Sabitlenmiş Tweet
MarketingWaterhole
28.6K posts


MarketingWaterhole retweetledi
MarketingWaterhole retweetledi
MarketingWaterhole retweetledi

🚨 Tweet #11: The weapon they built is called Pythia.
Built at Georgia Institute of Technology. Funded by the Defense Advanced Research Projects Agency.
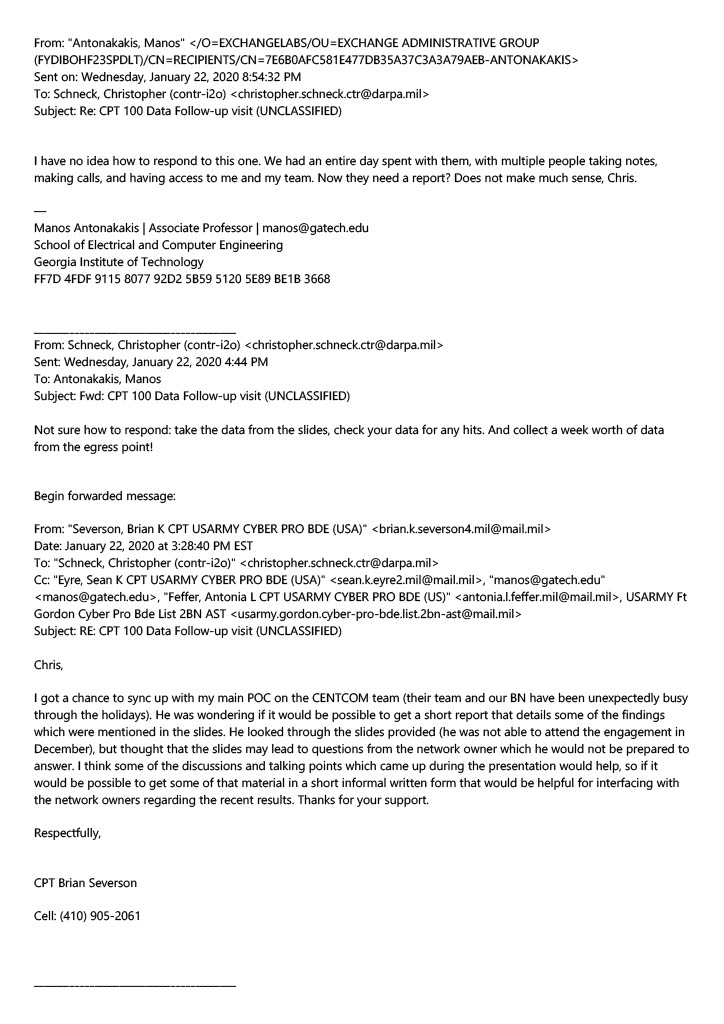
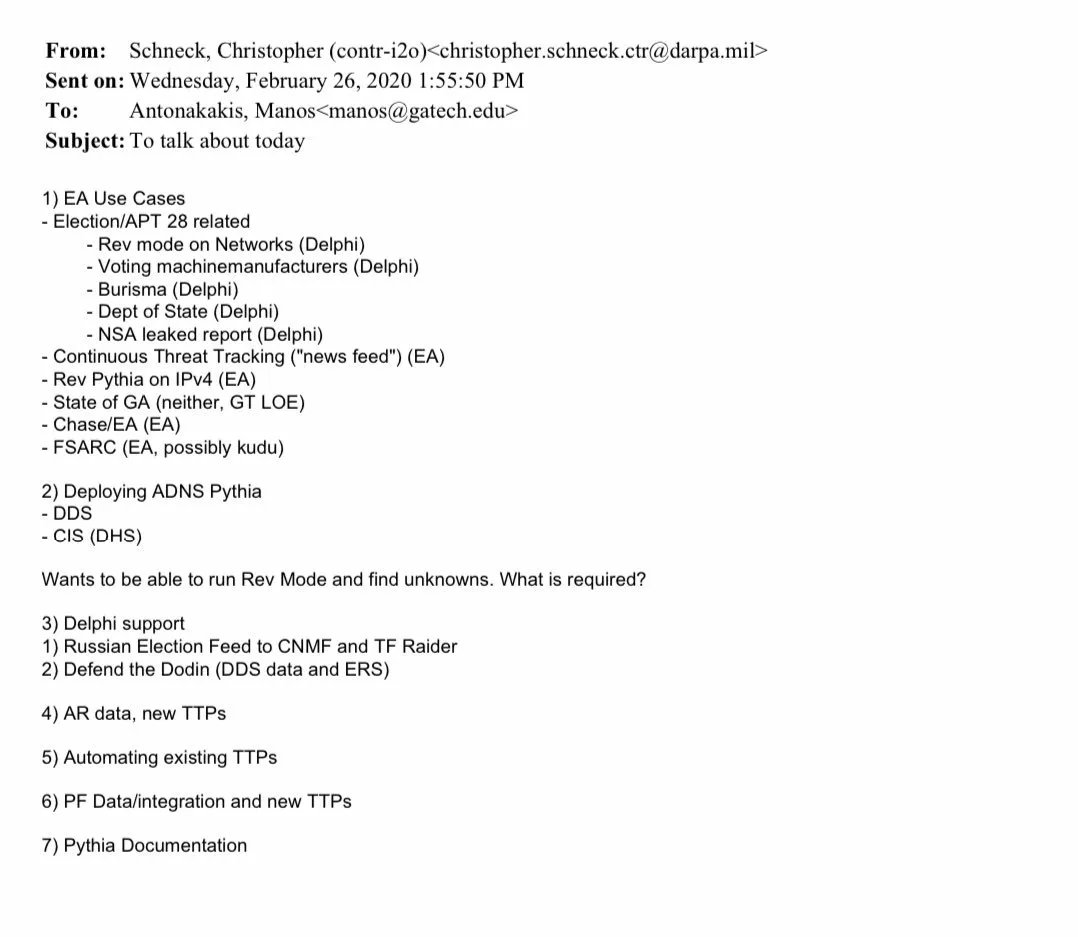
But this is not theory. We have the Defense Advanced Research Projects Agency's own internal planning document - a working agenda sent by Defense Advanced Research Projects Agency contractor Christopher Schneck to Professor Manos Antonakakis on February 26, 2020 - eight months before the 2020 election.
Read what is on that agenda. Word for word:
"Deploying Active Domain Name System Pythia - Defense Digital Service / Department of Homeland Security"
"Wants to be able to run Reverse Mode and find unknowns."
Translation for non-technical readers:
Pythia was being embedded inside the Department of Homeland Security, the very agency responsible for declaring elections secure, with the specific goal of running Reverse Mode.
Here is what Reverse Mode does in plain language:
You pick a target network - say, a voting machine company.
Once inside a network, and the documents confirm Pythia was deployed inside the Department of Homeland Security by February 2020, Pythia maps every single connection on that network. Public or private. Internal or external. There is nowhere to hide.
Who is accessing it.
From where.
At what time.
Through what pathway.
Encryption does not hide this.
Firewalls do not block this.
Because Pythia operates at the Domain Name System layer: the foundational address system every internet-connected device must use to function. There is no way around it.
And here is what else is on that same Defense Advanced Research Projects Agency agenda - listed as Reverse Mode targets:
✅ Voting machine manufacturers
✅ Burisma - the Ukrainian energy company
✅ Department of State
✅ National Security Agency leaked report
✅ State of Georgia - its own separate line item
All of this. On one Defense Advanced Research Projects Agency planning document.
Eight months before you voted.
And United States Army soldiers were trained on this weapon at Georgia Tech's campus.
One of those soldiers wrote this to Professor Antonakakis after his training:
"Thanks for hosting the Pythia training a couple of weeks ago. It was very interesting seeing the tool in action."
The Army unit's motto: 'Pierce the Shadows.' They were not kidding. Captain Severson's email signature contains the Second Battalion Cyber Protection Brigade motto: "Pierce the Shadows." It is in the document.
In Ancient Greece, Pythia was the Oracle of Delphi. Nice documents @TheAndersPaul - he obtained them via public records requests and hit gold.

