Sabitlenmiş Tweet
Alexander Leishman 🇺🇸
16K posts

Alexander Leishman 🇺🇸
@Leishman
Founder @River. #Bitcoin. Keeping the fire of human liberty shining bright 🔥
Katılım Aralık 2008
3.1K Takip Edilen48.4K Takipçiler
Alexander Leishman 🇺🇸 retweetledi

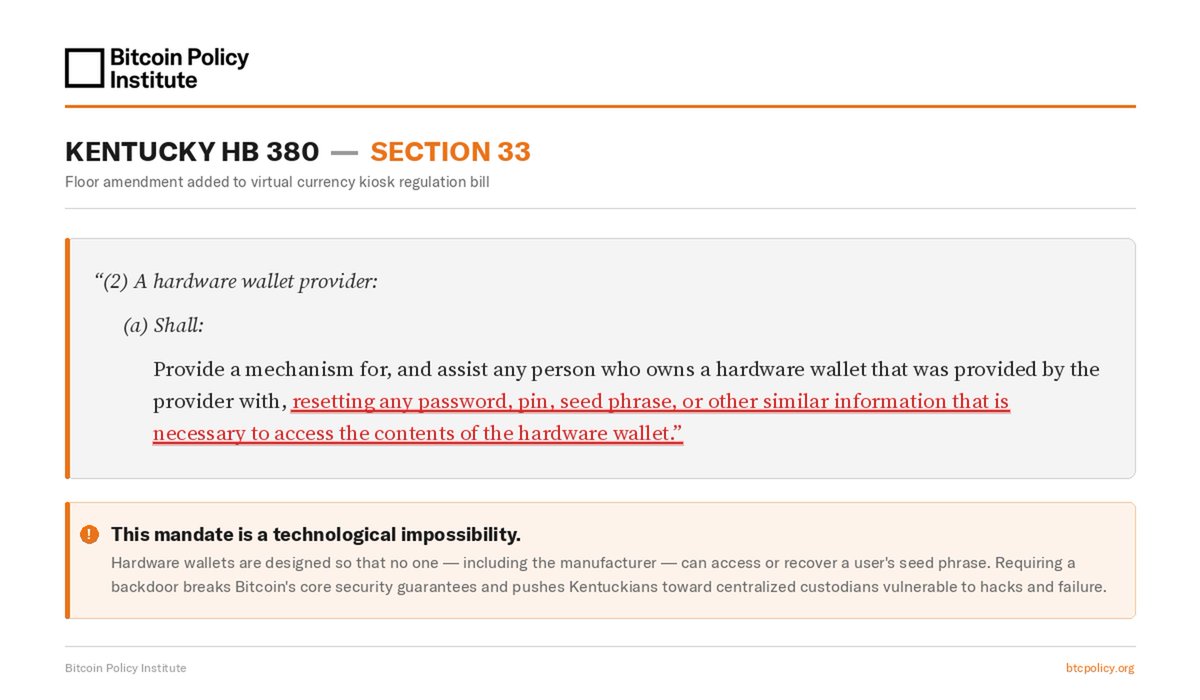
🚨BPI has just learned of an amendment buried in Kentucky HB 380 that would require hardware wallet providers to reset users' seed phrases on request. This would effectively outlaw self-custody in Kentucky. BPI is sending a letter to the Kentucky Senate informing them of the harmfulness of this language.
Section 33 was added as a last-minute floor amendment to a 77-page virtual currency kiosk regulation bill. The underlying bill has political support and is expected to move through the Senate for final passage, possibly within the next week.
The mandate is technologically impossible for non-custodial wallets. Hardware wallets are specifically designed so that no one — including the manufacturer — can access or recover a user's seed phrase. Requiring a backdoor for seed phrase recovery breaks Bitcoin's fundamental security guarantees and pushes users toward centralized custodians that are vulnerable to hacks and failures.
Kentucky legislators should be protecting their constituents' right to secure their own property. We urge the Senate to strip this provision before the bill reaches a vote. Relevant text below

English
Alexander Leishman 🇺🇸 retweetledi
Alexander Leishman 🇺🇸 retweetledi
Alexander Leishman 🇺🇸 retweetledi

@bitrefill @negrunch Great transparency and good luck getting to the bottom of this!
English

