

GrittyBlu
927 posts

@GrittyBluDragon
K12 Systems Engineer - Cybersecurity Specialist | Using this account to help myself and others learn about I.T. and cybersecurity











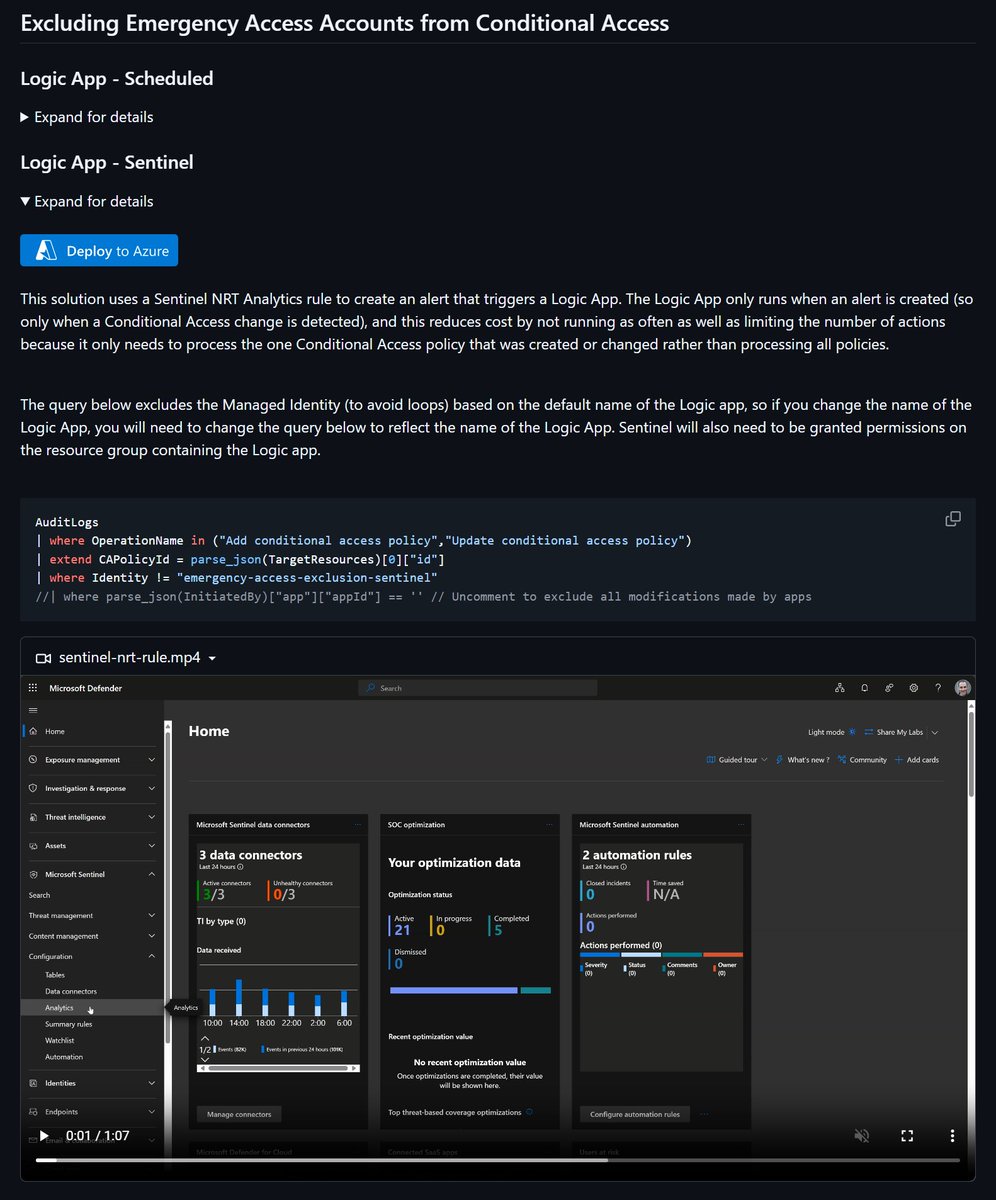
I've been working on a set of solutions around excluding emergency access accounts from CA policies to showcase when/why to use certain methods I just pushed the first option, Logic App using a sliding window, to my repo with a Deploy to Azure button :) github.com/nathanmcnulty/…




@jamieantisocial @HackingLZ @NathanMcNulty Is ChromeOS even real outside of schools? I think too many cyber bro's get all barred up that the world can move away from Windows in the enterprise/business - when the reality is that nothing else is even remotely ready for normies like my mother...







