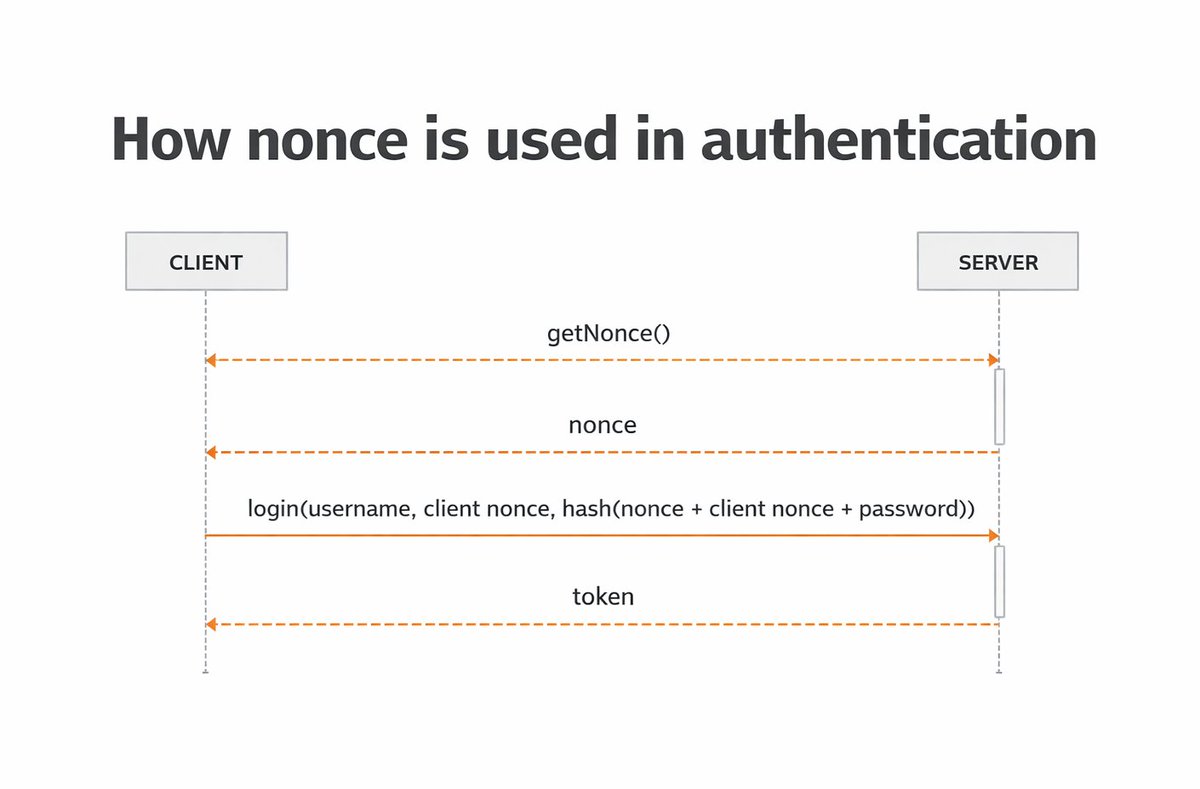
What Is a Replay Attack?
A replay attack occurs when an attacker captures legitimate network communication and retransmits it later to gain unauthorized access.
For example:
1️⃣ A user authenticates to a system
2️⃣ The attacker captures the authentication traffic
3️⃣ The attacker replays that same traffic to impersonate the user
If the system cannot detect that the message has already been used, the attacker may successfully authenticate.
To prevent replay attacks, many systems use mechanisms such as:
- Nonces (unique one-time numbers)
- Timestamps
- Session tokens
These techniques ensure that each authentication request is unique and cannot be reused.
#Networking #Infosec #LearningInPublic #LearningJourney

