m0z
2.7K posts

m0z
@LooseSecurity
The greatest trick the devil ever pulled, was convincing the world that cyber security existed.





@terjanq @arturjanc Yep let's begin to reward the greatest anti-AI writeup. Whoever can make the funniest incorrect writeup for a challenge gets a prize.


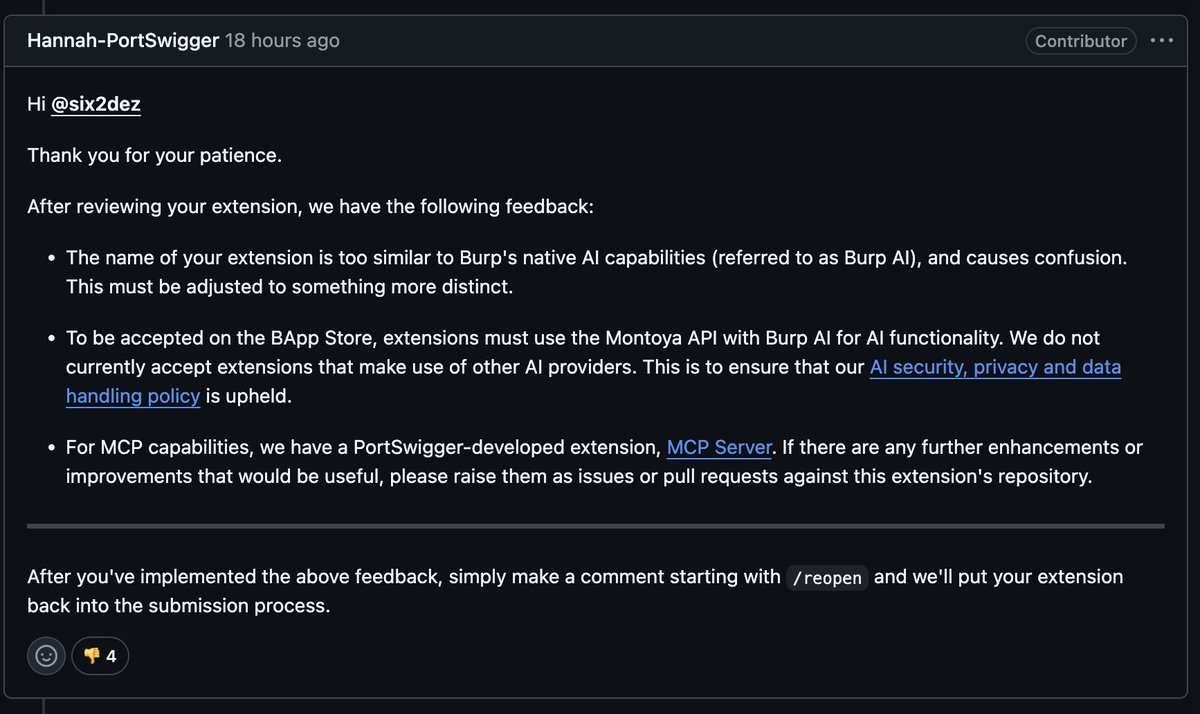
📢 Interested in AI and agent security at Google🛡️? This post looks at how we mitigated the risk of URL-based data exfiltration through provenance checks and sanitization – effectively blocking a prompt injection-based exploitation vector. bughunters.google.com/blog/mitigatin…







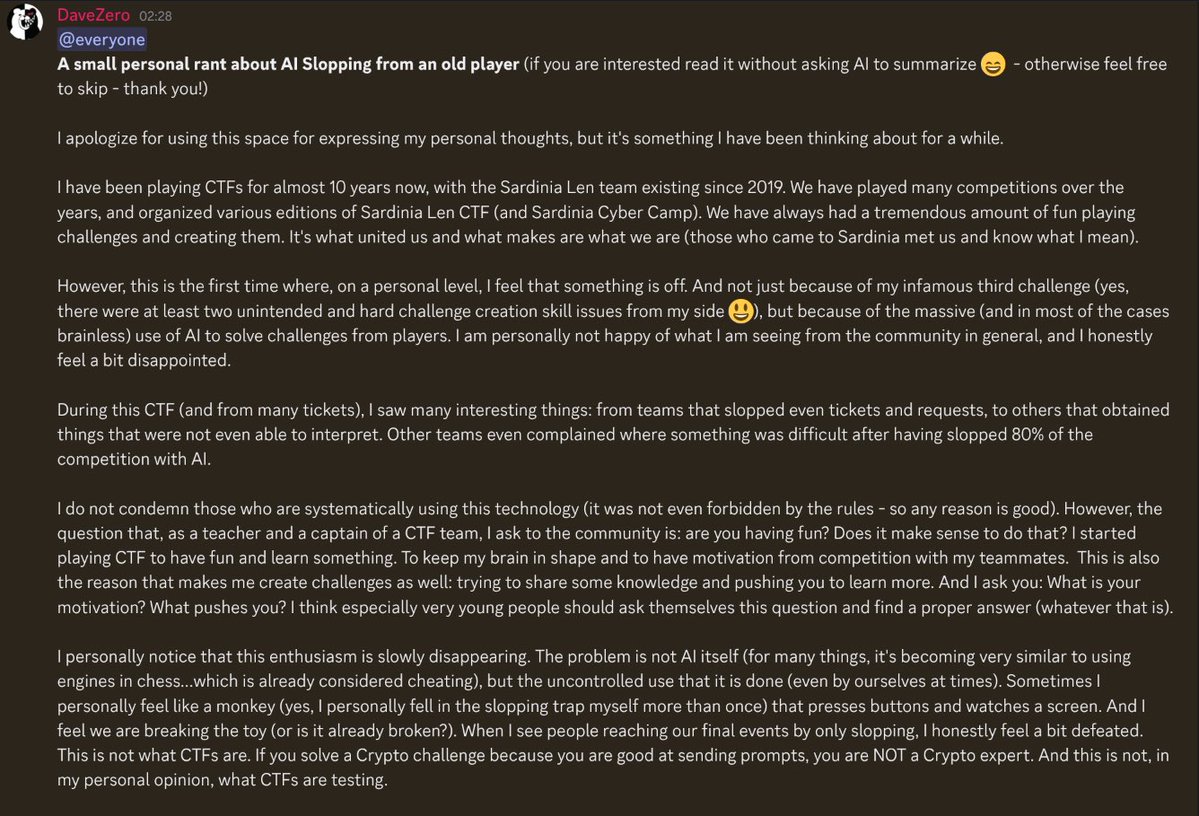
What I’ve always found amazing about CTFs is that "flag is flag". Whether you found an unintentional solve or pwned the browser with n-day for a XSS challenge, it didn't matter. I totally get the frustration of AI, but there is no solution other than accepting the change.



I started playing CTFs in 2022, and LLMs definitely changed the **competitive** CTF scene a lot, especially since mid-2025. I also started using LLMs in late 2025. Yes, those models did one-shot many challenges, but what's the fun of slopping them? I learned absolutely nothing 🥲