English
MarketingWaterhole retweetledi

🚨 Tweet #12: This is the document that proves it was all planned.
Defense Advanced Research Projects Agency contractor Christopher Schneck sent this email to Georgia Tech Professor Manos Antonakakis on February 26, 2020.
Eight months before the presidential election. Subject: "To talk about today."
It is a working agenda. Decoding every line:
Item 1: Enhanced Attribution Use Cases
Enhanced Attribution is the Defense Advanced Research Projects Agency program funding Georgia Tech to identify and track cyber attackers using internet traffic data.
Listed under "Election / Advanced Persistent Threat 28 related"
Advanced Persistent Threat 28 is the code name for Russian Military Intelligence. That label is the legal justification attached to everything below.
It converts domestic surveillance into a national security operation.
Now look at what is listed underneath that label:
✅ "Reverse Mode on Networks (Delphi)"
Delphi is the Georgia Tech surveillance platform. Reverse Mode means: pick a target network and map every single connection going into it and leaving it.
✅ "Voting Machine Manufacturers (Delphi)"
Dominion Voting. Election Systems and Software. Hart InterCivic. The companies that make the machines that count your votes. Targeted for reverse mode network surveillance. Eight months before the election.
✅ "Burisma (Delphi)"
The Ukrainian energy company at the center of the Biden family controversy. On the same Defense Advanced Research Projects Agency targeting list as voting machine manufacturers.
✅ "Department of State (Delphi)"
The United States State Department. Also a Delphi reverse mode target.
✅ "National Security Agency Leaked Report (Delphi)"
An actual National Security Agency intelligence leak being analyzed by a university professor under a Defense Advanced Research Projects Agency contract.
✅ "Reverse Pythia on Internet Protocol Version 4 (Enhanced Attribution)"
Running Pythia's reverse surveillance mode across the entire public internet address space. Every device. Every connection. Simultaneously.
✅ "State of Georgia (neither, Georgia Tech Level of Effort)"
Georgia gets its own separate line. Not running under the Russian threat label. Not running under Enhanced Attribution. Running under Georgia Tech's own funded effort. Meaning it operates outside standard Defense Advanced Research Projects Agency program oversight entirely.
✅ "Chase / Enhanced Attribution"
JPMorgan Chase bank. Being monitored under the same program as voting machine manufacturers.
Item 2: Deploying Active Domain Name System Pythia
The total internet surveillance weapon described in Tweet #11 was being deployed to two locations:
Defense Digital Service: the Pentagon's own internal technology unit.
Center for Internet Security / Department of Homeland Security: the federal agency responsible for protecting election infrastructure.
The same agency that later declared the 2020 election "the most secure in American history." More solid evidence Chris Krebs lied through his teeth!
The note reads: "Wants to be able to run Reverse Mode and find unknowns. What is required?"
The Department of Homeland Security wanted Pythia's reverse surveillance capability deployed inside their own walls. They were asking Georgia Tech what it would take.
Item 3: Delphi Support
"Russian Election Feed to Cyber National Mission Force and Task Force Raider"
Cyber National Mission Force is the United States military's offensive and defensive cyber warfare unit. The cyber equivalent of Special Forces.
Task Force Raider is a military cyber task force.
Intelligence derived from surveilling voting machine manufacturers and election networks was being fed directly to military cyber warfare units in real time.
"Defend the Department of Defense Information Networks"
The same surveillance infrastructure protecting military networks was also watching election infrastructure. Same team. Same tools. Same data pipeline.
Item 7: Pythia Documentation
They were writing the manual for this weapon.
Now read this entire email again knowing one thing:
The Defense Advanced Research Projects Agency contractor who sent this agenda is the same man who later wrote to the same Georgia Tech professor:
"Collect a week worth of data from the egress point."
That was Tweet #2. The email that started this entire thread. The one with the 2 red highlight rectangular boxes we inserted.
It was not random. It was not accidental.
This document proves it was a coordinated, pre-planned, institutionally authorized operation targeting voting machine companies, Georgia specifically, and the Biden family's business partners: eight months before the 2020 presidential election.
And the Department of Homeland Security - the agency that declared your election secure - had this weapon deployed inside their own walls.
Tweet #13 will show you what happened when they pointed it directly at Dominion Voting thirteen days before Election Day: and the exact words a Georgia Tech professor typed when he saw what came back.
English
MarketingWaterhole retweetledi

🚨 Tweet #13: October 21, 2020.
Thirteen days before the presidential election.
Two Georgia Tech professors are running their Defense Advanced Research Projects Agency surveillance tool against voting machine manufacturer networks.
Remember Tweet #12. The planning document.
Voting machine manufacturers were an authorized Delphi target. This was not accidental. This was the operation executing exactly as planned.
Here is what happened when the results came back.
Professor Angelos Keromytis typed four words:
"It's Dominion Voting."
Professor Manos Antonakakis typed six words:
"Oh, shit. These look like egress points."
A Defense Advanced Research Projects Agency funded professor. Running authorized surveillance on voting machine networks. Thirteen days before you voted.
And when the data came back he typed "Oh, shit."
That is not the reaction of someone who found nothing.
That is not the reaction of someone who found what they expected.
That is the reaction of someone who found something that even he was not prepared to see.
Now understand what "egress points" means in plain language.
An egress point is a place where data leaves a network and goes somewhere else.
On a properly secured voting machine system there should be no egress points. The machines are supposed to be air gapped. Meaning completely isolated from the internet and all outside networks.
Our election officials however have been lying to us, as first off they don't even know what a true air gap - and - their voting systems don't have them. It pretend theater.
Eric Coomer told the court the machines had no "direct" connection to the internet.
Notice he said "direct."
The egress points his own colleagues found in the network data thirteen days before the election suggest the machines had something other than a direct connection.
And notice something else.
Before Antonakakis typed "Oh, shit" he wrote:
"Let me check something..."
Then he posted a link to the United States Election Assistance Commission's official government page listing all registered voting equipment manufacturers.
He was cross referencing what he found in the live network data against the official government registry of voting machine companies.
He was confirming the identity of what he was seeing in the data.
He confirmed it. Then typed what he did.
These are not the emails of people passively watching foreign adversaries attack American systems.
These are the emails of people who just found something unexpected inside American voting infrastructure.
Thirteen days before the election.
-Who did they tell?
-What did they do with what they found?
-Why has none of this ever been publicly disclosed?
Tweet #14 will show you the document that connects all of this directly to the highest levels of the United States Senate and Special Counsel John Durham's own investigation.
Professor Manos Antonakakis of GAtech:


