
Jake Hulberg
100 posts

@JakeHulberg
Developer Advocate @Infisical. Talking all things secrets, PAM, & certificate management. 🎥 YouTuber at Jake's Tech on breaking into tech & dev tools

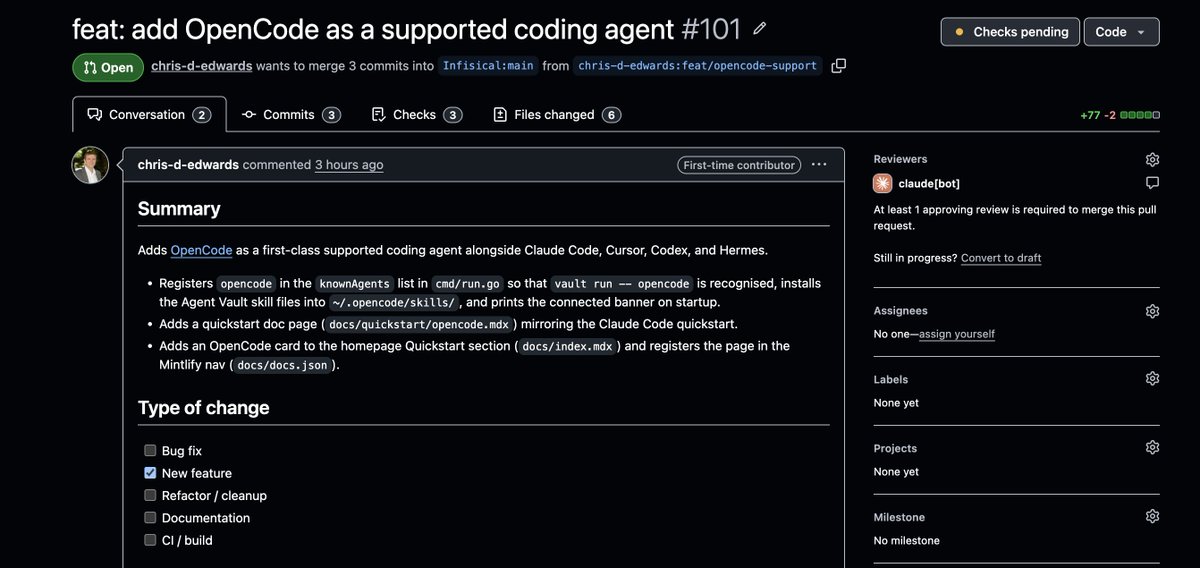






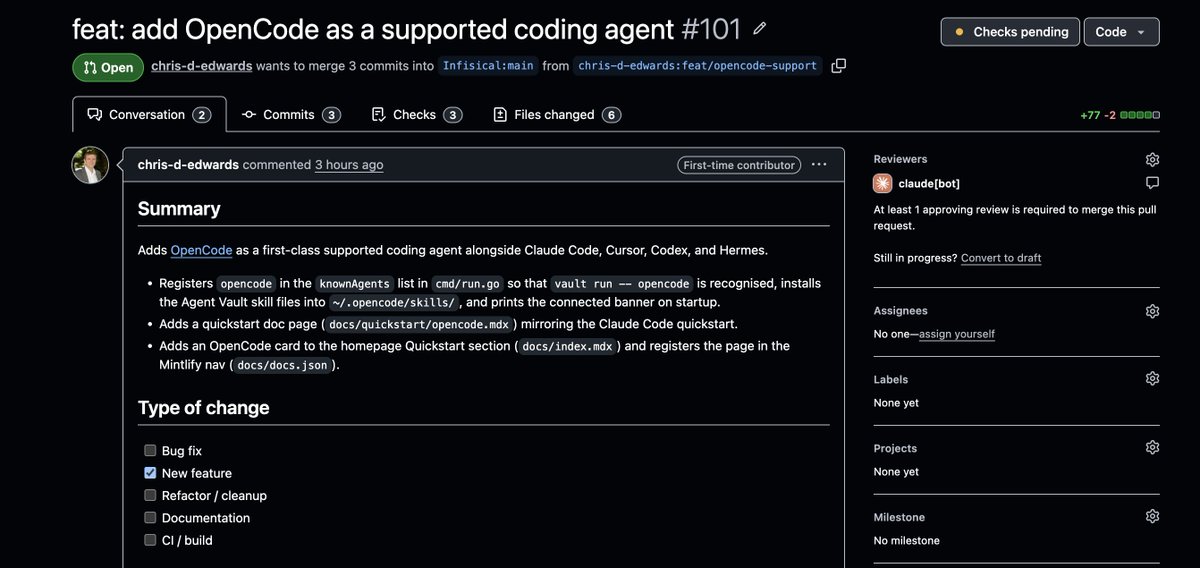
EXO v1.0.70 is out. This release ships with multimodality and major enhancements for memory usage in long context use cases (e.g. @openclaw and @opencode), as well as updated model support and QOL features.

