Sabitlenmiş Tweet
Olúwatóbi
54 posts


Olúwatóbi
@Grandis_02
Christian || Medical student @ibadanmedicine || Chess || Anime
Katılım Ocak 2025
409 Takip Edilen55 Takipçiler
Olúwatóbi retweetledi

Graffiti project for @abh_parrot is officially live! 🎨🚀
Huge shoutout to the talented @Grandis_02 We had a blast bringing this vision to life.
Spread the word and hit the DMs for commissions!
TheFree did it again. 👨🏽⚕️🔥


English
Olúwatóbi retweetledi

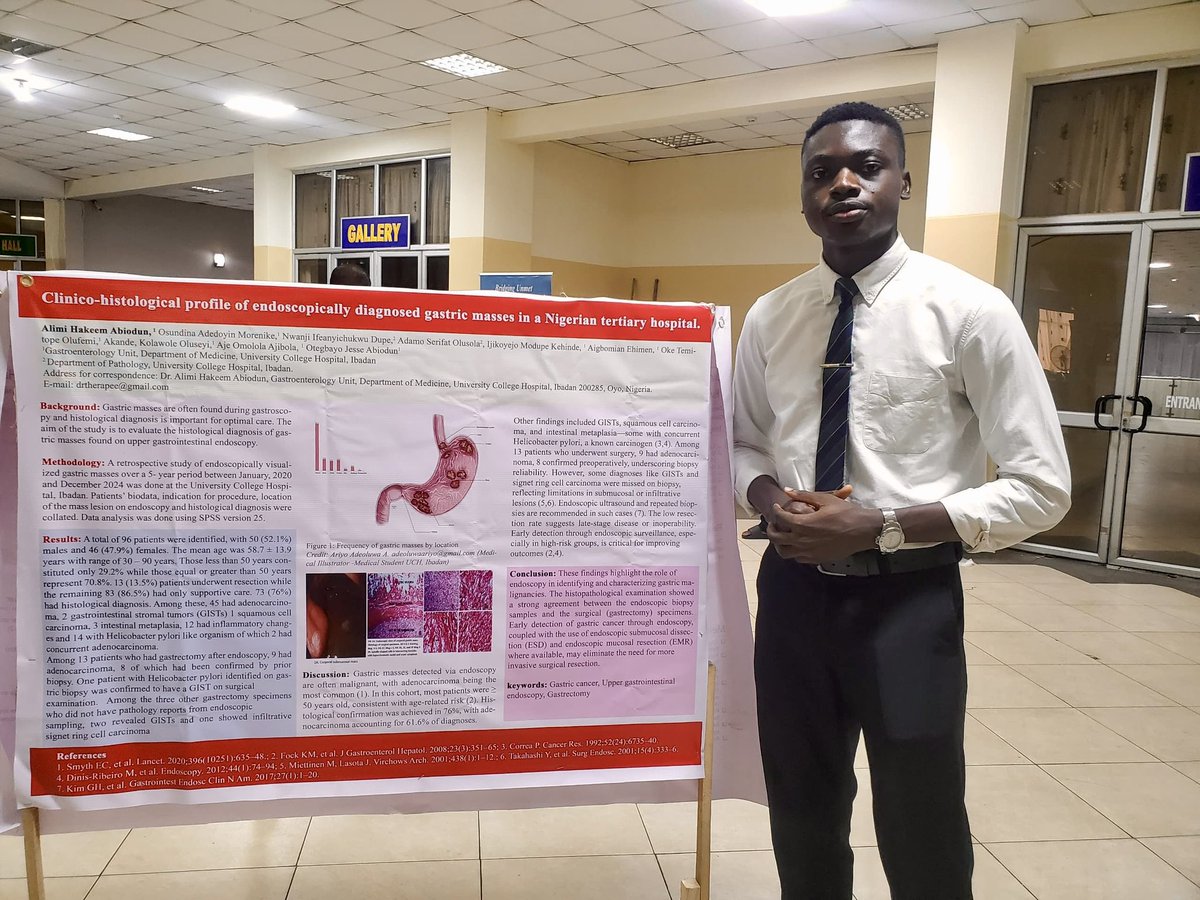
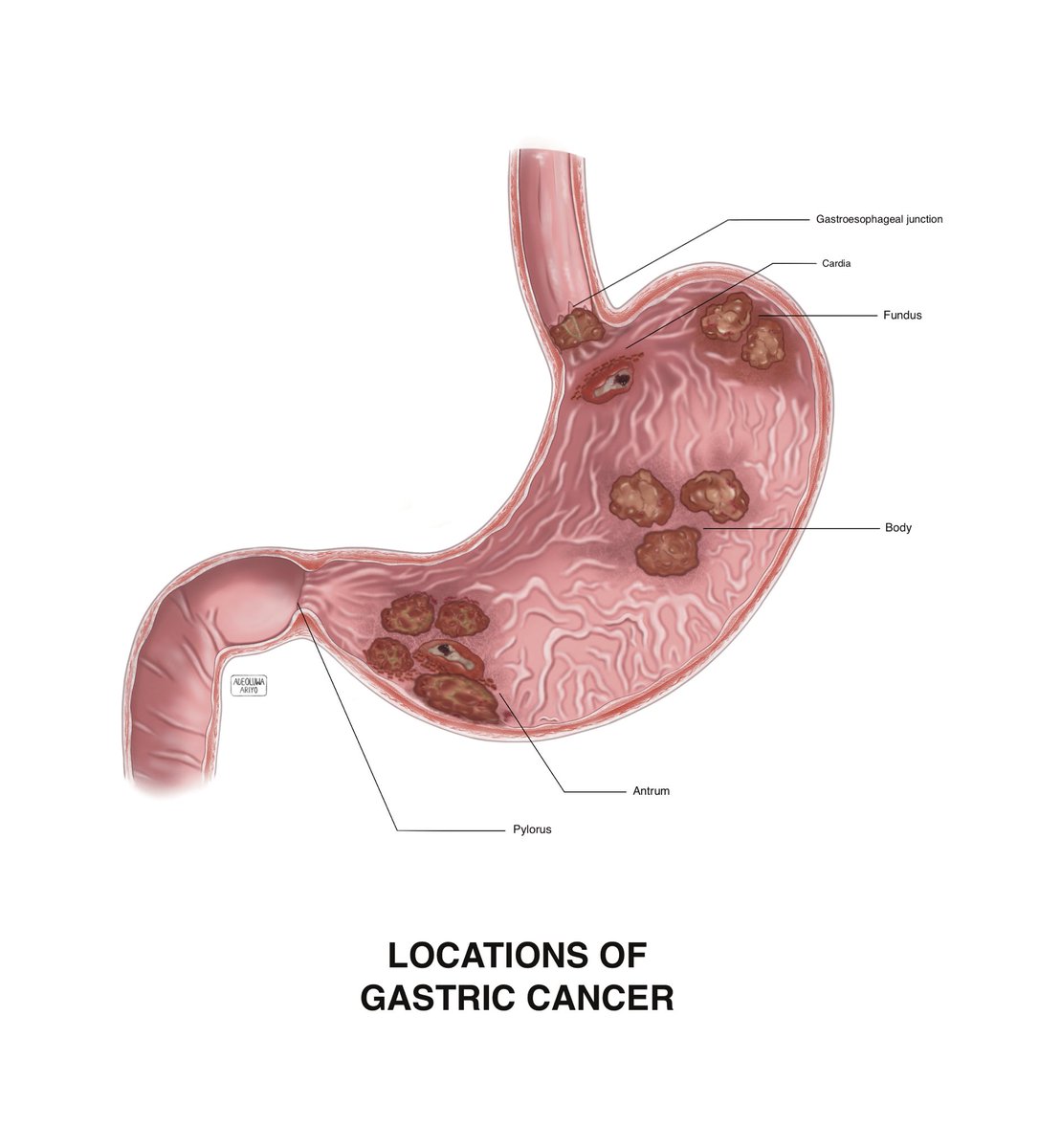
Reaching out to all #MedTwitter . High-quality research deserves high-quality visualization. I create Medical Illustrations professionally and I am dedicated to helping researchers and clinicians bridge the gap between complex subjects and visual clarity.
linktr.ee/adeoluwaariyo
English