English
Chimamaka Ukaga retweetledi

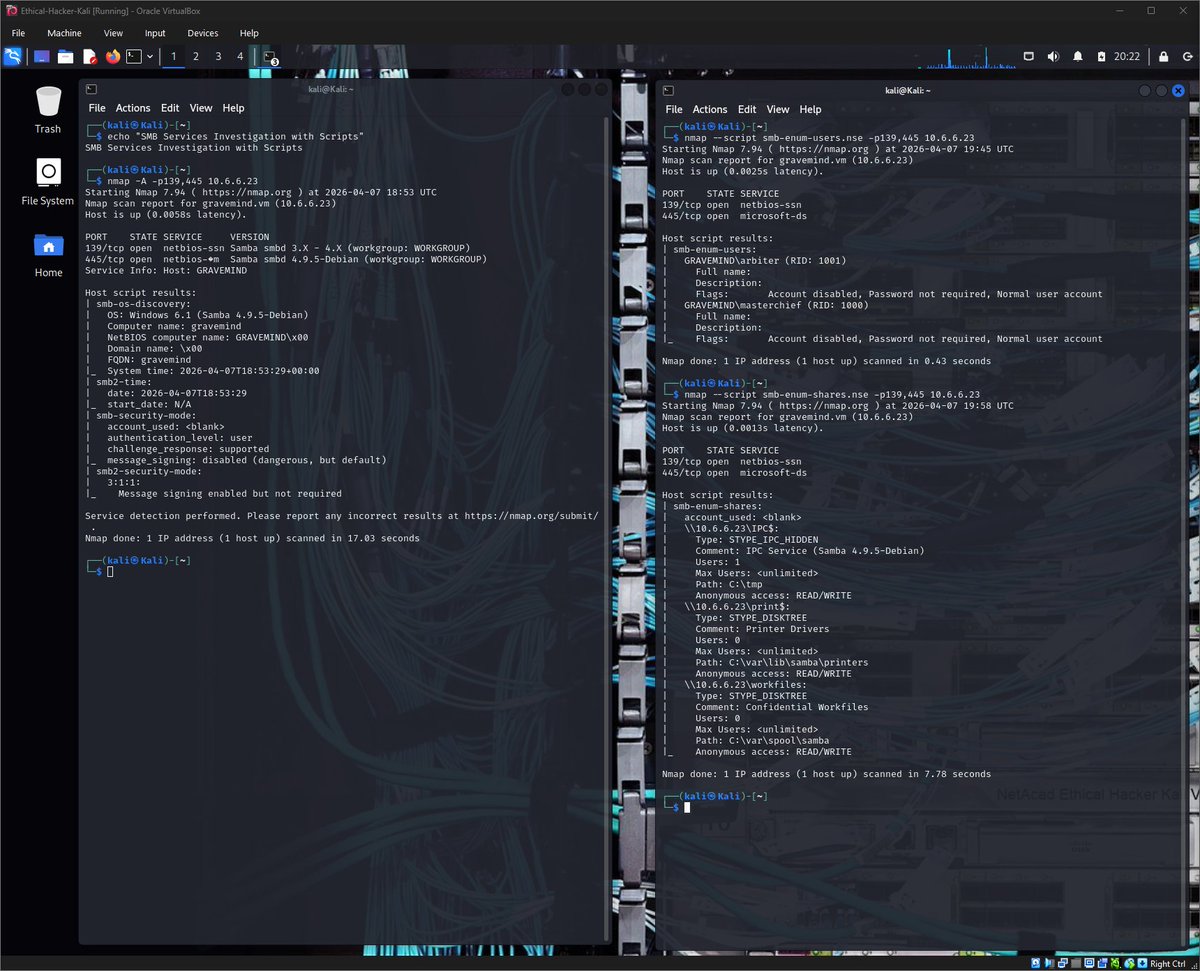
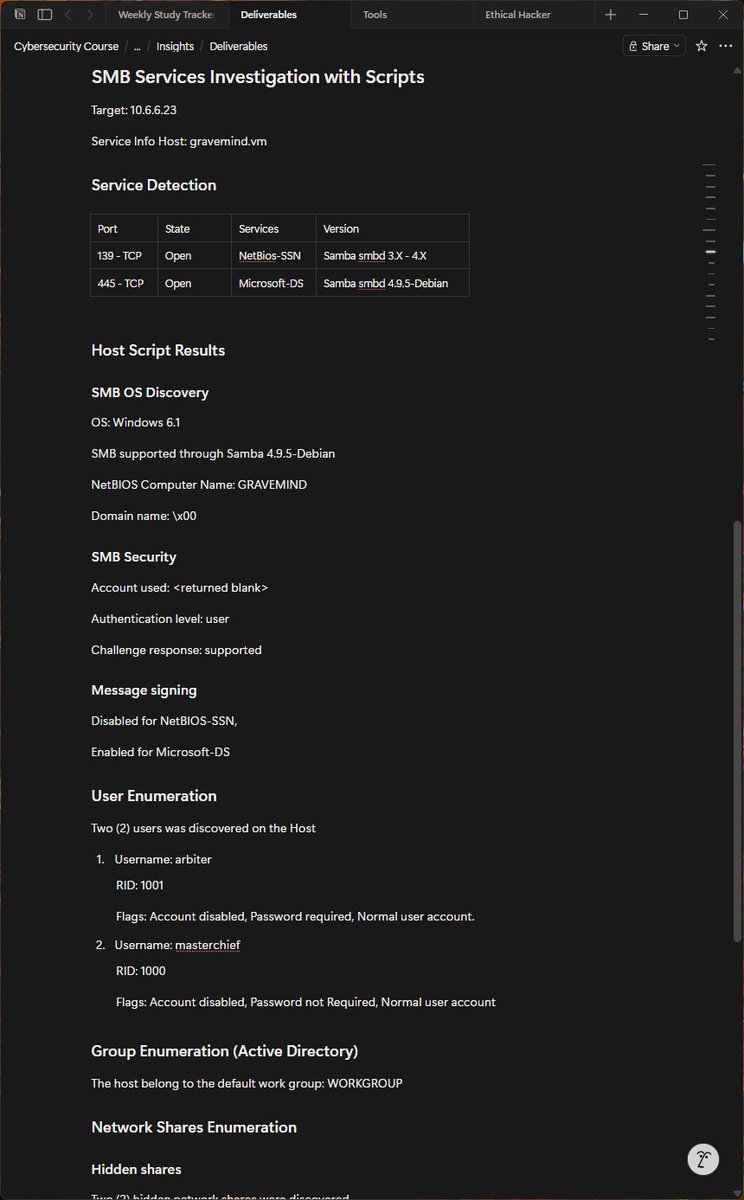
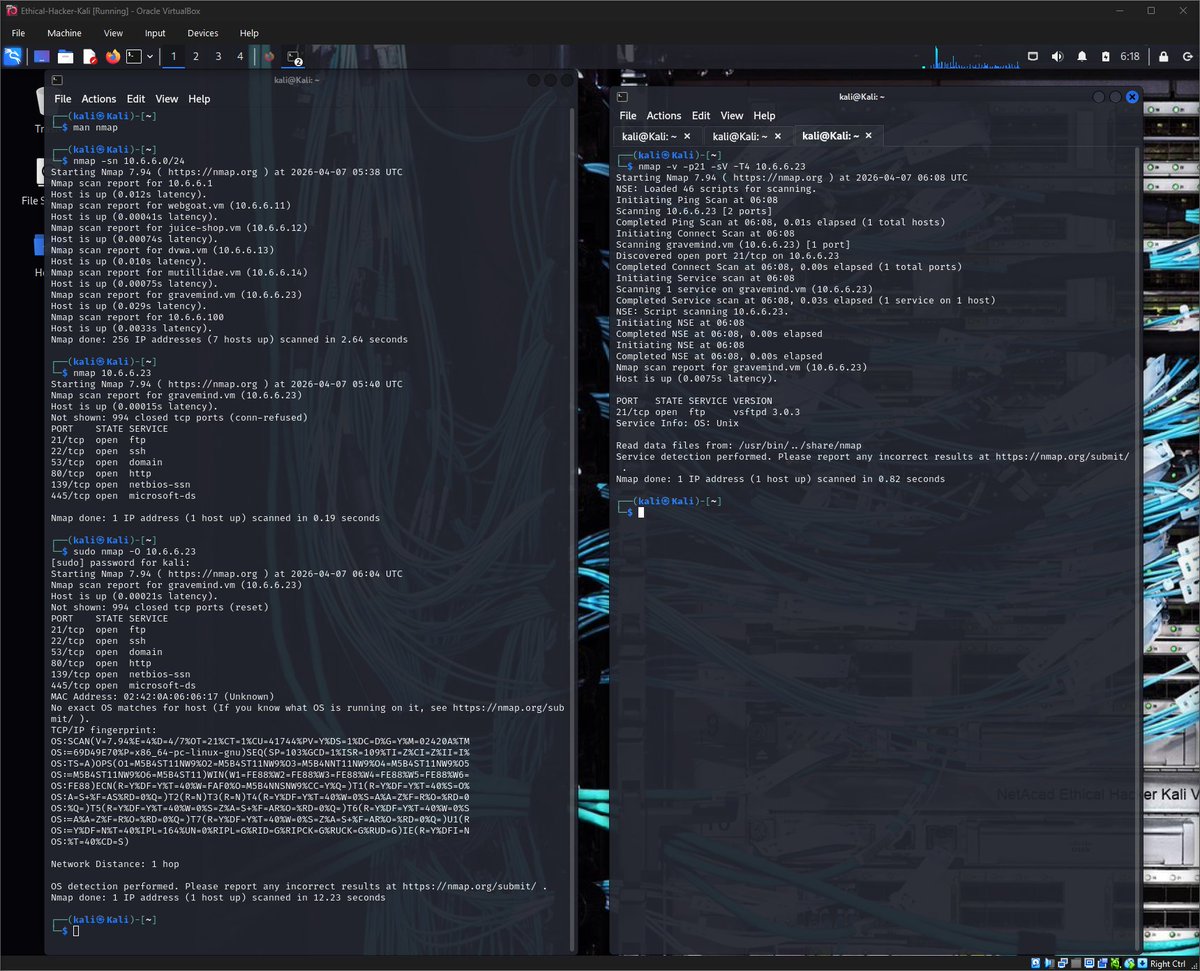
Day 93 - #100DaysOfCybersecurity 🔐
Today I completed a hands-on lab on Enumeration with Nmap, using active reconnaissance to investigate a suspicious host on a DMZ network.
Lab Scenario
A Wireshark capture showed unusual activity coming from a host on the 10.6.6.0/24 DMZ network.
My task was to use Nmap from a Kali Linux system to investigate the machine 10.6.6.23 and determine what services it was running and whether any vulnerabilities existed.
Key Activities Performed
🔎 Host Discovery
Using a ping scan:
nmap -sn 10.6.6.0/24
I identified 7 active hosts on the DMZ network.
🔌 Port Scanning
Running a default Nmap scan on the suspicious host:
nmap 10.6.6.23
Discovered open ports:
- 21 FTP
- 22 SSH
- 53 DNS
- 80 HTTP
- 139 NetBIOS
- 445 SMB
This immediately revealed a large attack surface.
🖥 Operating System Detection
Using OS detection:
sudo nmap -O 10.6.6.23
The target host was identified as running Linux.
⚙️ Service Version Enumeration
Using:
nmap -v -p21 -sV -T4 10.6.6.23
I discovered the FTP service running:
vsftpd 3.0.3 on a Unix system
📂 FTP Enumeration
