GunningCrypto
921 posts


GunningCrypto
@Gunningcrypto
This crypto money got me feeling super if you know what I’m sayian. COYG🔴⚪️
Katılım Nisan 2020
537 Takip Edilen76 Takipçiler
GunningCrypto retweetledi
GunningCrypto retweetledi

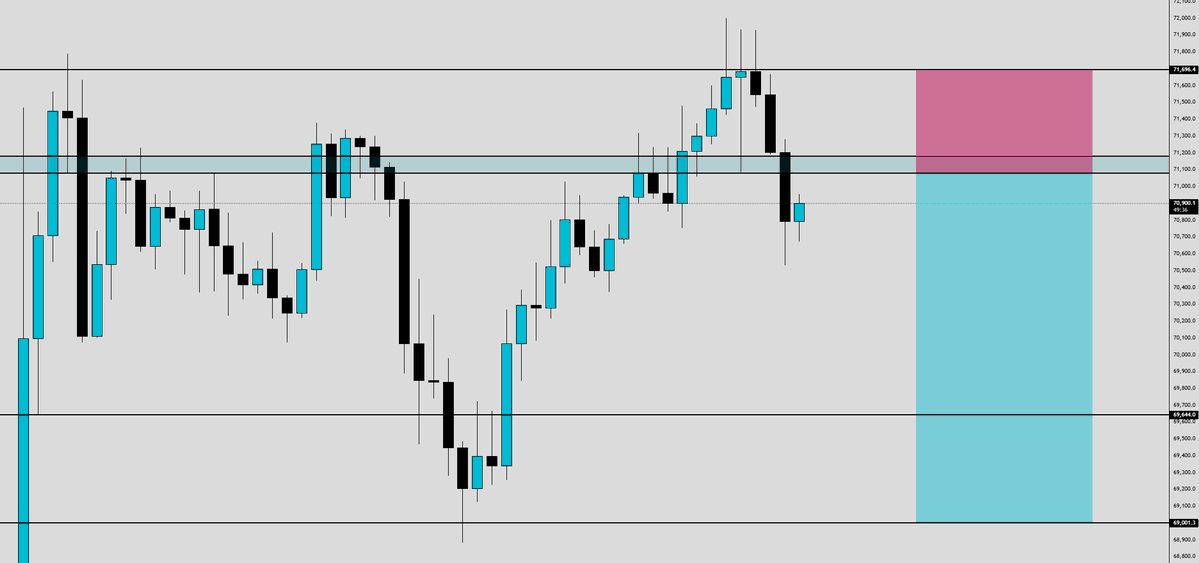
@KillaXBT 67/68 next week then 76-80 shortly thereafter.
You patiently wait for 8X,XXX then full port short and close your computer till late summer/early fall.
Yes this is financial advice.

English

@PeterPaulGuy @hamill23 How’s he 22 if the article states that he had a conviction for no insurance in 2016 😂😂
English

🇮🇪 Ireland - 12th March 2026
Louis Diasivi (22), who was caught driving without insurance for a second time, refused to give gardai his details and told them: "This is a f*cking joke" has walked out of court with just a €500 fine.
#Diversity #TwoTierJustice