What can I say, I'm an old man 🫠
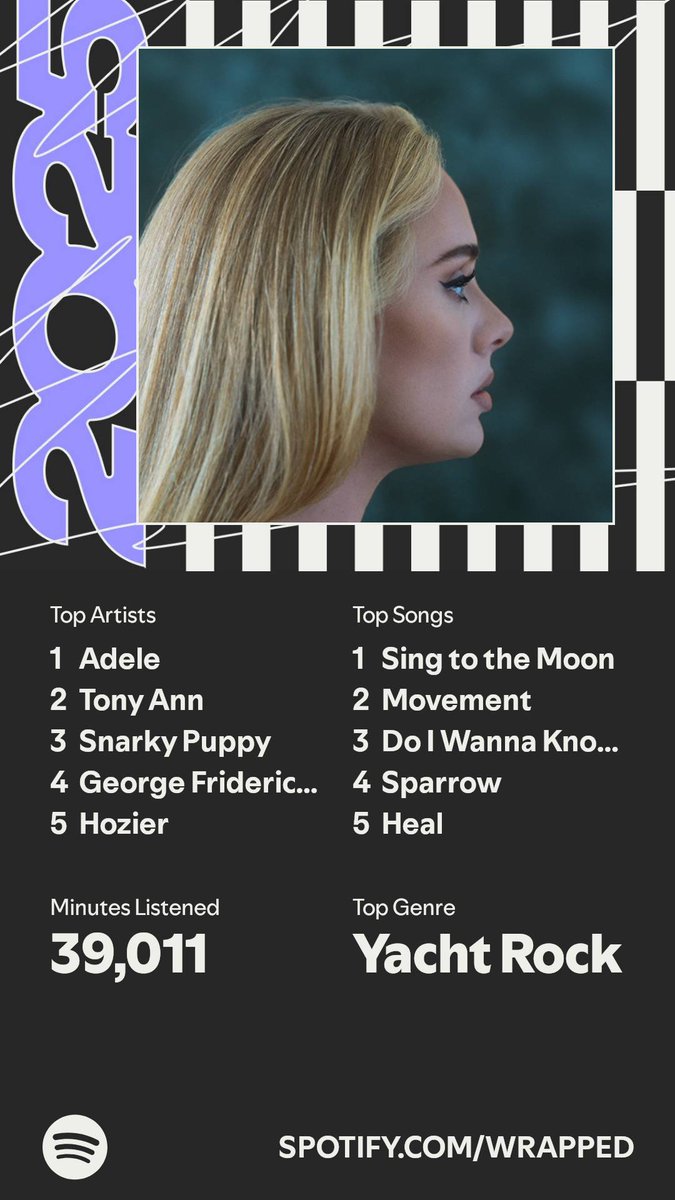


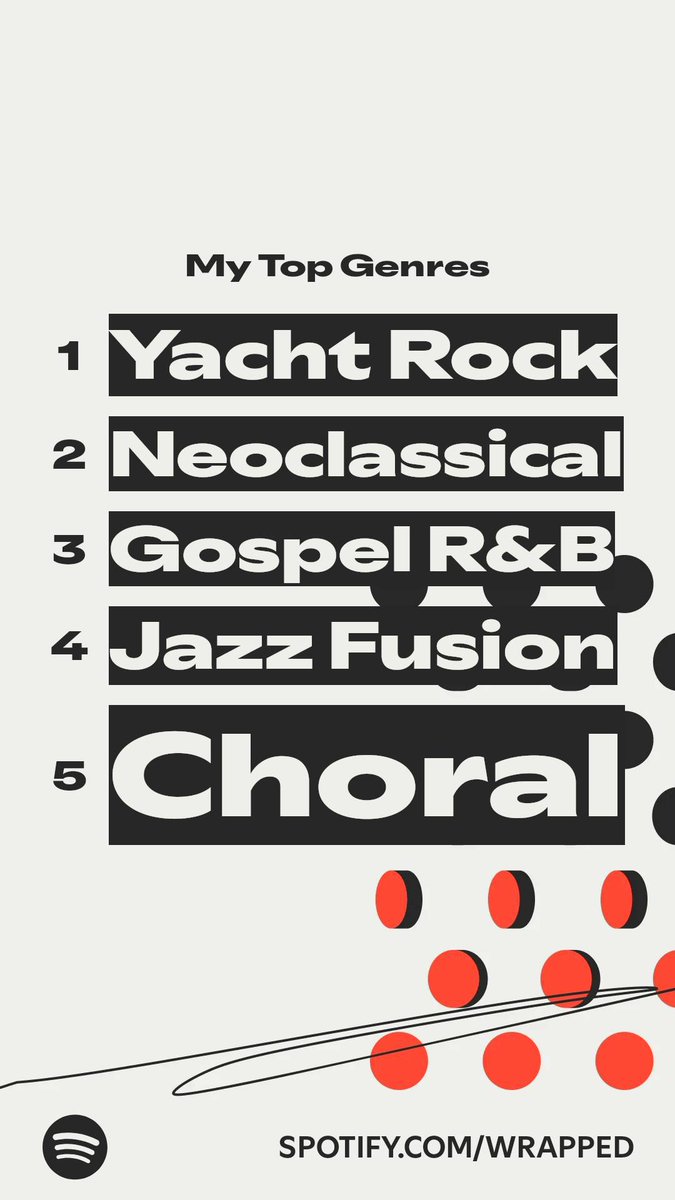
Akaza@Akaza_Web3
quote this tweet with your Spotify Wrapped for 2025! #SpotifyWrapped
English
Olúwatóbi retweetledi