HOW TO MITIGATE A CREDENTIAL BREACH 👇 With all the security breaches right now, I thought I'd share two cents on how the best engineering teams secure their secrets and credentials across local development, CI/CD, and production systems (this should be layered with other defense in depth mechanisms). 1/ Store secrets in a vault: Centralize all secrets with a secrets management tool like @infisical. Instead of chasing down secrets across 50+ apps and environments with blind spots, lock everything down in a secure vault, encrypted, with tight access. 2/ Eliminate secret zero: Have your applications authenticate with the vault using infrastructure-native auth method like AWS/GCP/Azure/OIDC/Kubernetes Auth. Upon authentication, the vault should issue a short-lived access token that the application can use to fetch back secrets. This uses workload identity so, for example, if you're running a GitHub Actions CI workflow, you can use OIDC to have the CI pipeline authenticate with Infisical and fetch back secrets. 3/ Eliminate static secrets: Most teams have heard of automatic secrets rotation but not dynamic secrets. Secrets rotation is where you update the value of a secret on a per interval basis; this can be your OPENROUTER_API_KEY. Dynamic secrets is where you mint ephemeral secrets on the fly such a PostgreSQL credential. Leaked a secret? At least it's only valid for a finite period. 4/ Log every action: With the right tooling in place, you should be able to trace which applications and people have access to which secrets and all the times that they are accessed. If something goes wrong - you have a trail to look back on. Have a question? AMA I and the team will try to answer as many questions as we can to do with secure secrets management over the next few days.

Vercel confirmed a breach. Customer environment variables were exposed. Here's what to do right now.



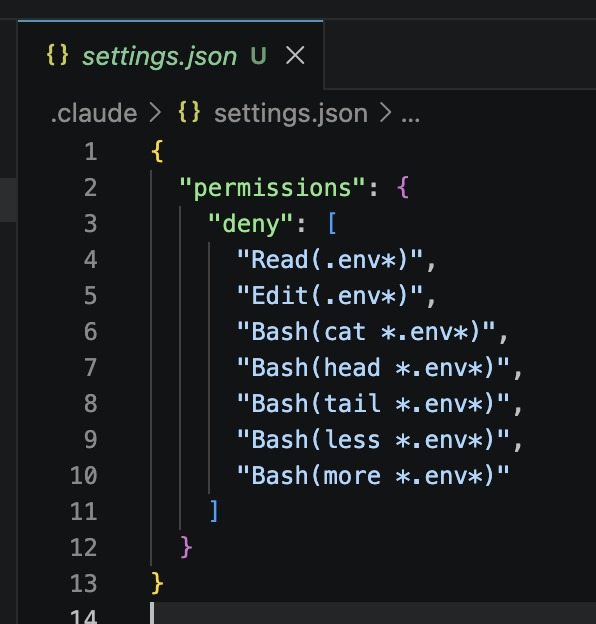
DON’T LET CLAUDE READ YOUR ENV FILE DON’T LET CLAUDE READ YOUR ENV FILE DON’T LET CLAUDE READ YOUR ENV FILE DON’T LET CLAUDE READ YOUR ENV FILE DON’T LET CLAUDE READ YOUR ENV FILE

CLAUDE CODE CAN READ YOUR .ENV FILES BY DEFAULT. Your API keys. Your database passwords. Your secret tokens. All of it visible to the agent unless you tell it otherwise. One setting. Two minutes. Fixes it completely. Add this to your CLAUDE.md right now: Secure your stack before you ship it.





Folks… Why are we still using .env files?? infisical run — npm run dev Thank me later.

We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: vercel.com/kb/bulletin/ve…





We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: vercel.com/kb/bulletin/ve…



We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: vercel.com/kb/bulletin/ve…


If you’re a Vercel user acting on today’s security incident, here are some best next steps: > Rotate all secrets in your Vercel dashboard immediately > Bulk-migrate env vars to sensitive variables (@infisical has a Vercel sync you can use to quickly mark all secrets as sensitive) > Set up automations to rotate DB creds and API keys on a schedule > Use dynamic secrets, so DB credentials are short-lived > Pull secrets at runtime through our SDKs instead of storing them in Vercel > Make sure you have audit logs to see what was accessed