Using a more aggressive scan:
nmap -A -p21 10.6.6.23
Findings:
- Anonymous FTP login allowed
- 4 files accessible through the FTP server
- FTP communication occurs in plaintext
🗂 SMB Enumeration
Scanning SMB services on ports 139 and 445 revealed:
- Samba service running
- NetBIOS computer name: GRAVEMIND
- Workgroup: WORKGROUP
Using Nmap NSE scripts:
smb-enum-users.nse: I discovered 2 user accounts
smb-enum-shares.nse: I identified 3 shared directories
Two shares were hidden, and anonymous users had READ/WRITE access, which is a major security risk.
Key Security Risks Identified
⚠️ Anonymous FTP login enabled
⚠️ FTP communication in plaintext
⚠️ SMB shares accessible with anonymous read/write access
⚠️ Multiple exposed services increasing the attack surface
Key lesson learnt from this lab:
Tools like Nmap are incredibly valuable for defenders, helping administrators discover devices, identify exposed services, and detect misconfigurations.
However, the same tools can be used by attackers during reconnaissance to map a network and identify potential entry points.
Understanding both perspectives is essential for building stronger defenses.
@jay_hunts @ireteeh @segoslavia
#Cybersecurity #EthicalHacking #Nmap #NetworkSecurity #PenTesting

