Sabitlenmiş Tweet
eShard
992 posts

eShard
@eshard
Beyond testing tools, solutions that deliver expertise. 🌐 Chip & binary security testing https://t.co/1dUvkjLR8L https://t.co/BCMLXCF49H
Katılım Temmuz 2015
335 Takip Edilen1.8K Takipçiler

We're at @offensive_con 🏴☠️ in Berlin!
We're doing demos of our Time Travel Debugging tool, so stop by our booth to catch some "bugs" 👀


English

Missing peripheral in QEMU? Adding it yourself is easier than you think.
We hit a wall analyzing CVE-2019-14192 on real @Raspberry_Pi 3B+ firmware, so we added the missing driver to #QEMU. Register by register, using U-Boot's own source as the spec.
eshard.com/blog/u-boot-cv…
English

A malicious MKV opens in VLC. A fake calc.exe pops up: "We've got you."
An AI agent made an MCP trace-driven analysis and reconstructed the full exploit chain, use-after-free, heap spray, ROP chain, shellcode, from a single CPU trace.
🔗eshard.com/blog/vlc-media… #exploit
English

Heading to @offensive_con in Berlin next week ✈️
We'll be demoing Time Travel Debugging (TTD) through a hands-on CTF challenge. Come break things with us 😎
English

Live session with @PqShield: physical attacks on post-quantum crypto, a CPA attack on ML-KEM, and how to harden your defenses.
📆 June 2nd | 10am CEST | 4pm SGT
Limited seats 👇 zoom.us/meeting/regist… #pqc #hardwaresecurity

English

We have a Slack! Come chat, get support for our free TTD tool, and be part of the community: u.eshard.com/slack
English

Thanks for joining our live! Recording is up at the same link. Just reply here or comment there if you have any questions.
eShard@eshard
🔴 We're starting our live! youtube.com/watch?v=RaZrX0… #reverseengineering #cybersecurity
English
eShard retweetledi


Join us tomorrow! We'll go live to talk about AI, reverse engineering, time travel debugging, and more: youtube.com/live/RaZrX0PX4…
🔔 Click the bell so you don't miss it!
#ai #reverseengineering #cybersecurity

YouTube
English

Join us next week for an open conversation about the role of AI in reverse engineering:
🔴 youtube.com/live/RaZrX0PX4…
🔔 Click the bell so you don't miss it!
#ai #reverseengineering #cybersecurity

YouTube
English

AI can work great at static analysis, but it fails at at dynamic analysis because runtime data is a moving target.
The only way to solve this is to change the data format: turn dynamic execution into static data.
🔗 eshard.com/blog/dynamic-a… #cybersecurity #reversengineering #ai
English