English

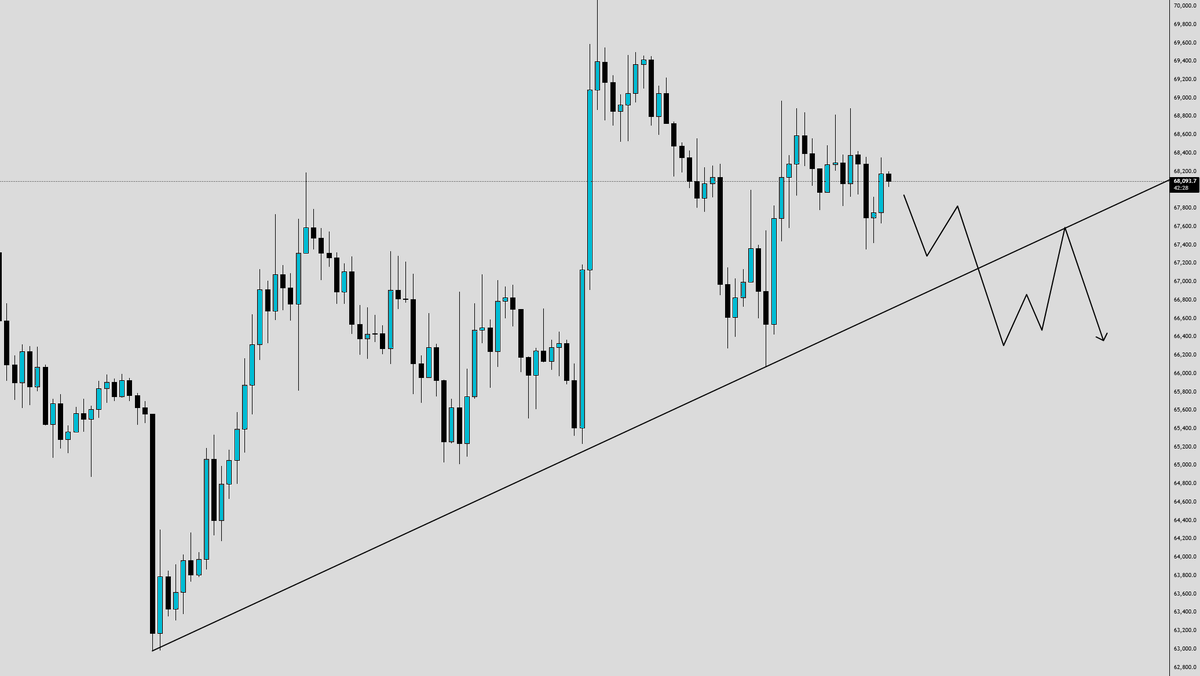
more longs to liquidate $BTC
Blasto@iBlasto_
If you're long on $BTC just because of that trendline… I’ve got bad news for you. The Liquidation Of Longs❗️❗️❗️
English
GunningCrypto retweetledi

RSA — 18 February 2011
Global authentication trust impact.
What happened?
Attackers penetrated RSA’s internal systems and exfiltrated data related to SecureID token generation, including seed values used in two-factor authentication. While the breach did not directly drain user funds, it undermined the security assumptions of organizations relying on RSA tokens for access control.
If attackers could correlate stolen seed data with specific deployments, they could predict one-time passwords, enabling unauthorized access to protected systems. The downstream impact was indirect but substantial, increasing breach risk across defense contractors, financial institutions, and critical infrastructure operators that depended on RSA authentication.
$ENX

English
GunningCrypto retweetledi

RT @eliz883: $PEOPLE 3D
The macroeconomic situation is creaking, so trading is high risk.
But I'll try it spot here https://t.co/7GJTwp…
English

Vitalik just repriced all $ETH L2s and Ethereum is scaling like never before
You can hear the OGs roaring, "return to mainnet"
The market is nuking but ETH/BTC is holding a key level
You can see the OGs foaming at the mouth for alt szn
The $SOL trenches have never been more PvP
You can feel the diamond hands not worried on mainnet
Positioned properly:
- $ETH now 2nd largest position
- $PEPE bidding the bottom
- $wojak adding all the dips
- $Z + $ENX good privacy alts too
There's going to be a melt up again soon
Market will chop and bottom for 1-2 months before rate cuts and global liquidity starts flowing
Now's the time to build and bid
Book it

English
GunningCrypto retweetledi

Did you know?
The VPN industry has a major centralization problem. Research shows that 97 of the most popular VPN services are actually owned by just 23 parent companies. For you as a user, this creates a "shell game" where you think you’re choosing a new provider for better privacy, but you’re often just handing your data to the same corporate conglomerate under a different brand name.
When ownership is hidden under complex holding structures and possibly state-influenced constructs, "no-logs" promises become very difficult to verify. In this case you are forced to trust an undecipherable web of corporate interests instead of a transparent single service.
We developed EPN (Enigma Privacy Network) to move past the era of blind trust. Instead of relying on a single company’s hardware and promises, EPN utilizes a decentralized infrastructure. By distributing data across an ever-changing, peer-to-peer network with non-static routing tunnels, we remove the "central point of failure" inherent in traditional VPNs as well as the problem of metadata storage.
This is how we build the future of cyber defense.
$ENX
English
GunningCrypto retweetledi

Announcement: Enigma Livestream EP. 06
Tomorrow, February 4th at 6pm EST
We're excited to host another Enigma Live Session. This time we will get an extensive EPN Update by our Chief Architect @HarrisLion16 and our AI Lead Colby Myers.
The stream will cover:
• Recent progress and status updates on the EPN development
• Exciting news about the Beta Testing
• Personal insights and commentary from Harris Nussbaum, Chief Architect of Enigma
See you tomorrow.
$ENX

