Lavi Goldshtein
15 posts

Lavi Goldshtein
@LaviGoldshtein
Cyber Security Researcher at @hunters_ai @team__axon
Katılım Temmuz 2024
36 Takip Edilen22 Takipçiler
Lavi Goldshtein retweetledi

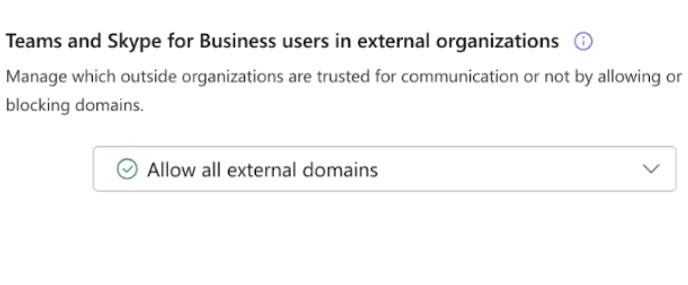
External communications are the primary threat in Microsoft Teams.
The fact that this capability is enabled by default in M365 tenants makes it particularly attractive for attackers.
More details in our latest blog: hunters.security/en/blog/micros…
#ThreatHunting #MicrosoftTeams
English
Lavi Goldshtein retweetledi

Threat hunting tip 🔥
Look for ChatCreated events in M365 logs where the sender domain is external + rarely seen.
This pattern often signals fake IT/Helpdesk phishing in Teams.
We share detection logic in our latest blog hubs.li/Q03G1Z-_0
#ThreatHunting #MicrosoftTeams
English
Lavi Goldshtein retweetledi

🚨 Major Chrome Extension Threat Campaign 🚨
The new year kicks off with a significant cybersecurity threat that demands attention.
@hunters_ai Team AXON is now actively researching this threat, that was initially appeared as a single incident involving Cyberhaven's compromised browser extension and has now revealed itself as part of a much larger, coordinated campaign.
💡 What we know so far:
- There are indications that this campaign has been active for at least 7 months, targeting a variety of Chrome extensions and apps.
- December 2024 saw a notable spike in compromised Chrome extensions, marking the height of this activity.
- Affected extensions include malicious mechanisms to exfiltrate user cookies, posing a severe risk to both users and organizational services.
📌 Indicators of Compromise (IOCs):
Domains:
"bookmarkfc[.]info",
"vpncity[.]live",
"castorus[.]info",
"parrottalks[.]info",
"primusext[.]pro",
"censortracker[.]pro",
"uvoice[.]live",
"iobit[.]pro",
"moonsift[.]store",
"yujaverity[.]info",
"wayinai[.]live",
"readermodeext[.]info",
"policyextension[.]info",
"yescaptcha[.]pro",
"internxtvpn[.]pro",
"wakelet[.]ink",
"linewizeconnect[.]com",
"bardaiforchrome[.]live",
"blockadsonyt[.]vip",
"chataiassistant[.]pro",
"chatgptextension[.]site",
"chatgptextent[.]pro",
"cyberhavenext[.]pro",
"dearflip[.]pro",
"geminiaigg[.]pro",
"goodenhancerblocker[.]site",
"gpt4summary[.]ink",
"linewizeconnect[.]com",
"locallyext[.]ink",
"proxyswitchyomega[.]pro",
"savegptforyou[.]live",
"savgptforchrome[.]pro",
"searchcopilot[.]co",
"tinamind[.]info",
"tkv2[.]pro",
"videodownloadhelper[.]pro",
"vidnozflex[.]live",
"youtubeadsblocker[.]live",
"checkpolicy[.]site",
"extensionbuysell[.]com",
"extensionpolicy[.]net",
"extensionpolicyprivacy[.]com",
"linewizeconnect[.]com"
IPs:
"149.28.124[.]84"
"149.248.2[.]160"
SHA256 Hashes:
"a8d3027be48f61ae6174d067e59e89b7ec47ae19420470248733d8c4b75fda52",
"91ff6f07b3f2347da00b5ec9907d0b7753cca9c442cc9c0692c1c6aba1b90318",
"b53007dc2404dc3a4651db2756c773aa8e48c23755eba749f1641542ae796398",
"0e05fa617531e9c49b9e377b6715c21c909a8dd998cdd68fad09fc463f1dd2ba"
SHA1 Hashes:
"AC5CC8BCC05AC27A8F189134C2E3300863B317FB",
"0B871BDEE9D8302A48D6D6511228CAF67A08EC60",
🛡 Hunting Recommendations:
If you identify any additional suspicious IPs, we recommend conducting a reverse IP lookup. Leveraging reverse IP lookups and their historical data has proven invaluable in identifying many compromised domains linked to the C2 IP addresses associated with the relevant threat actor.
If you identify any additional indicators or TTPs, feel free to share them in the comments below.
Links the valuable resources can be found in the comments section below.
#AXON #THREATHUNTING #DFIR #CYBERSECURITY #CYBERHAVEN #CHROME #HUNTERS
@team__axon
English

🚨 New Blog Alert! 🚨
Excited to share my first research blog on the LummApp infostealer campaign! 🎉 Dive into how malicious browser extensions are used to steal credentials and evade detection.
Read more 👉 hunters.security/en/blog/lummap…
#CyberSecurity #Infostealer #ThreatIntel
English
Lavi Goldshtein retweetledi

A guide I wrote covering the basics of securing Kubernetes :)
hunters.security/en/blog/kubern…
#Kubernetes #cybersecurity
English

1 / 2
We've researched how EDRs audit plist files in macOS LaunchAgents. Detection issues can allow persistence mechanisms to slip through, impacting visibility and security posture.
#Cybersecurity #macOS #EDR #ThreatHunting #Infosec

English