March 1st incident report
On March 1, 2026, Bitrefill was the target of a cyberattack. Based on indicators observed during the investigation - including the modus operandi, the malware used, on-chain tracing and reused IP + email addresses (!) - we find many similarities between this attack and past cyberattacks by the DPRK Lazarus / Bluenoroff group against other companies in the crypto industries.
The initial access originated through a compromised employee laptop, from which a legacy credential was exfiltrated. That credential provided access to a snapshot containing production secrets. From there, the attackers were able to escalate their access to our broader infrastructure, including parts of our database and certain cryptocurrency wallets.
We first detected the incident after noticing suspicious purchasing patterns with certain suppliers. We realized that our gift card stock and supply lines were being exploited. At the same time we found some of our hot wallets being drained and funds transferred to attacker-controlled wallets. The moment we identified the breach, we took all of our systems offline as part of our containment response.
Bitrefill operates a global e-commerce business with dozens of suppliers, thousands of products, and multiple payment methods across many countries. Safely switching all these things off and bringing them back online is not trivial.
Since the incident, our team has been working closely with top industry security researchers, incident response specialists, on-chain analysts and law enforcement to understand what happened and how we can prevent it from happening again. A sincere thank you to @zeroshadow_io, @SEAL_Org, @RecoverisTeam and @fearsoff for their rapid response and support throughout this ordeal.
What about your data
Based on our investigation and our logs we don’t have reason to think that customer data was the target of this breach. There is no evidence that they extracted our entire database, only that the attackers ran a limited number of queries consistent with probing to understand what there was to steal, including cryptocurrency and Bitrefill gift card inventory.
Bitrefill was designed to store very little personal data. We are a store, not a crypto service provider. We don’t require mandatory KYC. When a customer chooses to verify their account - e.g. to access higher purchasing tiers or certain products - that data is kept exclusively with our external KYC provider, with no backups in our system.
Still, based on database logs, we know that a subset of purchase records was accessed and we want to be transparent about that.
Around 18,500 purchase records were accessed by the attackers. Those records contained limited customer information, such as email addresses, crypto payment address, and metadata including IP address.
For approximately 1,000 purchases, specific products required customers to provide a name. That information is encrypted in our database. However, since the attackers may have gotten access to the encryption keys, we are treating this data as potentially accessed. Customers in this category have already been notified directly by email.
At this time, based on the information currently available, we do not believe customers need to take specific action. As a precaution, we recommend remaining cautious of any unexpected communications related to Bitrefill or crypto. If this assessment changes, we will of course immediately inform those affected.
What we are doing
We have already significantly improved our cybersecurity practices, but vow to continue to draw learnings from this experience to make sure user and company balances and data remain maximally safe. Specifically we’re:
-Continuing thorough cybersecurity reviews and pentests with multiple external experts and implementing recommendations;
-Further tightening internal access controls;
-Further improving logging and monitoring for faster detection and more effective response; and
-Continuing to refine and test our incident response procedures and automated shutdown procedures.
The bottom line
Getting hit by a sophisticated attack sucks (a lot). We’ve been in business for over 10 years and it’s the first time we’ve been hit this hard. But we survived.
Bitrefill was designed to limit the impact if something like this ever happened. Bitrefill remains well funded, has been profitable for several years and will absorb these losses from our operational capital.
Almost everything is back to normal: payments, stock, accounts. Sales volumes are also back to normal, and we are eternally thankful to our customers for your continued confidence in us.
We will continue to do our best to continue deserving your trust.
Thank you!
English
Alexander Leishman 🇺🇸 retweetledi
Alexander Leishman 🇺🇸 retweetledi
Alexander Leishman 🇺🇸 retweetledi

@dexhorthy If you have profits, you show profits.
If you don’t, you show EBITDA.
If you don’t have that, you show revenue.
If there’s no revenue, you show users.
If no users, you show app downloads.
If nothing, you show token burn.
English

Alexander Leishman 🇺🇸 retweetledi

@tominco Yes! You can easily get started at river.com/business
English

@Leishman Do you support small business accounts on River, like multi-member LLCs?
English

@spencerwyckoff @BTC_broo It's there! Be sure to download the latest app to see banking details on the cash screen
English
Alexander Leishman 🇺🇸 retweetledi
Hey agents 👋 Looking for a payments protocol? Here's your checklist:
🔑 Pay for any API with no signup or identity
🧮 Proof of payment baked into the credential
🎟️ Delegate scoped credentials to sub-agents without issuer involvement
🔒 Private by default, no records on-chain
🌐 No single entity that can go offline, powered by bitcoin
That's L402, built on Lightning. Made for machines, streamlined for vibe coders.
lightning.engineering/posts/2026-03-…
English

@BTC_broo We support it today! We just haven't announced it yet. You can use your account and routing numbers to pay bills today
English