English
Chimamaka Ukaga retweetledi

What Is a Nonce?
In cybersecurity, a nonce is a number used only once.
It is commonly used in authentication protocols to prevent replay attacks.
Here’s a simplified example:
1️⃣ A server sends a random nonce to a client
2️⃣ The client encrypts the nonce and sends it back
3️⃣ The server verifies the response
Because the nonce changes every time, previously captured messages cannot be reused.
This simple concept plays an important role in secure communication protocols and authentication systems.
#Networking #Infosec #LearningInPublic #LearningJourney
English
Chimamaka Ukaga retweetledi

Day 94 - #100DaysOfCybersecurity
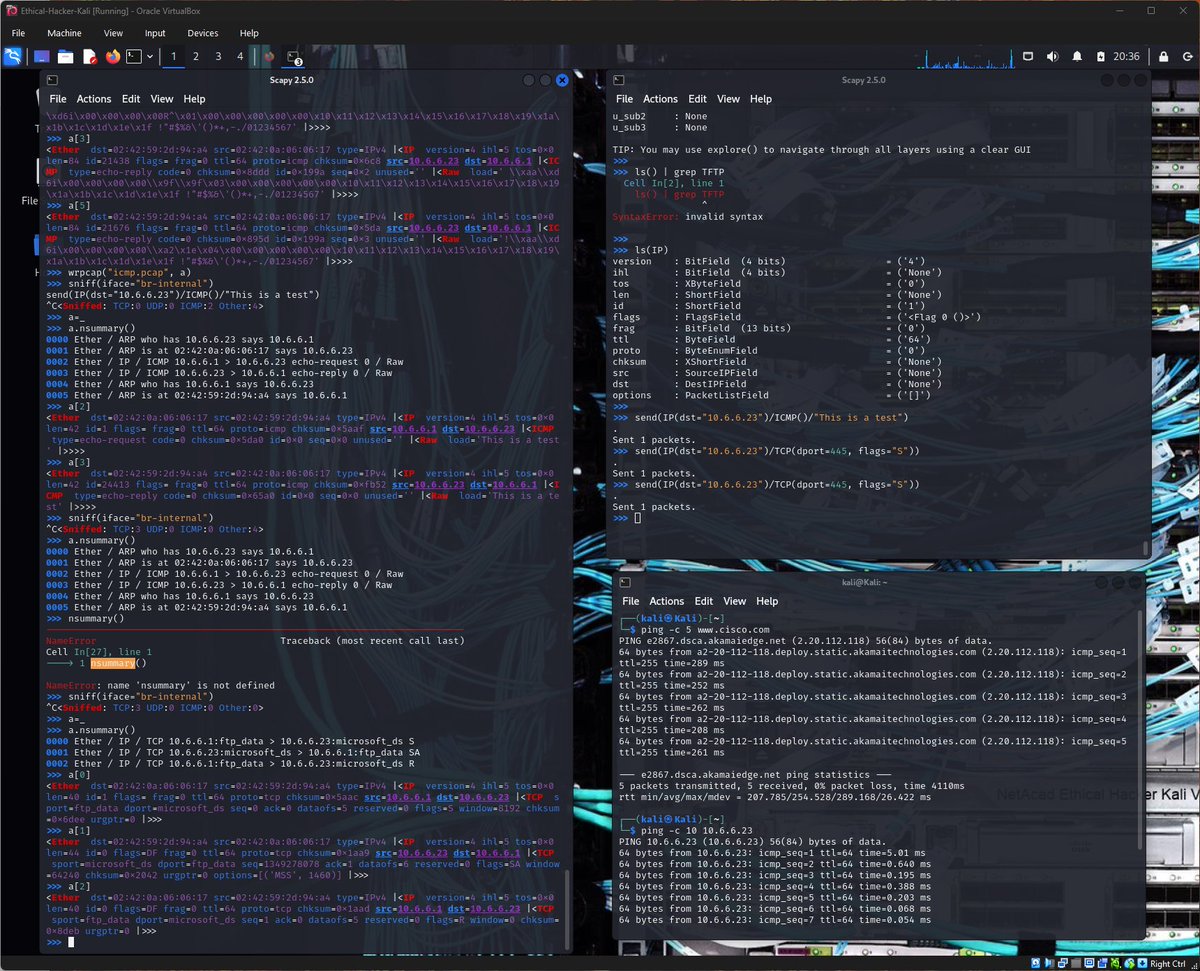
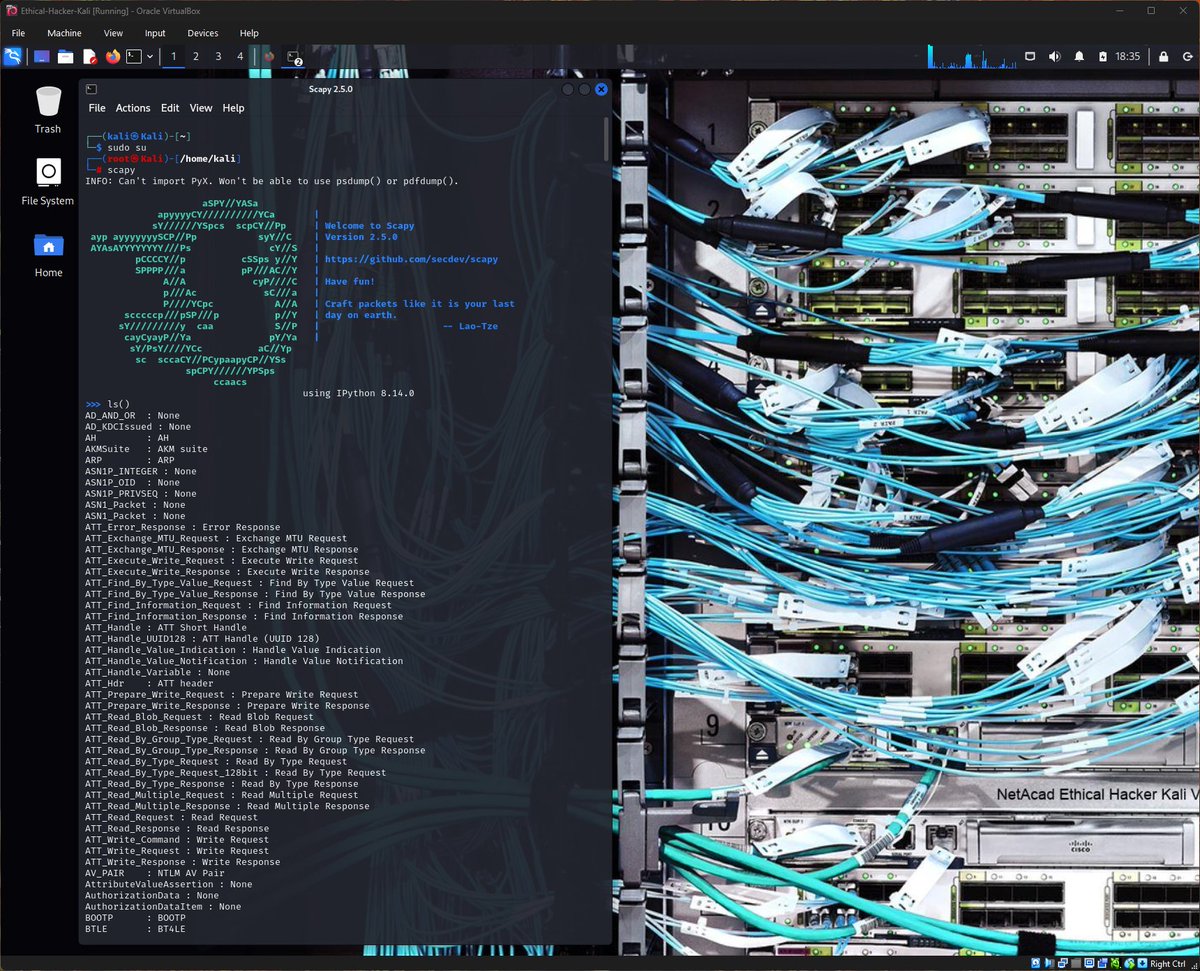
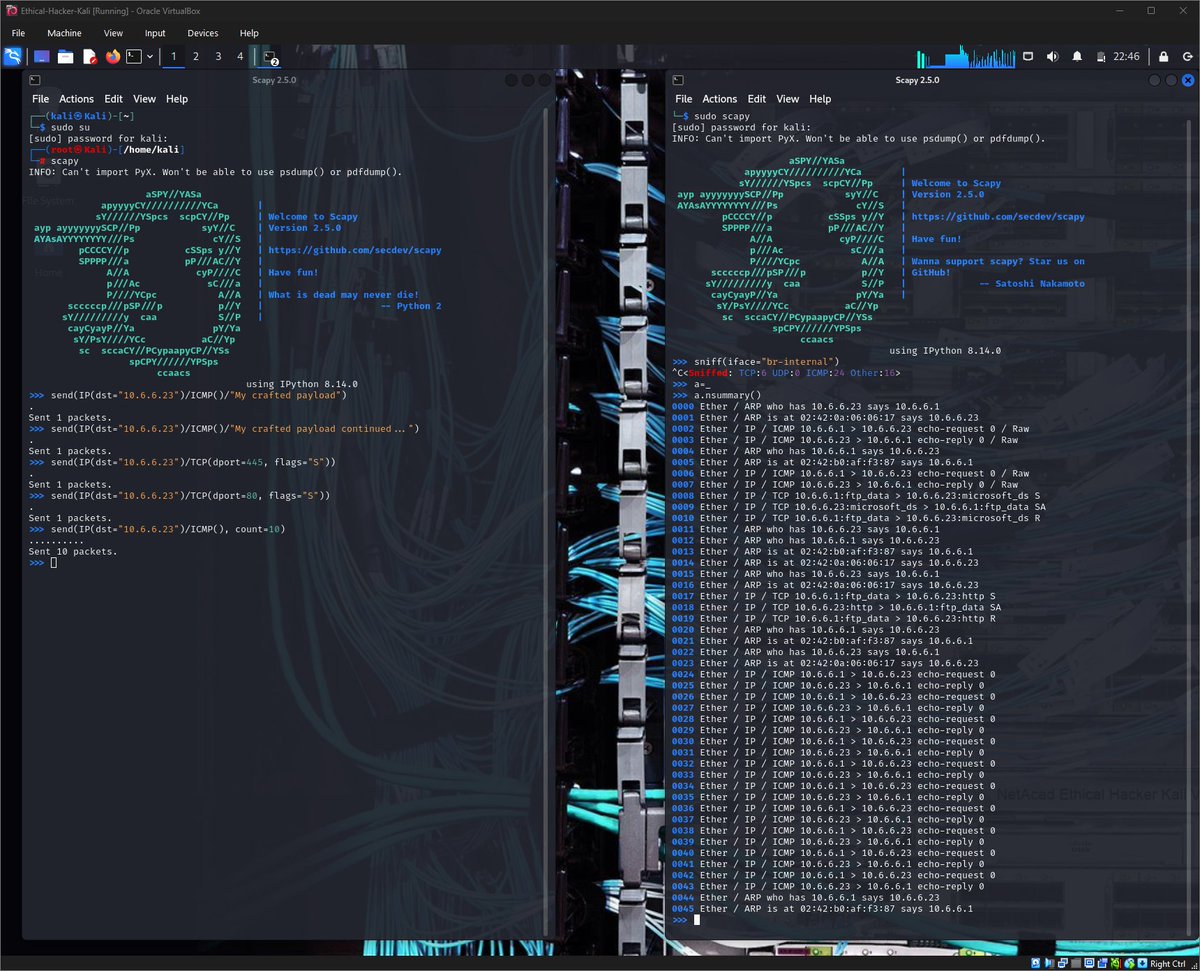
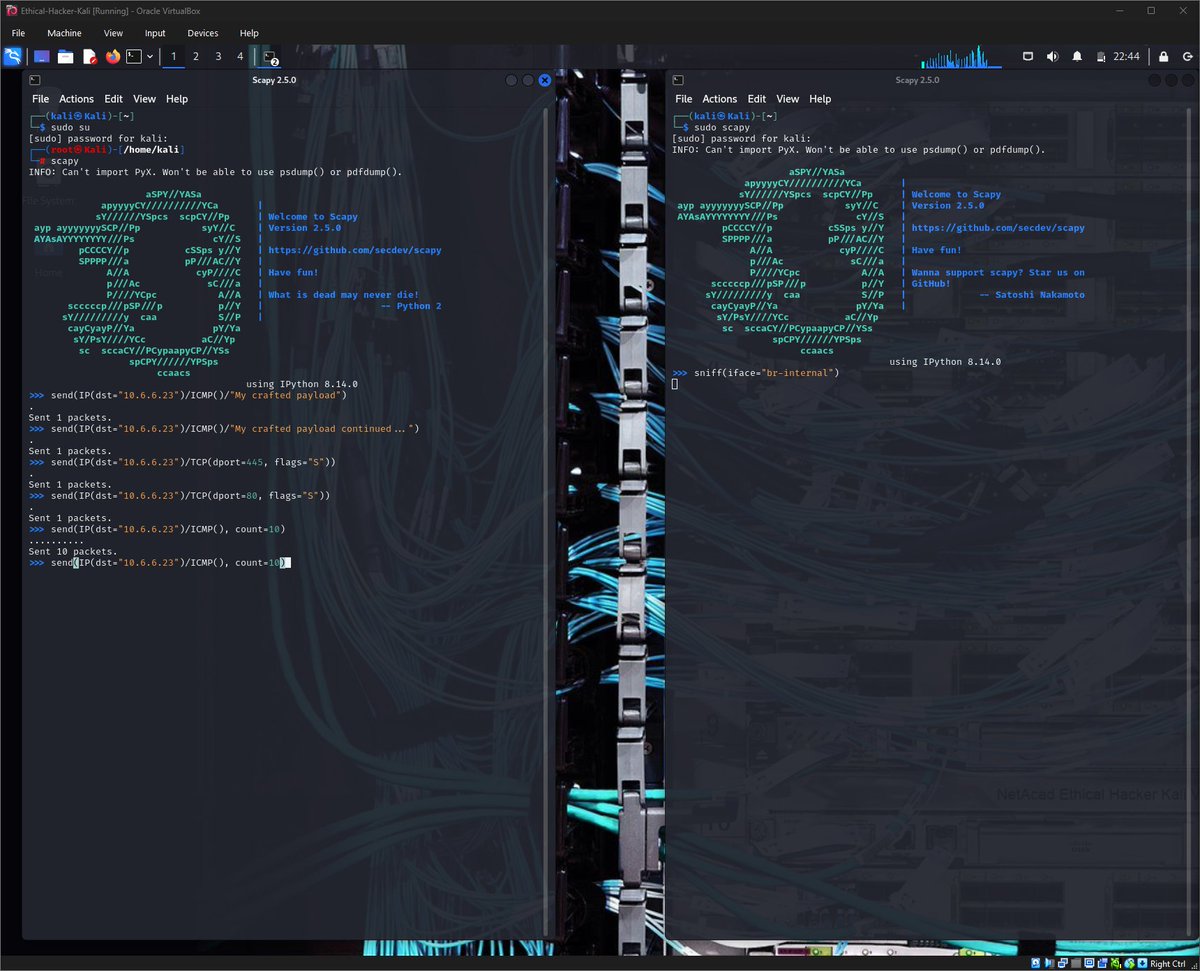
Today I completed a hands-on lab on Packet Crafting with Scapy, a powerful Python-based packet manipulation tool used by penetration testers and security researchers.
Unlike traditional scanners, Scapy allows you to manually craft, send, sniff, and analyze packets, making it extremely useful for reconnaissance, testing network behavior, and security research.
Activities I carried out:
🔎 Exploring Scapy
I started by launching Scapy in interactive mode and exploring its capabilities.
Using the ls() function, I viewed the large list of supported protocols and packet formats.
For example, Scapy supports 9 different TFTP packet formats.
TFTP is a useful protocol used to send and receive files on a LAN segment.
I also examined the structure of an IPv4 packet header using:
ls(IP)
This revealed important packet fields such as:
- TTL (Time To Live)
- Source and Destination IP addresses
- Protocol field (ICMP, TCP, UDP)
- Header checksum
