
Karl T. Muth 🌐✈️📊
2.7K posts


@KarlMuth
Invented tech you've used. Likes and replies autodelete. Views mine and not views of others/clients/employers/etc.











Yes, this is a Ferrari. For real. Ferrari's first all-electric car, the Luce, has arrived, and it brings radical change to Maranello. What do you think of its looks?




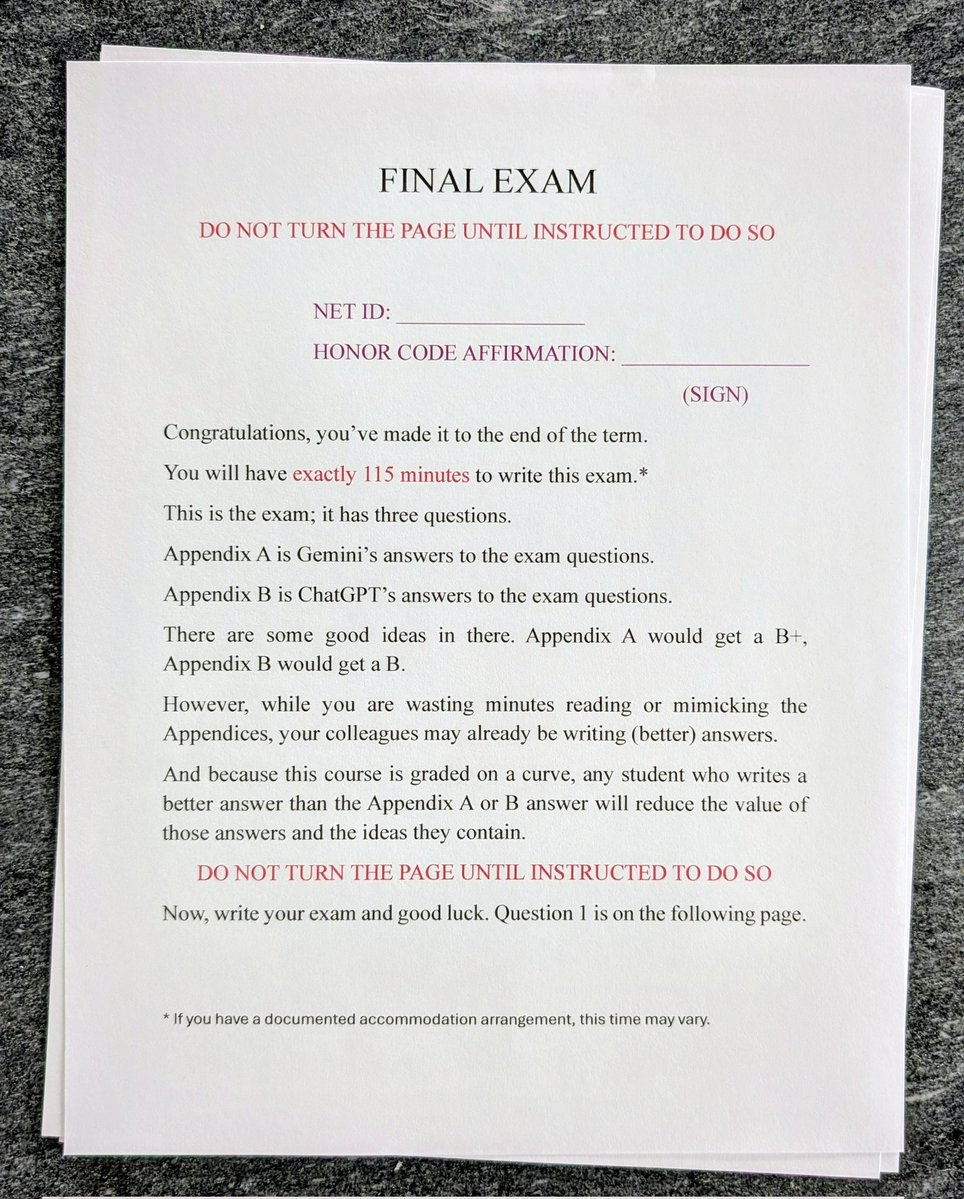



I know there are many (understatement) approaches to AI use where students are being evaluated, and that there is variation between disciplines and levels of study, but I thought I'd share one and perhaps stoke the debate. Anyone (including my students) is welcome to comment...








@DavidCheesesq @Derridazs How would you define a false positive? In your own words. Then, if you would, look at whichever study you refer to and see how it defines "false positive." Please then let me know if that is how you would conceive of the term. (My point being I think you've been duped.)



@GhostOfSocrates Cool, I teach zero of those people. This is an elite law school. This is not what you're imagining.



I know there are many (understatement) approaches to AI use where students are being evaluated, and that there is variation between disciplines and levels of study, but I thought I'd share one and perhaps stoke the debate. Anyone (including my students) is welcome to comment...