English
GunningCrypto retweetledi

Open Source Agentic AI: Risk or Opportunity? (Pt. 01)
A new generation of AI agents has blown up worldwide over the last days, bringing to life immense hopes and horrible fears alike. In just one week, we’ve monitored hundreds of leaks, breaches, and privacy incidents, while being genuinely impressed by Clawdbot and the performance of its early descendants. So what’s happening exactly?
In Part 01 we will take a deep look at the opportunity and attack vectors that open source AI agent systems are currently confronted with.
Advanced autonomous agents such as Clawdbot, Moltbot, and similar self-hosted or semi-hosted systems represent a shift from passive assistants to active operators. These agents observe multiple data sources, maintain long-term memory, interact with wallets, exchanges, and messaging apps, and in some cases execute actions without continuous human confirmation. Typical deployments run on local servers, cloud instances, or hybrid setups tightly coupled to personal communication channels and financial infrastructure.
The appeal is straightforward. These systems operate continuously, reduce reaction time, and automate workflows that are difficult to supervise manually. Much of the current hype focuses on capability, autonomy, and convenience.
Recent incidents and post-mortems around Clawdbot-like agents show risk systemic concentration. The failures were not caused by a single exploit, but by overlapping architectural, operational, and behavioral weaknesses that compounded over time.
1/ Technical exposure and attack surface
Most advanced agents require broad permissions to function. API keys, wallet access, persistent credentials, and read/write access to local or cloud storage are commonly granted by default. In several documented cases, sensitive secrets were stored in plaintext configuration files, environment variables, or long-lived memory stores. Once filesystem access, logs, or remote command execution were obtained, escalation to full control followed quickly.
Isolation was frequently insufficient. Plugins, tools, and integrations often shared a single runtime and privilege scope, allowing vulnerabilities in auxiliary components to propagate into core agent functionality, including financial actions.
Network exposure further amplified risk. Agents listening on fixed ports, exposing dashboards, or relying on publicly reachable endpoints became discoverable. Persistent exposure increased the likelihood of misconfiguration, credential reuse, and brute-force attacks.
2/ Data accumulation and metadata leakage
Autonomous agents accumulate large volumes of contextual data by design. Conversation history, decision context, transaction metadata, and behavioral traces are retained to improve performance. This creates dense, high-value datasets that are rarely segmented or time-bounded.
Even when payload data is encrypted, metadata often remains observable. Stable IP addresses, fixed routing paths, predictable polling intervals, and continuous uptime allow external observers to infer behavior patterns over time. Unlike traditional applications, these agents rarely have clear session boundaries. Continuous operation means continuous exposure.
Part 01 was all about attack vectors and data - next time we will analyze how Enigma's privacy stack and RAVID can drastically reduce systematic risk and improve architectural security of all open source advanced agents.
Stay tuned for Part 02 and make sure to join our community.
$ENX