Understanding these fields is essential when crafting custom packets.
📡 Sniffing Network Traffic
Next, I used Scapy’s sniff() function to capture traffic on the internal network interface.
Example:
sniff(iface="eth0")
I generated traffic by pinging a host and then reviewed the captured packets using:
- summary() function for native view, and
- nsummary() for number line view
I also filtered traffic to capture only ICMP packets and saved the capture to a .pcap file using:
wrpcap("icmp.pcap", a)
'a' is the variable I used to store the output of the sniff() function
Then, I used Wireshark to open the pcap for deeper analysis.
📦 Crafting a Custom ICMP Packet
I created and sent a custom ICMP packet to the target host 10.6.6.23.
Example:
send(IP(dst="10.6.6.23")/ICMP()/"This is a test")
The packet capture confirmed both the ICMP echo-request and echo-reply, and I observed that the crafted packet contained my custom payload in the raw data field.
🔌 Crafting a TCP SYN Packet
Finally, I crafted a TCP SYN packet to test whether port 445 (SMB) was open on the target system.
Example:
send(IP(dst="10.6.6.23")/TCP(dport=445, flags="S"))
The response returned a SYN-ACK (SA) flag, confirming that port 445 was open.
Key lessons I learned from this lab:
- Scapy is Python based and run in an interactive command mode.
- It allows deep control over packet creation and analysis.
- Packet crafting can reveal how systems respond to specific network interactions.
- Custom packets can be used for reconnaissance, testing firewall behavior, and identifying open services.
Understanding tools like Scapy helps to analyze networks at a much deeper level than traditional scanning tools alone.
@jay_hunts @ireteeh @segoslavia
#RedTeamer #Cybersecurity #EthicalHacking #Scapy #NetworkSecurity #PacketAnalysis

