Ajay (blue tick) retweetledi

A 0-click exploit chain for the Pixel 10: When a Door Closes, a Window Opens projectzero.google/2026/05/pixel-…
English
Ajay (blue tick)
1.7K posts

@IamAlch3mist
embedded security researcher | re,vr...






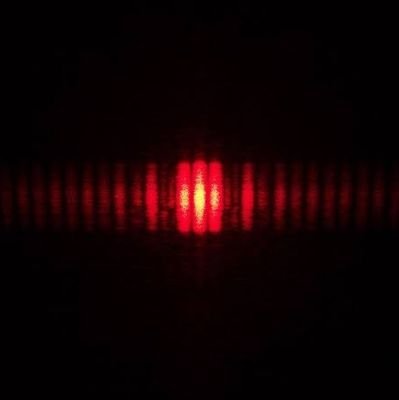
We're likely 1st to publicly exploit crypto: af_alg as a new attack surface in kernelCTF. Our members @n0psledbyte & @st424204 started poking it in Sep 2025, finding a 0-day container escape unnoticed since 2011. @AnthropicAI @OpenAI: interested in collaborations? We are all ears