🕵️♂️ Which Threat Actors Are Targeting Your Industry Right Now?
Do you know which threat actors are targeting your industry right now? We do.
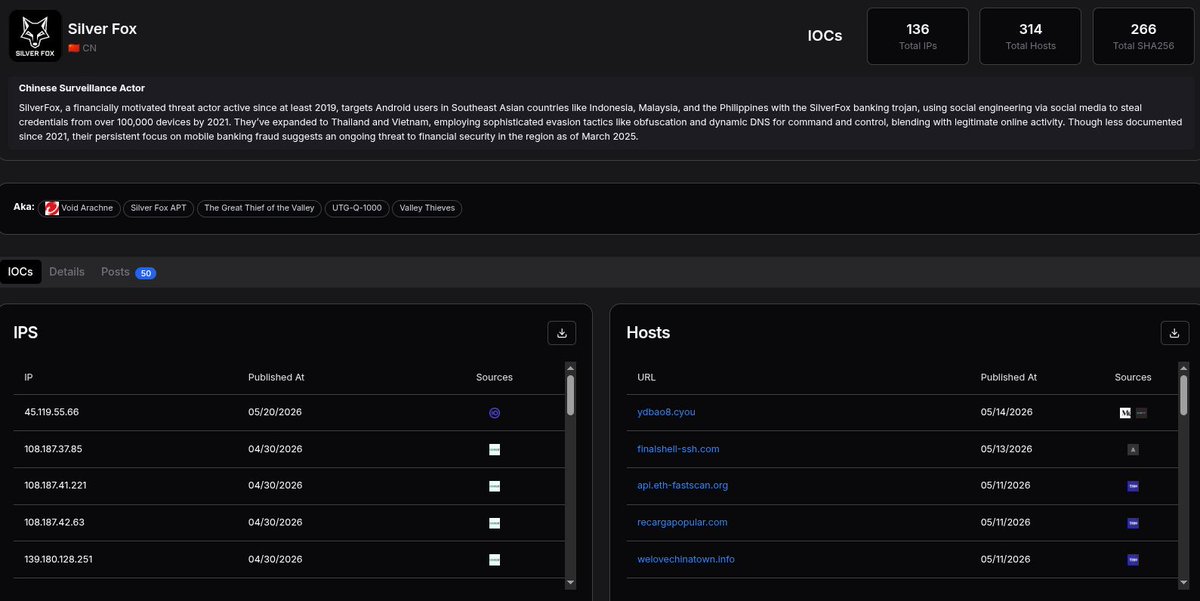
With Hunt, you can filter our Threat Actor Listing by industry targets, then jump from a category like Government, Finance, or IT into actor-level context.
Each actor profile includes aliases, country attribution, recent IOCs, IPs, hosts, SHA256s, posts, and source-backed activity.
Start broad by industry, select an actor, and move straight into investigation.
Discover which threat actors are active in your industry 👉 hunt.io/get-started
#ThreatHunting #ThreatIntelligence #CyberSecurity

English