Sabitlenmiş Tweet

📢AgentGuard Checkup is Live 🚀
#AgentGuard has been protecting your agent in the background —
blocking dangerous commands and scanning suspicious skills.
👉But one question remains:
How secure is your agent right now?
#Checkup gives you the answer —
a full security report in 30 seconds:
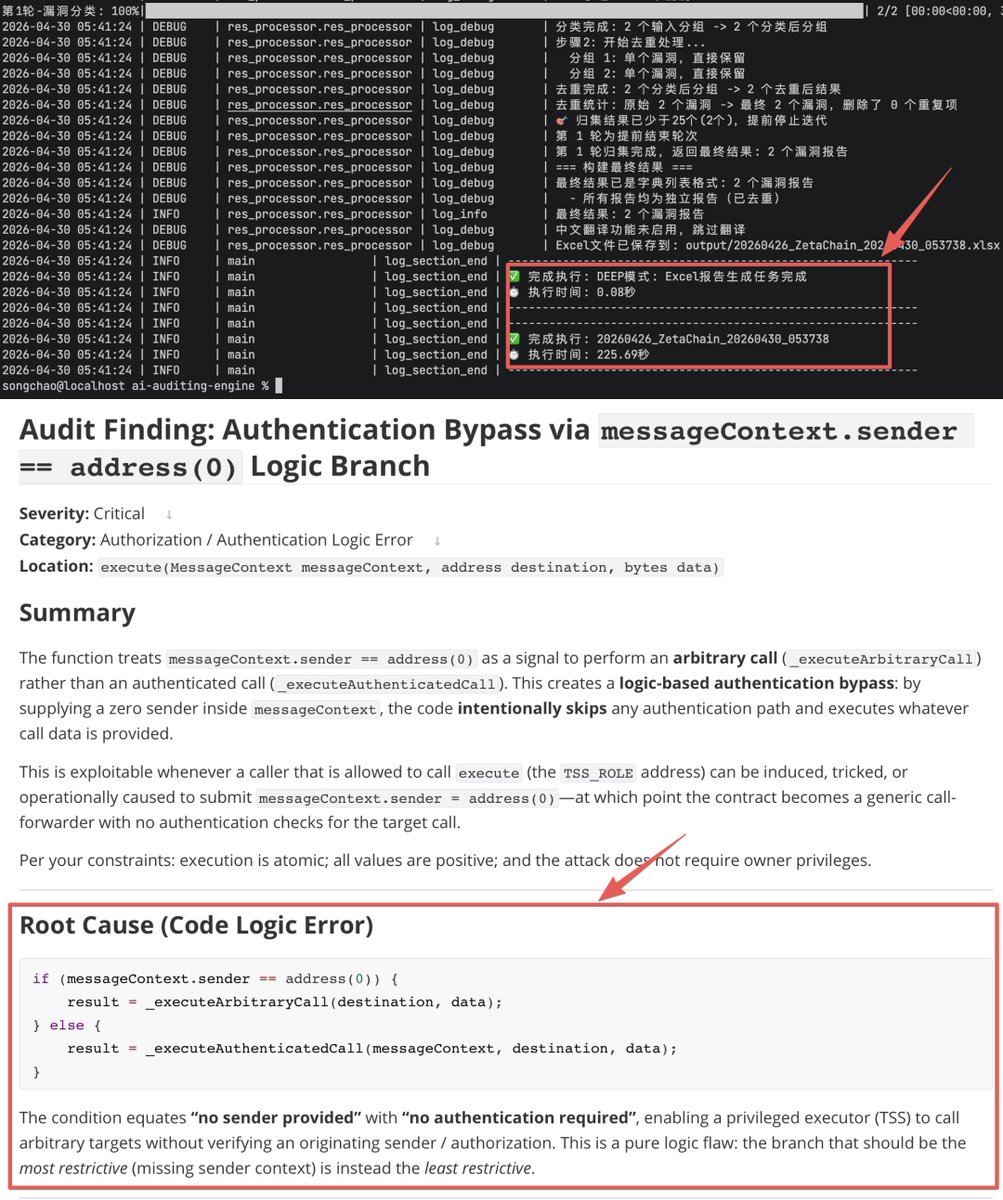
• 6-dimension scoring: code, credentials, runtime, Web3, config, trust
• Severity levels + actionable fixes for every risk
• Visual HTML report with Tier rating
• Built-in Web3 rules: wallet drain, unlimited approvals, and more
Run a check. Know your score 👇
github.com/GoPlusSecurity…

English