English
Chimamaka Ukaga retweetledi

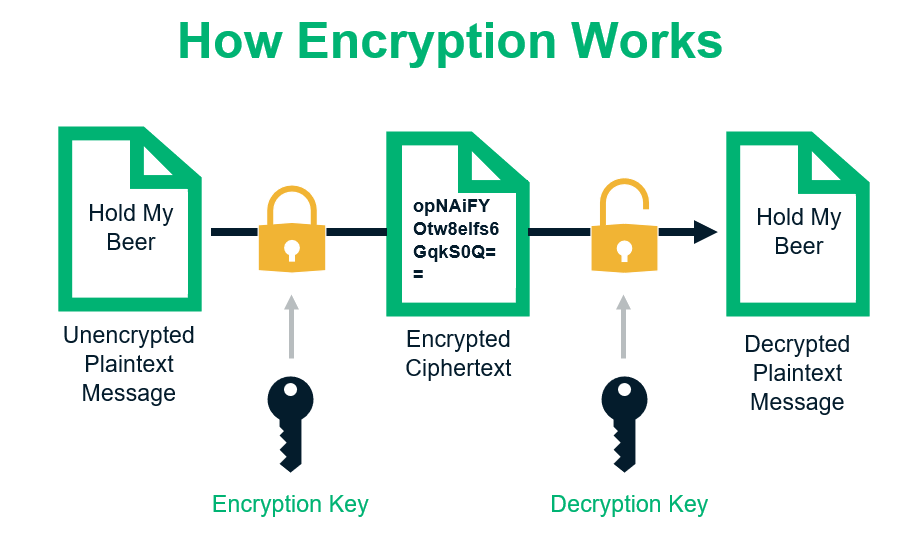
Understanding Encryption
Encryption is one of the core technologies that protects data on a network.
It works by transforming readable data (plaintext) into an unreadable format (ciphertext).
Only someone with the correct key can decrypt the data.
Encryption protects information in situations such as:
- Secure web browsing
- Online banking
- Messaging applications
- File storage
Without encryption, sensitive information like passwords and financial data could easily be intercepted during transmission.
This is why secure protocols like HTTPS have become the standard across the internet.
#Networking #Infosec #LearningInPublic #LearningJourney
English
Chimamaka Ukaga retweetledi

Day 95 - #100DaysOfCybersecurity
Today I joined my mentorship class session where our instructor walked us through Module 4 of the Ethical Hacker course: Social Engineering Attacks.
Social engineering focuses on manipulating human behavior rather than exploiting technical vulnerabilities, making it one of the most effective attack vectors in cybersecurity.
Topics We Covered in Today’s Session:
🎭 Pretexting for an Approach and Impersonation
We explored how attackers create believable scenarios (pretexts) to gain trust and extract sensitive information. This often involves impersonating trusted individuals such as IT staff, vendors, or executives.
🧠 Social Engineering Attacks
We discussed various forms of social engineering where attackers manipulate individuals into revealing confidential information or granting unauthorized access.
🚪 Physical Attacks
Social engineering is not limited to online interactions. Attackers may also exploit physical access vulnerabilities, such as tailgating into restricted areas, dumpster diving, shoulder surfing and badge cloning.
🛠 Social Engineering Tools
We looked at tools that attackers may use to automate or assist in social engineering campaigns, such as the Social Engineering Toolkit (SET).
🎯 Methods of Influence
One of the key aspects of social engineering is understanding human psychology. Attackers often rely on influence techniques such as authority, urgency, trust, fear, and curiosity to manipulate victims.
Lesson I learned from todays session:
Cybersecurity goes beyond securing systems, it’s also about protecting people from manipulation. Awareness and training are essential to help individuals recognize and resist social engineering attempts.
I am Grateful to our Instructor for the valuable insights shared during today’s mentorship session as I continue progressing through the Ethical Hacker course.
@jay_hunts @ireteeh @segoslavia
#RedTeamer #Cybersecurity #EthicalHacking #SocialEngineering #SecurityAwareness


English
Chimamaka Ukaga retweetledi

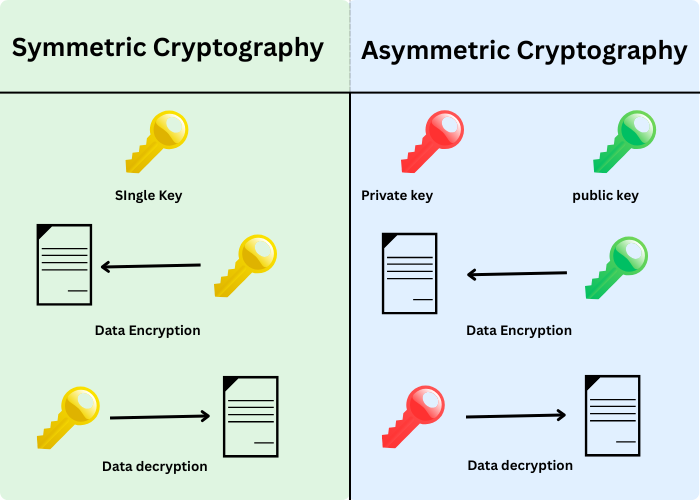
Symmetric vs Asymmetric Encryption
There are two main types of encryption used in cybersecurity.
Symmetric Encryption
- Uses a single shared key
- Faster and efficient for large amounts of data
- Both sender and receiver use the same key
Asymmetric Encryption
- Uses two keys: a public key and a private key
- The public key encrypts data
- The private key decrypts it
Asymmetric encryption is often used during secure communications to exchange keys safely.
After the secure exchange, symmetric encryption is typically used for the rest of the session.
Both approaches play important roles in modern cryptographic systems.
#Networking #Infosec #LearningInPublic #LearningJourney
English
Chimamaka Ukaga retweetledi

