Jérôme Bezet-Torres (#MVP x6 #MCT)
11.9K posts

Jérôme Bezet-Torres (#MVP x6 #MCT)
@JM2K69
Microsoft MVP/ Microsoft Certified Trainer / Powershell / PowerCli / MEMCM / Deployment / MDT / XAML / Automation
Lyon Katılım Ağustos 2011
1.3K Takip Edilen1.4K Takipçiler
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

Windows Server Upgrade Experience Survey forms.cloud.microsoft/pages/response…
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

I just released EIDVirtual v2! 🚀
Get a virtual smart card reader that uses a real USB drive for free. It automatically simulates a GIDS applet to manage your certificates—a perfect alternative to TPM-based MS Virtual Smart Cards.
Check it out here 👇 #EIDVirtual" target="_blank" rel="nofollow noopener">mysmartlogon.com/download#EIDVi…
English

Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

Blog post: #HyperV #PowerShell HyperV.VMFactory: VM Environments, Service Orchestration, and Mermaid Diagrams dlvr.it/TSgd7C

English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

New blog post - PowerShell Is King – Download ESD and Flip It to WIM deploymentbunny.com/2026/05/25/pow… via @mikael_nystrom @Truesec
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

Introducing psign: portable code signing. every file format, every signing method, every platform 👇
No more "let's run this on Windows because of signtool.exe". Say yes to code signing from Linux! 🚀
github.com/Devolutions/ps…
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

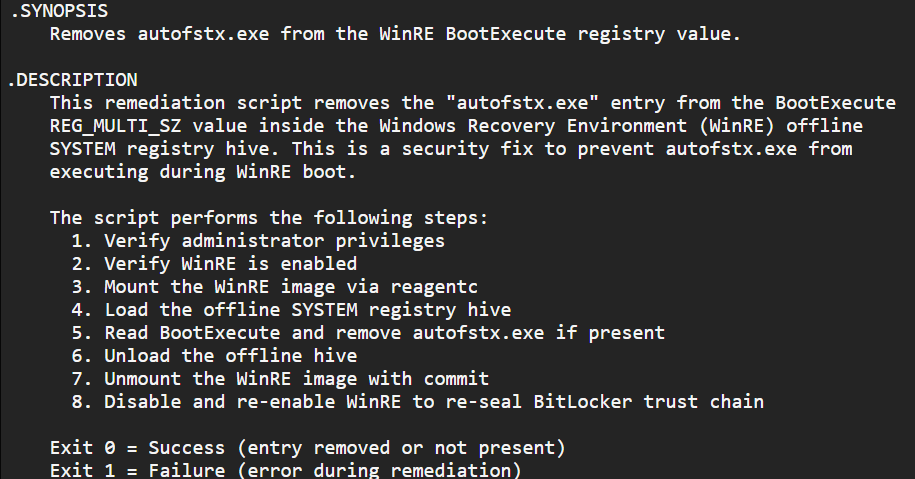
Updated guidance on BitLocker + Yellowkey - again, now with a script to configure the workaround.
Time to test it out!
msrc.microsoft.com/update-guide/v…
#MSintune #Windows11
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi
![Maurice Daly [MVP]](https://pbs.twimg.com/profile_images/1182232265255981056/RrKR33Pc.jpg)
In case you missed it, the Driver Automation Tool got a big upgrade a few weeks back, including #MSIntune support. Reflecting back on the past and highlighting new features here - msendpointmgr.com/2026/05/19/dri… #SCCM #ConfigMgr #Drivers #BIOS
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi
![Mike Terrill [MVP]](https://pbs.twimg.com/profile_images/1921307417620742144/iejUAVvq.jpg)
@damigs @ncbrady @gwblok Just keep in mind that this is updating the active db and not the default db. I stole this slide from the free training @jarwidmark gave on Secure Boot (which is worth a watch):
![Mike Terrill [MVP] tweet media](https://pbs.twimg.com/media/HIpeKOTawAAcD1g.jpg)
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

Join @miketerrill & @gwblok & learn how to create your own content items in #DeployR and integrate them with your task sequences. Sign up at: 2pintsoftware.com/events/list/de…
We will cover usage & best practices with tips for importing them from the community or another DeployR instance.
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

There is another @2pintsoftware #DeployR seminar tomorrow at 10am Eastern/15:00 GMT, there is still time to sign up: #Webinar" target="_blank" rel="nofollow noopener">2pintsoftware.com/events/list#We…
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

Microsoft is rolling out update KB5089573 to fix Windows 11 desktop sluggishness. The new "low latency profile" speeds up the Start menu and app launches, though the tech giant is already defending the feature against "cheating" claims.
neowin.net/news/kb5089573…
^P
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

Kick off Windows Server Summit and gain valuable insights as Windows Server product leaders come together to discuss the momentum behind Windows Server 2025 and share what’s coming next. x.com/i/broadcasts/1…
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi

"We're actually working toward making PowerShell 7 be the default in the next version of Windows Server."
"We'll probably make PowerShell <5.1> an optional component or a feature on demand, and then we'll have PowerShell 7 be the default."
🥳 Source: x.com/windowsserver
English
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi
Jérôme Bezet-Torres (#MVP x6 #MCT) retweetledi



![Mike Terrill [MVP] tweet media](https://pbs.twimg.com/media/HIn-ccebYAAKwYZ.jpg)
