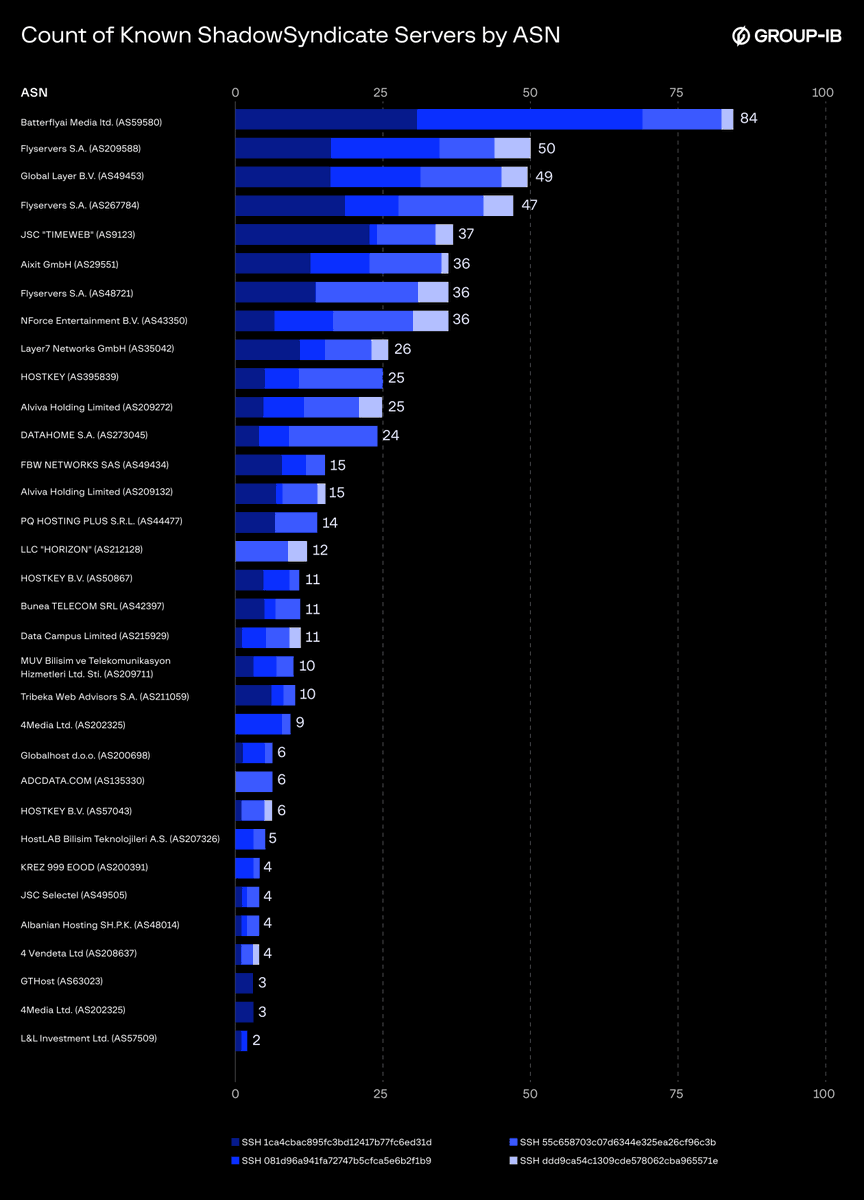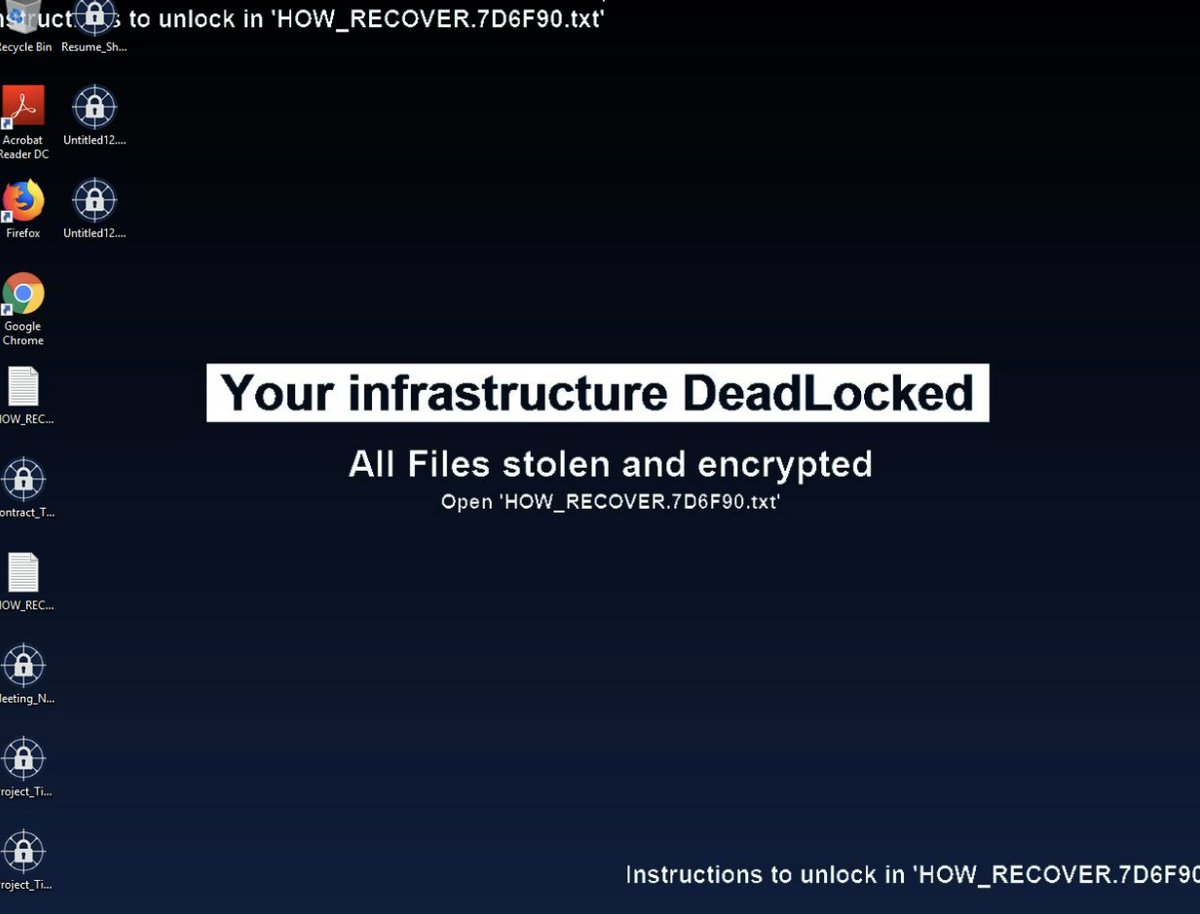
How do affiliates evolve into RaaS operators? The Gentlemen's playbook reveals a heavy focus on operational efficiency: weaponizing MeshCentral/AnyDesk for persistence, deploying password-protected executables via NETLOGON for domain-wide spread. Defend the #TTPs, not just the name. Read the full analysis here: link.group-ib.com/41defXc
English