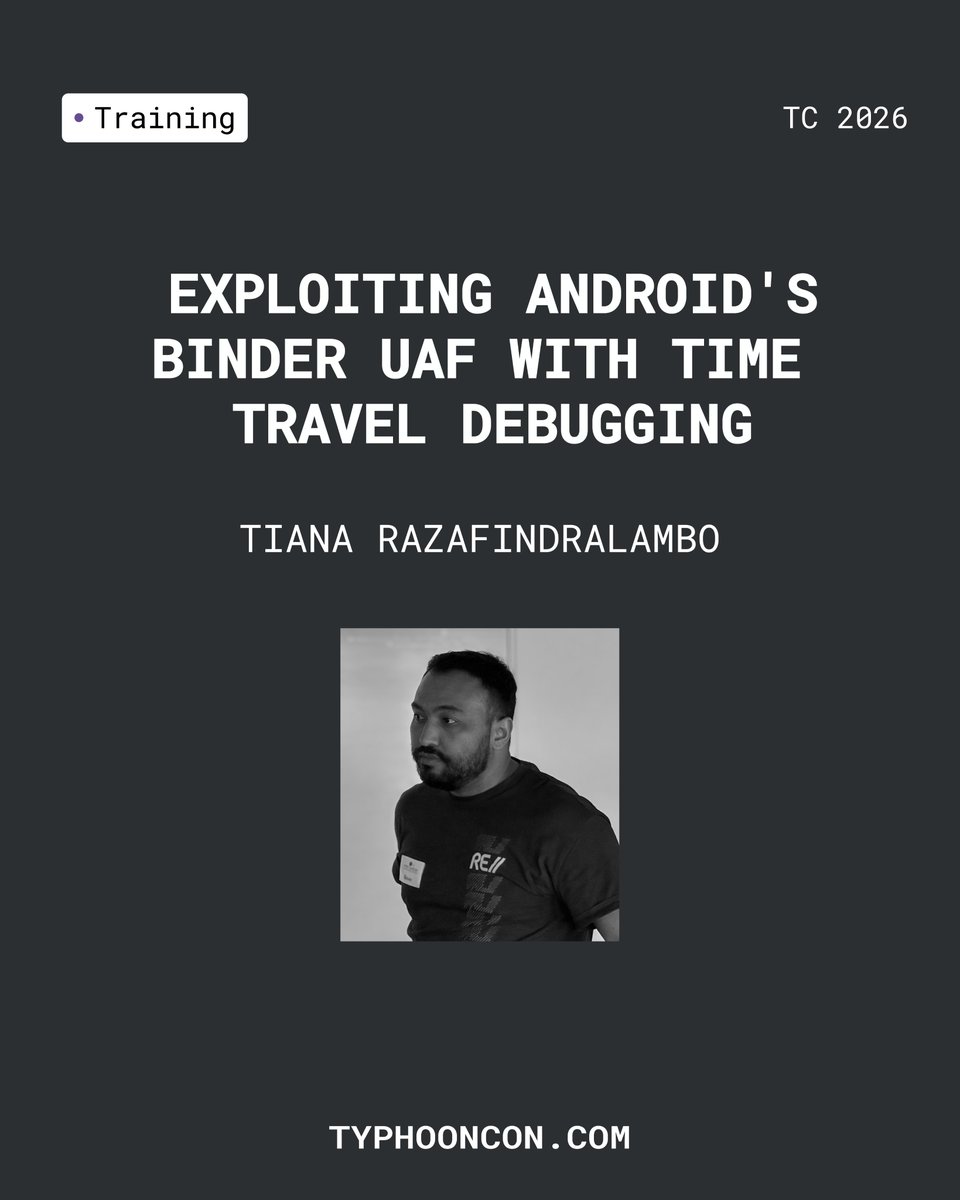
Last seats for our @TyphoonCon 2026 training in Seoul! 🇰🇷
𝗗𝗲𝗲𝗽 𝗗𝗶𝘃𝗲 𝗶𝗻𝘁𝗼 𝗔𝗻𝗱𝗿𝗼𝗶𝗱 𝗕𝗶𝗻𝗱𝗲𝗿
🗓️ May 27 - 29
Register for this training and get a FREE main conference pass! DM to claim.
🔗 eventbrite.com/e/196856163985…
#reverseengineering #AndroidSecurity #cybersecurity
English

We built a CTF challenge designed to be painful to reverse engineer. Then an AI agent solved it in 6 minutes.
Try it yourself before reading how 👉 ttd.eshard.com
Full write-up: eshard.com/blog/ring0-rin…
#CTF #reverseengineer #hacking
English

Hackers are using AI, creating a massive imbalance in the reverse engineering world. Because unlike hackers, security analysts can't be careless when using LLMs, so we fall behind.
↗ Here is how to level the playing field safely: eshard.com/blog/hackers-a… #reverseengineering
English

@mateaSays @typhooncon @SecuriTeam_SSD We can consider organizing another training session online. What's your timezone so we can keep it in mind?
English

@eshard @typhooncon @SecuriTeam_SSD Will this be recorded for the sake of folks who won't make it in person?
English

Join us at @Typhooncon in Seoul for a training on Android Binder internals.
We’ll guide you through the complexities of low-level component exploitation, moving from root-cause analysis to a reliable proof-of-concept.
🔗 Register here: eventbrite.com/e/196856163985…

English

