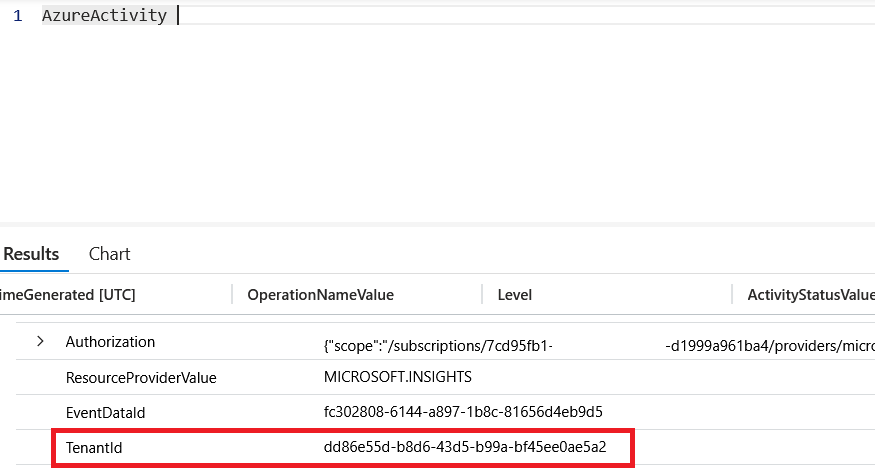
I genuinely don't think people are talking about this enough. --sdk-url is a non-documented Claude Code argument that circumvents your corporate Claude 'remote control' policy and allows outbound connections to any server. Claude can quite literally be considered a C2 framework.
Origin@originhq
Claude Code's remote control protocol lets developers orchestrate instances programmatically. @tyholms reverse engineered it and found an undocumented flag that redirects any instance to attacker-controlled infrastructure, silently bypassing all permission checks. originhq.com/blog/reversing…
English