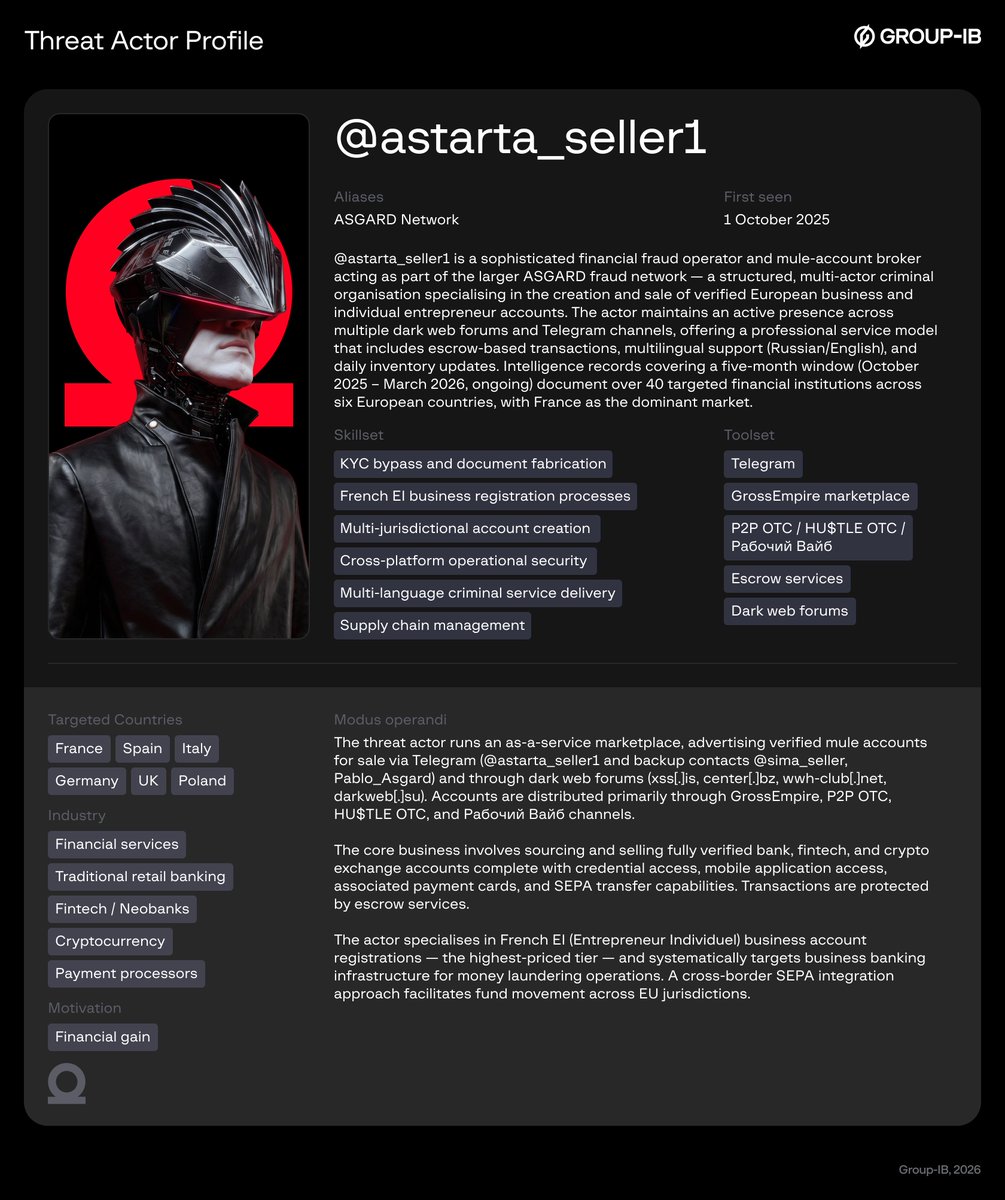
This Labor Day, the most dangerous hire isn't the one who failed the background check. It's the one who passed it.
DPRK-linked IT workers are infiltrating companies through legitimate hiring pipelines, earning salaries, and exfiltrating data from the inside. Group-IB researchers have mapped exactly how it works.
The numbers tell the story. Read the full blog here: bit.ly/4d3XzXX
#ThreatIntelligence #DPRK #InsiderThreat #Infosec #LaborDay #GroupIB


English