HackRisk.io
44 posts


@H4ckRisk
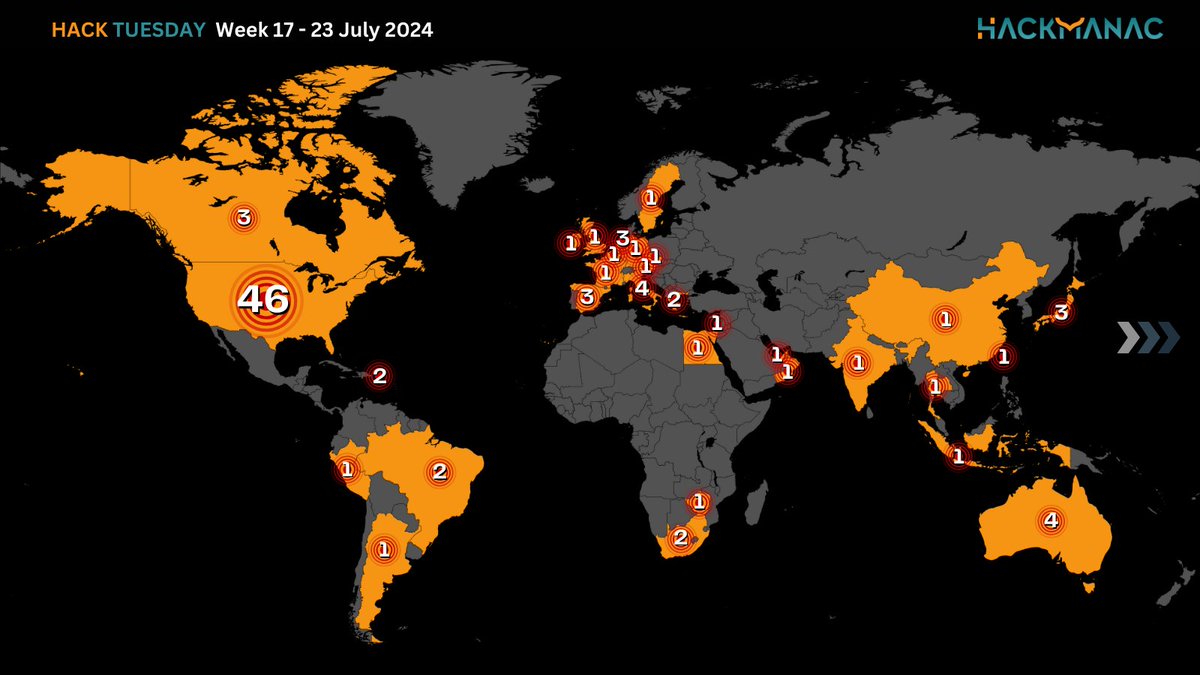
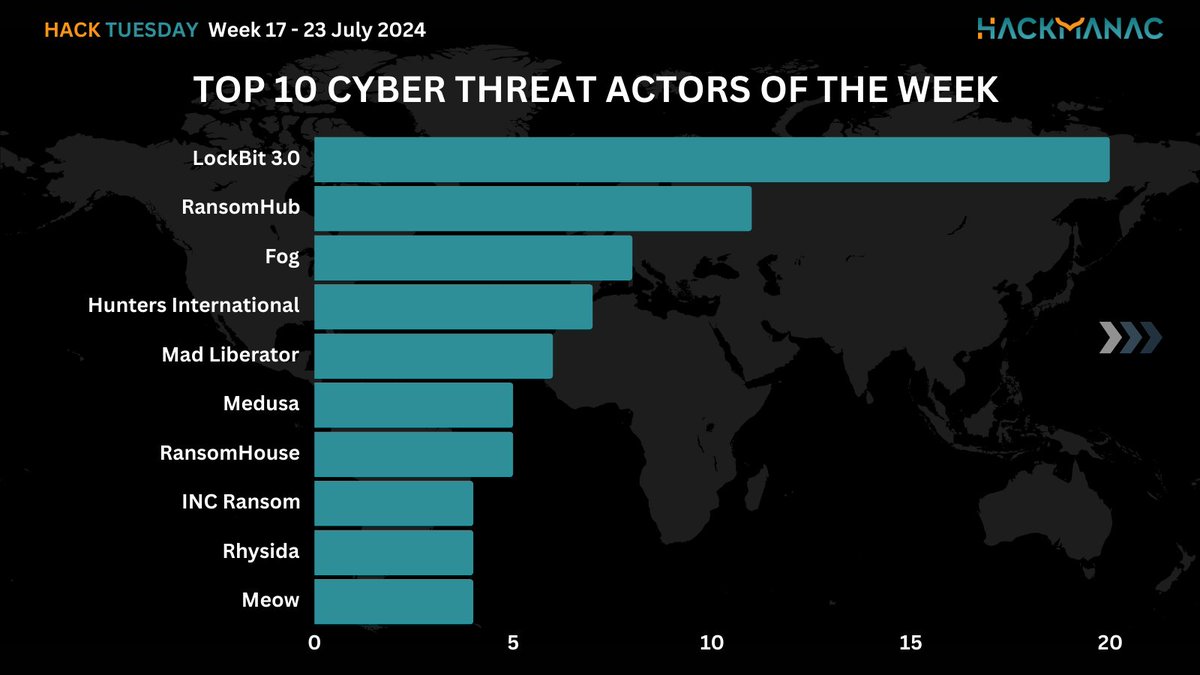
https://t.co/Tjr7gr3Ni8 is a cyber-attack data visualization, information dissemination and impact analysis service provided by @H4ckmanac







