⚙️ LearnEVM.com
166 posts

⚙️ LearnEVM.com
@LearnEVM
The comprehensive EVM deep dive for Solidity developers. Made by @0xMacroSecurity
Solidity memory lesson 9 (for Fantasy top fans): Implicit memory allocation of dynamic vs static arrays. - Dynamic array is initialized to 0x60, pointing to the zero pointer. No memory is allocated. - Static array is initialized by setting it to the location of newly allocated and zeroized memory.



Compile-time zero-cost abstraction for Solidity. When compiled (with or without --via-ir), this function gives very optimized bytecode that is faster than using `keccak256` to compare two strings.


@real_philogy @optimizoor Its a basic optimization, would be more surprised if it didn't.
Zolidity ERC20 is 52 lines of code. But still very gas efficient without assembly, vs. Solady ER20 (613 LOC):
Solidity just added support for Custom Storage Layouts! This allows specifying that your contract storage starts at a point *other than* zero. However, this still doesn't cover the popular Namespaced Storage Layout that modern contracts often use (EIP-7201). For now, you will need to continue using the verbose (but useful!) Solidity pattern to support custom storage for inherited contracts. Hopefully we get this feature soon!
EVM opcodes ranked
Diamond compat is complete! The grand total is... 889 bytes! This is 5x smaller than the Solidity equivalent 🤯 And thanks to my previously conservative math, the router contract *still* supports over 4000 function selectors! 😁 As wise @optimizoor once said, "you can use bytecode as storage" 😎
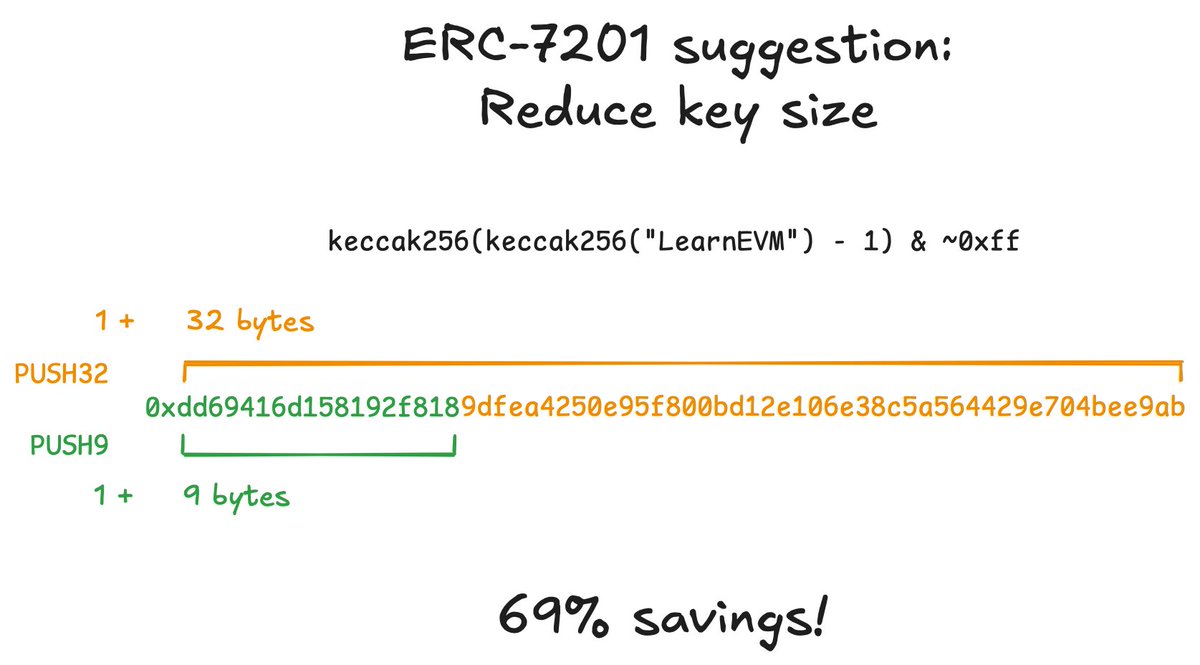
ERC-7201, namespaced storage, is good but bad at the same time. The solution is to just use the first 9-bytes of the keccak. Stop wasting 32 bytes of precious bytecode space everywhere. No, I don’t think we need an ERC for this. Just code from first-principles.