For generations, the act of running was like carrying a giant, empty bucket under a waterfall.
you put in endless effort — miles of sweat, grit, and burning lungs but at the end of the day, all you had was a fleeting sense of accomplishment and a load of wet laundry.
the world accepted that the financial value of a successful running routine was zero.
then came Runwago, and everything changed. 🧵
@runwago |@scribble_dao | #WWF
English
Olúwatóbi retweetledi
Olúwatóbi retweetledi

MYTH:-. Primary teeth are not permanent, so you do not need to take care of them.
FACT:-. Primary teeth are the ones that hold space for adult teeth growing in the jaw. If a primary tooth falls out too soon, other teeth in the mouth will try to move into that space and block the permanent tooth from coming in properly. This can lead to crowding and bite misalignment. Therefore, establishing dental habits at an early age helps ensure the safe development of adult teeth.
Tooth Boy@tooth_boy_
DENTAL STUDENTS; Quote this tweet by BUSTING ONE DENTAL MYTH to educate the public. Whoever has the highest number of RTs on their post by 8pm tomorrow wins 20k. 👍🏾
English
Olúwatóbi retweetledi
Olúwatóbi retweetledi
Olúwatóbi retweetledi

In the summer of 2017, the financial world faced a wake-up call it could not ignore. Equifax, one of the largest credit reporting agencies in the world and the gatekeeper of highly sensitive personal financial data, suffered a breach that exposed the identities of nearly 150 million Americans, along with millions of UK and Canadian citizens.
It was a catastrophic event with real-world consequences. For months, hackers roamed Equifax’s systems, siphoning off a treasure trove of data: names, Social Security numbers, birth dates, home addresses, and in some cases, driver’s license and credit card numbers. This was the kind of data cybercriminals dream of. Everything needed to impersonate individuals, open fraudulent accounts, and wreak havoc on lives for years to come.
The Anatomy of the Equifax Breach
The timeline of the breach revealed a perfect storm of negligence and outdated security practices. Between May and July 2017, attackers exploited a known vulnerability in Apache Struts, a popular web application framework. A patch for this flaw had already been available, but Equifax hadn’t applied it. That single oversight opened the front door for attackers.
Once inside, the hackers didn’t stop. They moved laterally through Equifax’s internal network, locating databases filled with sensitive consumer information. Even worse, they found unencrypted credentials and accessed the data in its most vulnerable state: plaintext, fully readable and ready to steal.
Equifax did encrypt data “at rest” (stored on servers) and “in transit” (moving across networks).
But like many companies, its data-in-use, the data being actively processed on servers, was unprotected. Any query or report that required sensitive information decrypted it in memory. The hackers didn’t have to break the encryption; they simply waited for the data to be processed and then exfiltrated it.
It was a systemic failure of the traditional “castle-and-moat” security model, where companies focus on building a strong perimeter and assume that everything inside can be trusted. In a world of sophisticated cyberattacks, that assumption is fatally flawed.
Why Traditional Security Fails
The Equifax breach highlights a fundamental weakness in conventional data protection:
- Encryption only works part of the time. Data is encrypted when stored or transmitted, but must be decrypted for use.
- Once attackers are inside, the data is theirs. Lateral movement within a network is enough to access plaintext data in memory.
- Trust is a liability. Companies must trust their infrastructure, employees, and every tool that touches the data.
This creates an “Achilles’ heel” in cybersecurity: the data-in-use stage, where sensitive information exists unencrypted in memory. Any breach of the internal environment can expose it.
Equifax learned this the hard way. But emerging technology, like Arcium’s confidential computing network, offers a fundamentally different approach that could have prevented this disaster.
How Arcium Could Have Saved Equifax
Arcium represents a new paradigm in data security: data-centric protection that secures information throughout its entire lifecycle—at rest, in transit, and crucially, in use.
Here’s how the 2017 breach might have unfolded if Equifax had built its infrastructure on Arcium’s confidential computing network:
1. Data Never Exists as Plaintext
When consumer data entered Equifax’s systems, it would have been immediately encrypted using secure multi-party computation (MPC).
- The plaintext Social Security numbers, addresses, and credit card details would never exist on a traditional server.
- Even if hackers breached the entry point, they would see meaningless ciphertext, not usable data.
2. Computation Happens Inside Trusted Enclaves
When Equifax needed to run a credit check or generate a report, the request would be processed inside secure hardware-level enclaves on Arcium’s decentralised network.
- These enclaves allow computation on encrypted data without ever decrypting it to a readable state.
- ZK proofs and MPC ensure computations are verifiable and accurate without revealing the underlying data.
- Not even Equifax administrators or a hacker with full network access could see the plaintext data.
3. Only the Result Leaves the Enclave
The only thing returned from Arcium’s secure processing is the final result: a credit score, a yes/no verification, or a completed analytic report.
- Raw data never leaves the protected environment.
- A breach of the internal network would yield nothing but useless encrypted fragments.
4. A Breach Becomes Meaningless
In the real 2017 scenario, hackers exfiltrated 150 million sensitive records. Under Arcium’s model:
- Even with full access to Equifax’s systems, attackers would only obtain encrypted data with no decryption keys.
- They would be unable to perform queries or extract meaningful information.
- The breach would have been effectively neutralised before it began.
The Lesson for the Future
The Equifax breach is a cautionary tale: perimeter-based security is not enough. Data is most vulnerable when it is actively used, and traditional encryption fails to protect it at that stage.
By contrast, Arcium’s confidential computing network eliminates the “data-in-use” weakness, flipping the security model on its head. Instead of trusting the network and infrastructure, it trusts the cryptography and hardware to ensure that sensitive data never leaves its encrypted state.
If this model had been in place in 2017, 150 million people could have been spared years of anxiety, fraud risk, and identity theft. And Equifax could have avoided one of the most infamous breaches in history.
The future of cybersecurity is clear: protect the data itself, not just the walls around it.
gMPC☂️💜