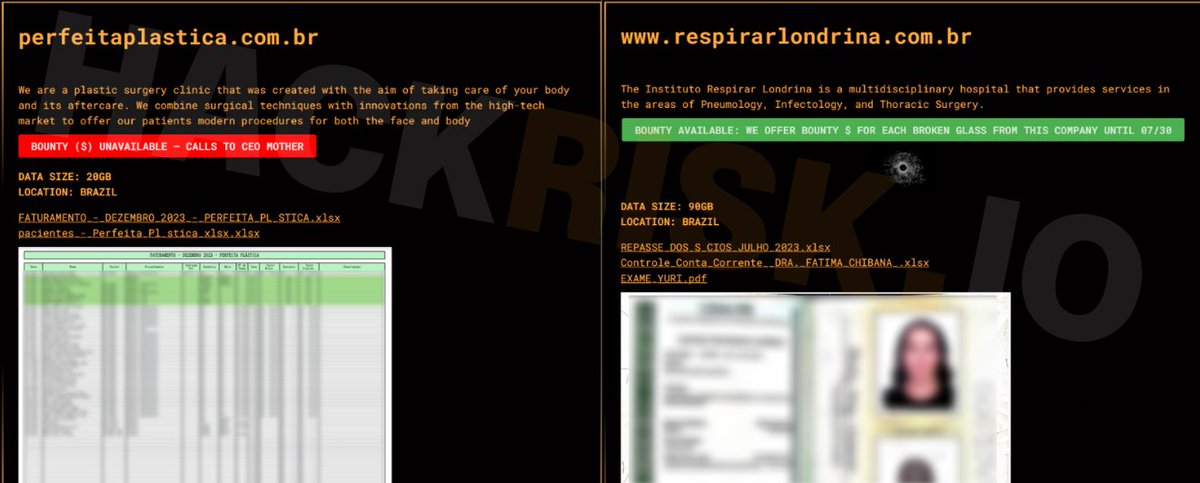
🚨 #CyberAttack 🇧🇷#Brazil, Policlínica Dona Anita The newly discovered ransomware group known as Ransomcortex has begun its ransomware campaign against Policlínica Dona Anita, a Brazilian healthcare organization. On the website, the polyclinic states: "We have been notified of fraud attempts using the name of our company. Pay attention to the documents received and consult our official channels if you have any doubts about a contact or information." #Ransomware













🚨#Chile🇨🇱: El grupo de ransomware akira publica a la Cooperativa de Ahorro y Crédito Financoop (financoop[.]cl). #infosec #ransomware #DarkWeb #akira #servicios #financieros #financoop cc:@CSIRTGOB