Day 96 - #100DaysOfCybersecurity 🔐
Today I spent more time practicing packet crafting with Scapy, reinforcing what I learned from my previous lab and gaining more hands-on experience manipulating network packets.
Scapy is a powerful Python-based tool that allows you to craft, send, sniff, and analyze packets, making it very useful for network reconnaissance and testing system responses.
What I Practiced Today
📡 Crafted and Sent ICMP Packets
I sent multiple custom ICMP packets to observe how the target host responds to crafted echo requests and to better understand ICMP packet behavior.
🔌 TCP SYN Packet Crafting
I also crafted TCP SYN packets to test specific ports on the target system:
- Sent SYN packets to Port 445 (SMB)
- Sent SYN packets to Port 80 (HTTP)
By analyzing the responses, I could determine whether the ports were open based on the TCP flags returned by the target host.
🔎 Packet Sniffing and Analysis
Using Scapy’s sniffing capabilities, I captured and analyzed the packets generated during these tests. This helped me observe:
- The request and response packet flow
- TCP flag responses from the target host
- The structure of the crafted packets
Hands-on practice with tools like Scapy helps build a deeper understanding of how network protocols behave and how systems respond to crafted packets during reconnaissance.
Continuing to explore packet-level interactions is helping me better understand network security from both an attacker and defender perspective.
@jay_hunts @ireteeh @segoslavia
#Cybersecurity
#Scapy
#PacketCrafting
#NetworkSecurity
#EthicalHacking
English
Chimamaka Ukaga retweetledi

Diffie-Hellman Key Exchange Explained
Secure communication often requires two parties to agree on a shared encryption key.
One method used for this is Diffie-Hellman key exchange.
The interesting part is that the key can be established over an insecure network.
The process works roughly like this:
1️⃣ Both parties agree on shared public values
2️⃣ Each party generates a private secret
3️⃣ They exchange computed values based on those secrets
4️⃣ Both sides independently derive the same shared key
Even if someone intercepts the exchange, they cannot easily compute the shared secret.
You can combine secrets in public, but only the original participants can reconstruct the final shared secret.
This concept forms the basis of many secure communication protocols.
#Networking #Infosec #LearningInPublic #LearningJourney