English
Olúwatóbi retweetledi

Ethereum at 10: A Decade of Decentralised Dreams, Disruptions, and Destiny
Yesterday, July 30, 2025, marked a milestone that few technologies ever reach:
A 10th birthday.
Ethereum's 10th birthday.
Ten years since block 0.
Ten years since the "world computer" first booted up.
Ten years since a wild idea became the foundational layer of DeFi, NFTs, DAOs, RWAs, and everything in between.
From anonymous hackers to Ivy League institutions, from pixelated cats to billion-dollar treasuries. Ethereum has been the stage for it all.
So, how did we get here? What’s next?
Let’s rewind, fast forward, and explore a decade of Ethereum; the triumphs, the breakdowns, the breakthroughs and why its second decade might just be even bigger.

English
Olúwatóbi retweetledi

Yellow Network: The Infrastructure Layer Rewiring Crypto Trading
"Crypto trading is about to leave the stone age, and Yellow Network is the bridge to that future."
Despite over a decade of innovation, most cryptocurrency trading still occurs through centralized platforms with fragmented liquidity, opaque processes, and considerable counterparty risk. While DeFi offers alternatives, it often sacrifices performance, scalability, and usability.
Yellow Network emerges as a transformative solution. A Layer-3 decentralized clearing network designed to unify crypto trading across blockchains, exchanges, and protocols. Instead of building “just another exchange,” Yellow is building the infrastructure that can support the future of real-time, cross-chain, P2P trading at scale.
Walk with me into this thread as I take a deep dive into what @Yellow network is.

English
Olúwatóbi retweetledi
Olúwatóbi retweetledi
After 139 hours, 8 weeks and a million mental breakdowns, I am pleased to share my latest drawing of Leo's greatest moment 🏆
Hope you enjoy and share it with a Messi fan ❤️
#Messi𓃵 #fifaworldcup22

English

The Power of Partnerships: GSR’s Role in Katana’s Early Growth
While many DeFi chains struggle with the "cold start problem" no liquidity, no users, @katana avoids this pitfall thanks to its early backer: @GSR_io, one of the largest market makers in crypto.
GSR is committed to:
> Seeding liquidity in lending markets,
> Bootstrapping LP pools,
> Facilitating token swaps,
> Supporting the initial auction mechanics for Katana’s native token.
This level of institutional involvement from day one gives Katana deep liquidity, price stability, and trader confidence, setting a strong foundation for organic growth.
gKatana

English