English
GunningCrypto retweetledi

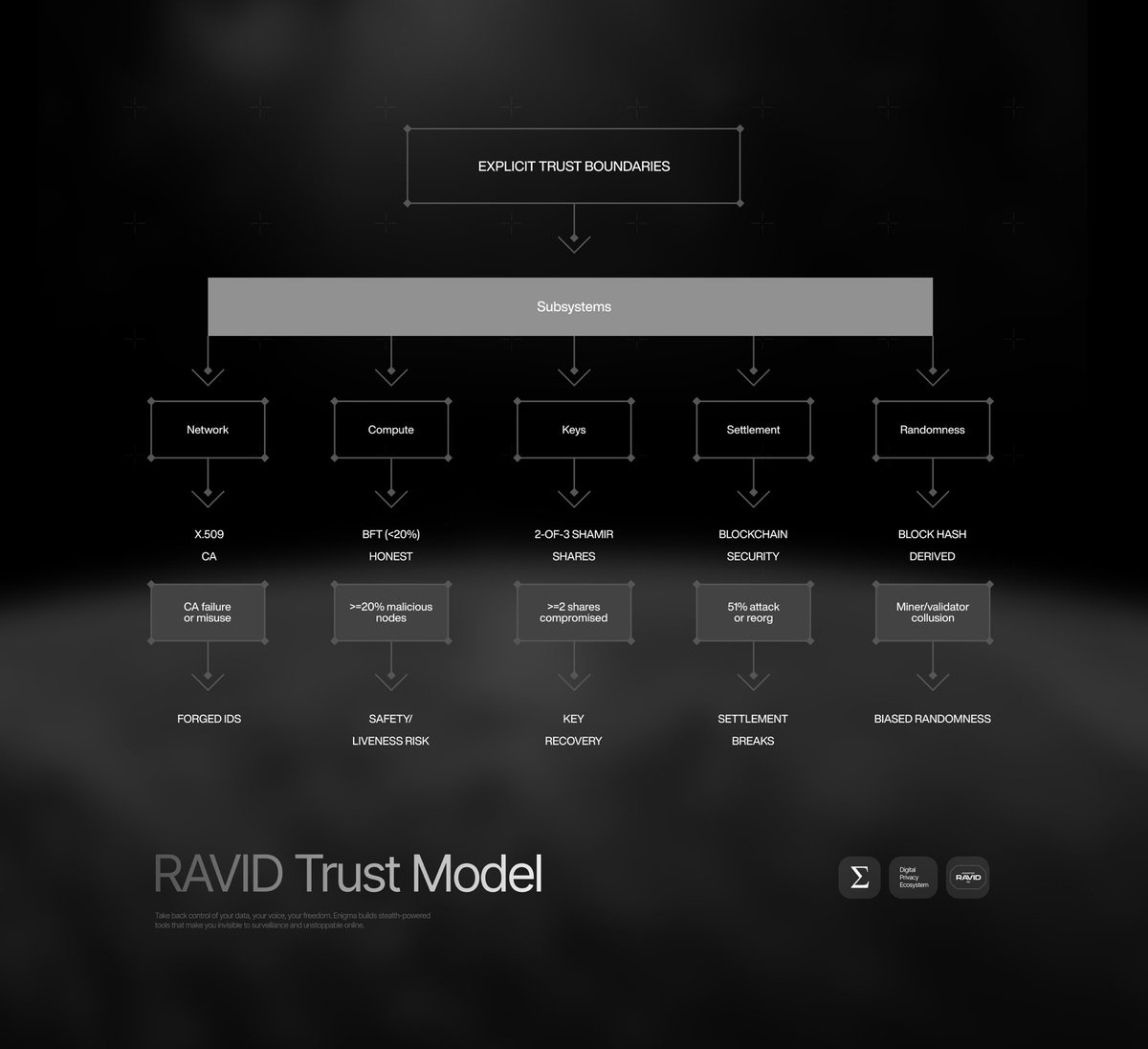
Trust Model: Explicit Assumptions and Failure Modes
Security systems fail at their trust boundaries.
RAVID’s trust model makes these boundaries explicit, allowing operators and reviewers to understand exactly what assumptions are being made.
RAVID defines trust per subsystem, anchoring each to specific primitives rather than implicit operator behavior.
Network identity relies on X.509 certificates; compromise requires CA failure
Compute consensus assumes fewer than 20% malicious nodes in BFT execution
Key material uses 2-of-3 Shamir secret sharing; compromise requires multiple shares
Economic settlement depends on blockchain security assumptions (e.g., Ethereum 51% resistance)
Randomness is derived from block hashes; manipulation requires miner collusion
By documenting these assumptions explicitly, RAVID avoids ambiguous guarantees and enables precise risk evaluation.
Relevant documentation:
docs.engma.io/ravid/trust-mo…
$ENX
English
GunningCrypto retweetledi

Identity & Authorization: Access Before Connectivity
Traditional networks grant connectivity first and attempt to enforce trust later.
RAVID reverses this order, ensuring that network access itself is conditional on identity and policy verification.
RAVID enforces a strict authenticate → authorize → connect model. Network access does not exist until identity has been verified and permissions evaluated.
User identities are established through an enrollment process where time-bound tokens define scope, duration, and service permissions.
Cryptographic keys are generated on the user’s device and tied to these claims.
After proof validation and CSR submission, an intermediate certificate authority issues X.509 certificates constrained by epoch and service policy.
Mutual TLS is then used to authenticate both client and network edge.
Session keys are derived using ECDH, and authorization is re-evaluated as sessions transition between epochs.
This model minimizes unnecessary exposure by ensuring that network paths only exist for explicitly authorized identities.
Relevant documentation:
docs.engma.io/ravid/identity…
$ENX

English
GunningCrypto retweetledi

@VitalikButerin is shilling privacy like no tomorrow. @engma_io fits the narrative perfectly with its revolutionary RAVID tech.
Being early feels risky, being late feels obvious. Legends are made by those who choose their path first. Which side are you on, anon?
- Yo Bih Lord
$ENX

English