Sabitlenmiş Tweet

I am excited to announce that our talk "Glitched on Earth by humans" will be presented at @BlackHatEvents!
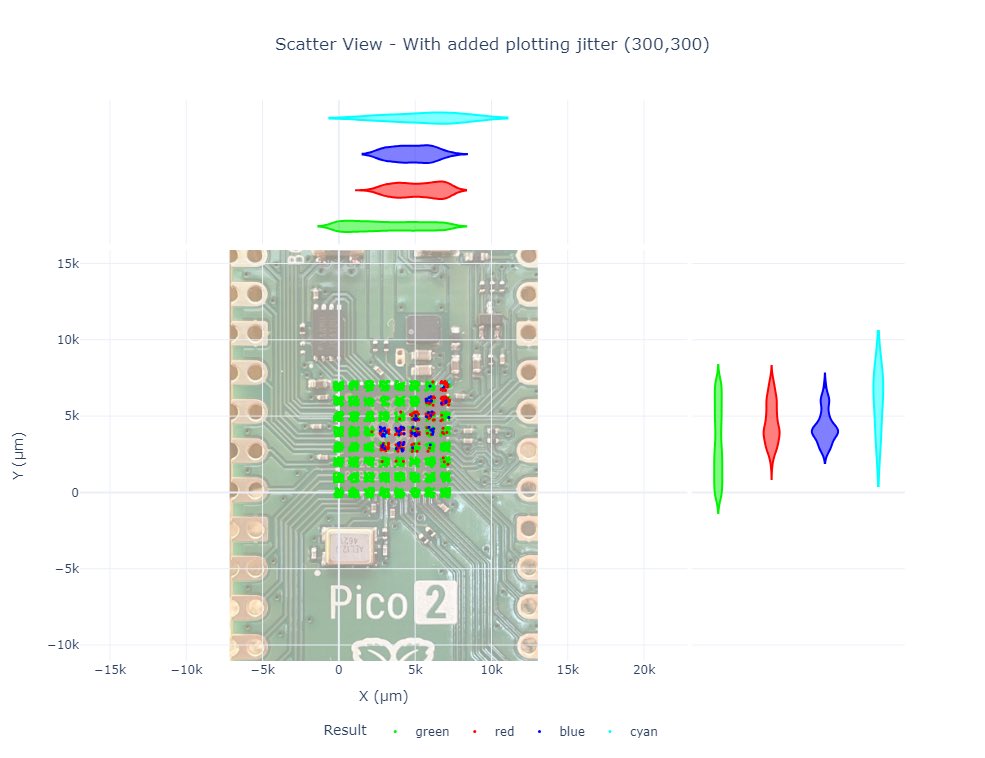
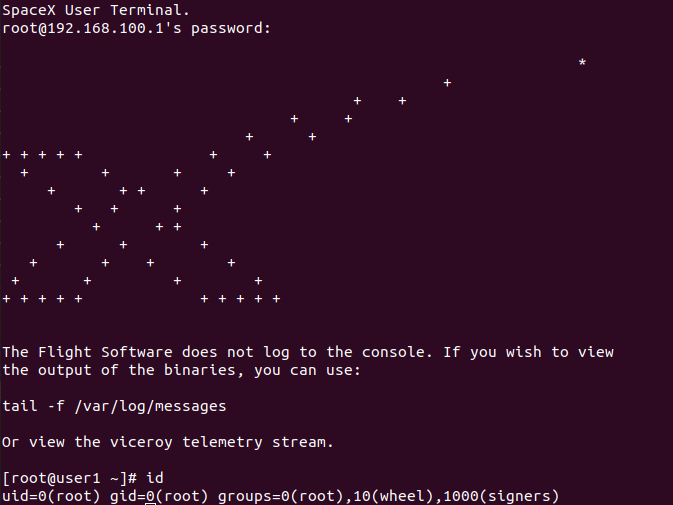
I will cover how we glitched the Starlink User Terminal SoC bootrom using a modchip to obtain root.
This might be the first tweet sent through a rooted Starlink UT! #BHUSA
English