
Iskuri
835 posts








In 1994, Nintendo made a public event at a Dutch airport where 10,000 counterfeit Game Boy games they confiscated in the Netherlands were ran over by a steamroller, to send a message to counterfeiters. An actor in a Mario costume was overseeing the operation.



Congratulations to our top hackers who have won our annual year-end bonus awards for 2023! Thank you for your hard work and dedication last year. We are always looking for talented individuals to join us. Hope to see you next year!! #JoinUs #YearEndBonus #GratefulHeart #OSRC #OPPO



Also, here is my exploit for the PN553, an NFC chip from a series which was found an insane number of phones at the time of analysis: github.com/Iskuri/PN553-S… this version purely dumps the BootROM from the chip, and could be adapted to most non-updated PN series chips.

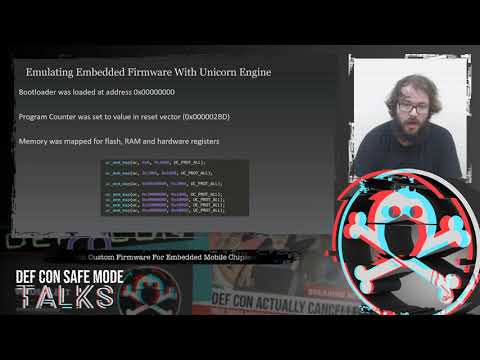


Physical Attacks Against Smartphones #MobileSecurity #AndroidSecurity #BlackHatUSA23 [SLIDES] by @Iskuri1 i.blackhat.com/BH-US-23/Prese…



Physical Attacks Against Smartphones #MobileSecurity #AndroidSecurity #BlackHatUSA23 [SLIDES] by @Iskuri1 i.blackhat.com/BH-US-23/Prese…