English
Chimamaka Ukaga retweetledi

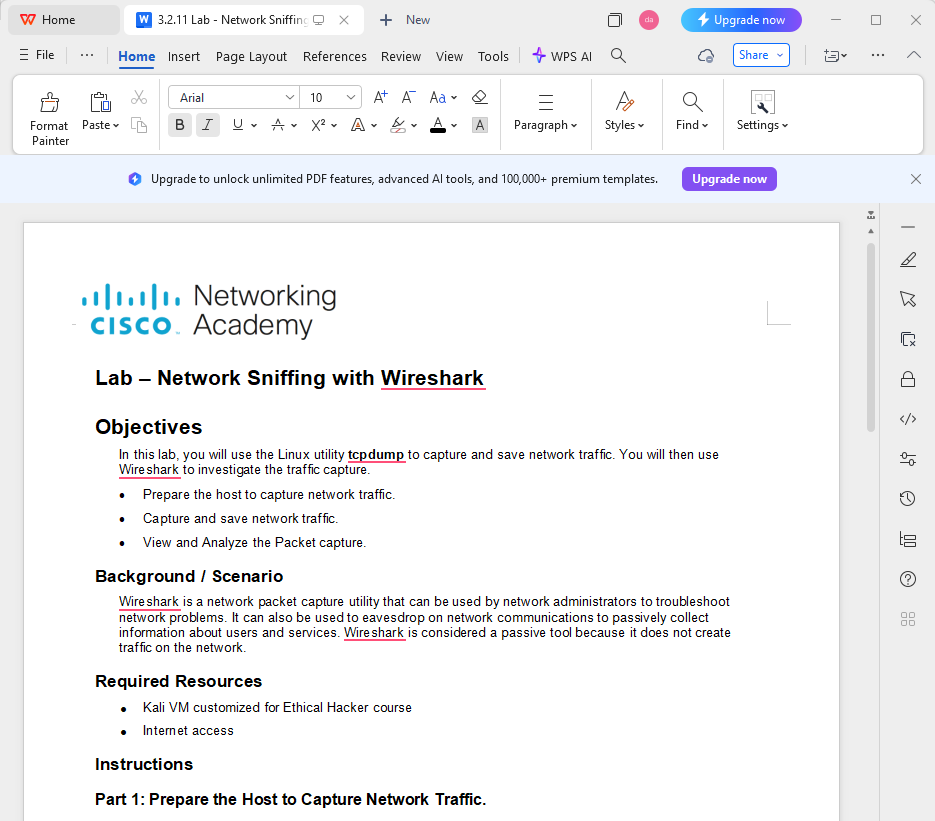
Day 97 - #100DaysOfCybersecurity
Let the countdown begin: 3 more days to go 🥳
Today I completed a hands-on lab on Network Sniffing with tcpdump and Wireshark, focusing on capturing and analyzing real network traffic for passive reconnaissance.
This lab reinforced how powerful packet capture tools are for observing network behavior without actively interacting with the target.
What I Did
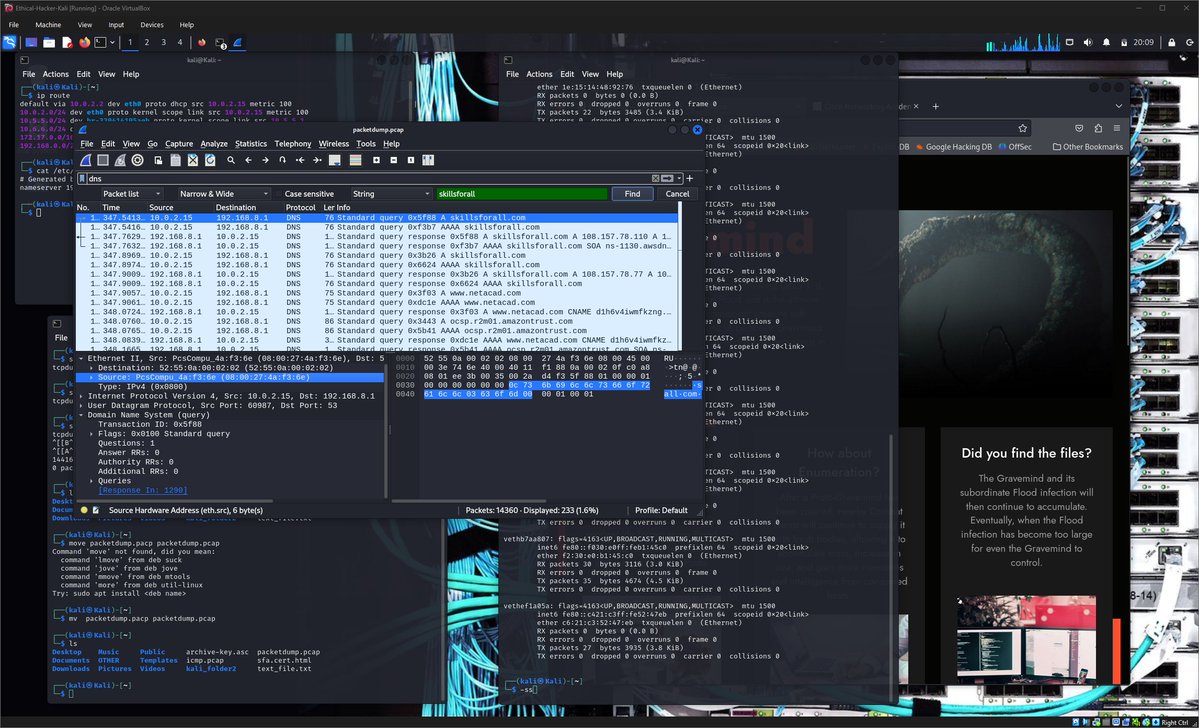
📡 Captured Network Traffic with tcpdump
I used tcpdump to capture live traffic on my Kali machine:
sudo tcpdump -i eth0 -s 0 -w packetdump.pcap
- Identified my interface details (IP, MAC, gateway, DNS)
- Captured traffic while browsing websites
- Saved the capture as a .pcap file for analysis
🔍 Analyzed Traffic with Wireshark
I opened the capture in Wireshark and filtered specific protocols to extract useful information.
🌐 DNS Analysis
By filtering dns traffic, I was able to observe:
- Websites visited (e.g., skillsforall, netacad, shodan)
- DNS queries and corresponding responses
- IP addresses associated with domains
Example insight:
skillsforall.com resolved to multiple IPs:
52.201.76.103
18.209.186.5
This shows how DNS can reveal user activity and browsing behavior.
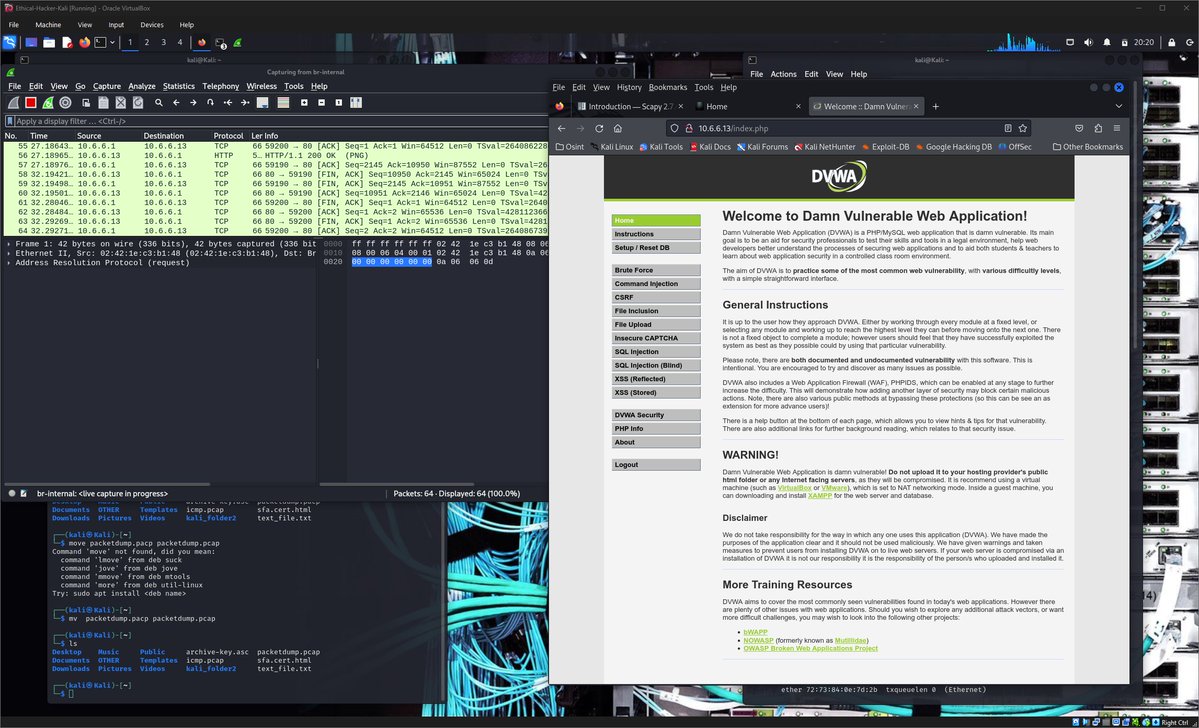
🌍 HTTP Session Analysis (DVWA Lab)
I captured and analyzed an HTTP login session on a test web app.
Key findings:
- POST request contained login credentials + user token (in plaintext)
- Server responded with a session cookie:
PHPSESSID=...
- The same session ID was sent back in subsequent requests
This demonstrates how unencrypted HTTP traffic exposes sensitive data, making it vulnerable to interception and session hijacking.
Key lessons I learnt in the lab:
- Packet sniffing tools enable stealthy (passive) reconnaissance
- DNS traffic reveals browsing patterns and infrastructure details
- HTTP traffic can expose credentials and session cookies in plaintext
- Packet analysis is critical for both defense and attack understanding
This lab really highlights why encryption (HTTPS) and secure configurations are essential in modern networks.
@jay_hunts @ireteeh @segoslavia
#RedTeamer #Cybersecurity #Wireshark #tcpdump
#NetworkSecurity #PacketAnalysis #EthicalHacking

English