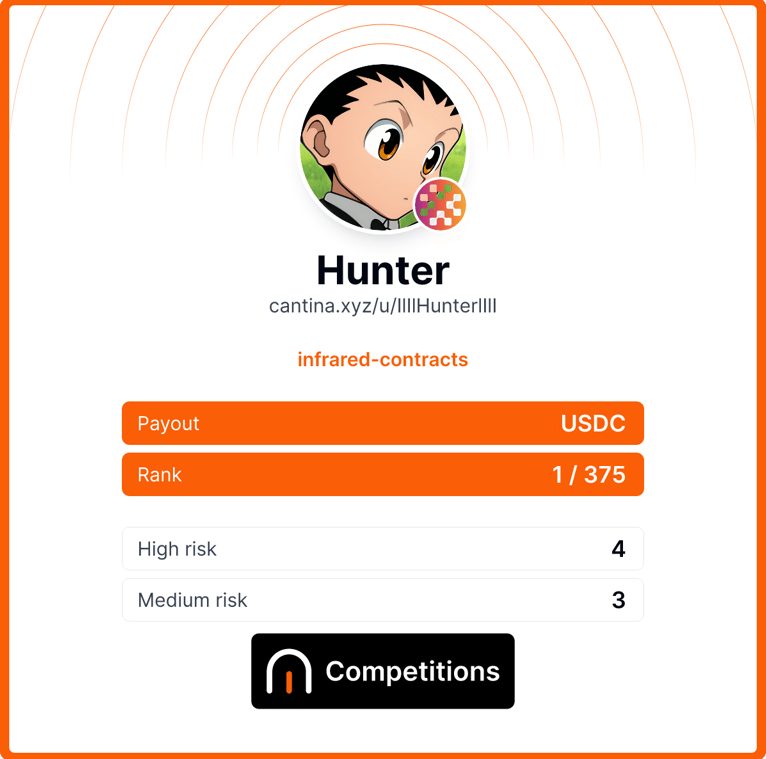
Hunter
761 posts

@Huntoor
Hunting Bugs Everywhere | https://t.co/5Sj1CzQCoV for private audits



Why permissionless DeFi is a double edged sword? dTRINITY got exploited for $257K today. here's what actually happened: their dLEND pool (an Aave v3 fork) had a rounding flaw in the cbBTC aToken share math. mint and burn both used the same half-up rounding conversion. at a high liquidity index, withdrawals could exceed deposits. attacker flash loaned, deposited ~$772 USDC valued as ~$4.8M collateral, borrowed 257K dUSD, then looped 127 deposit/withdraw cycles through a helper contract. each cycle extracted a bit more cbBTC than was put in. net profit after gas: ~$257K. pool TVL was only ~$435K. on March 5, @HypurrFi publicly disclosed a structural rounding vulnerability in Aave v3 versions prior to 3.5 with the same exploit pattern. conditions: high per-unit token price, low decimals, low gas fees. cbBTC checks all three. dLEND is an Aave v3 fork. unclear whether they were running a patched version, but the exploit matching a known vulnerability from 12 days earlier raises questions.

Bug bounty hunting in web3 programs offering up to $80k in rewards "should" be easier in 2026 and 2027. Over the years, protocols without a large treasury have slowly transitioned from paying for an expensive security engagement with a firm, to an affordable private audit from a single elite researcher (remember those times? the solo-auditor golden age?), to fast and cheap AI Audits, to bundles of 100% free and open-source SKILLS.md. And in a world where new firms compete on who can offer the most affordable engagement, with a quality as close as possible to that of an elite human auditor, the only winners are actual elite human auditors: black hats and bug bounty hunters.