English
MarketingWaterhole retweetledi

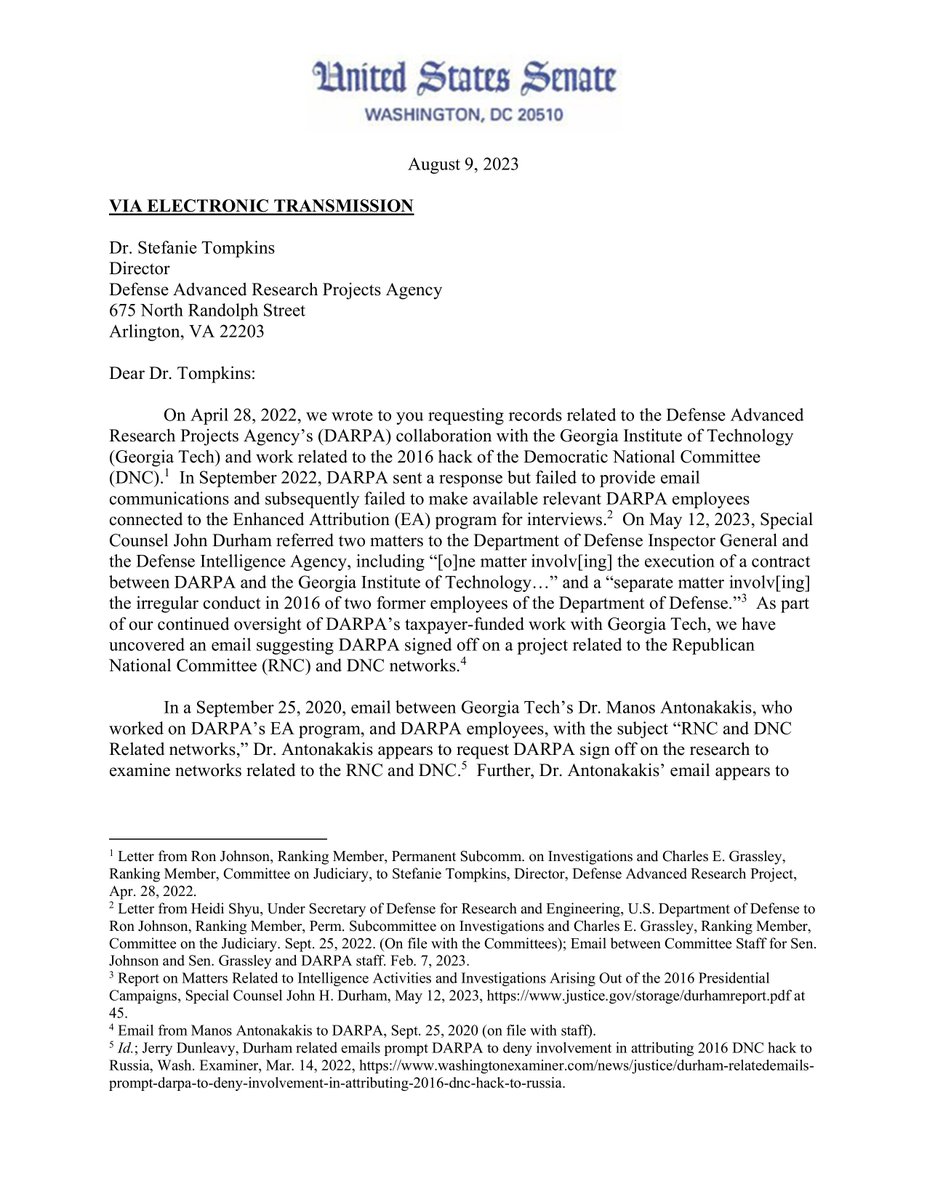
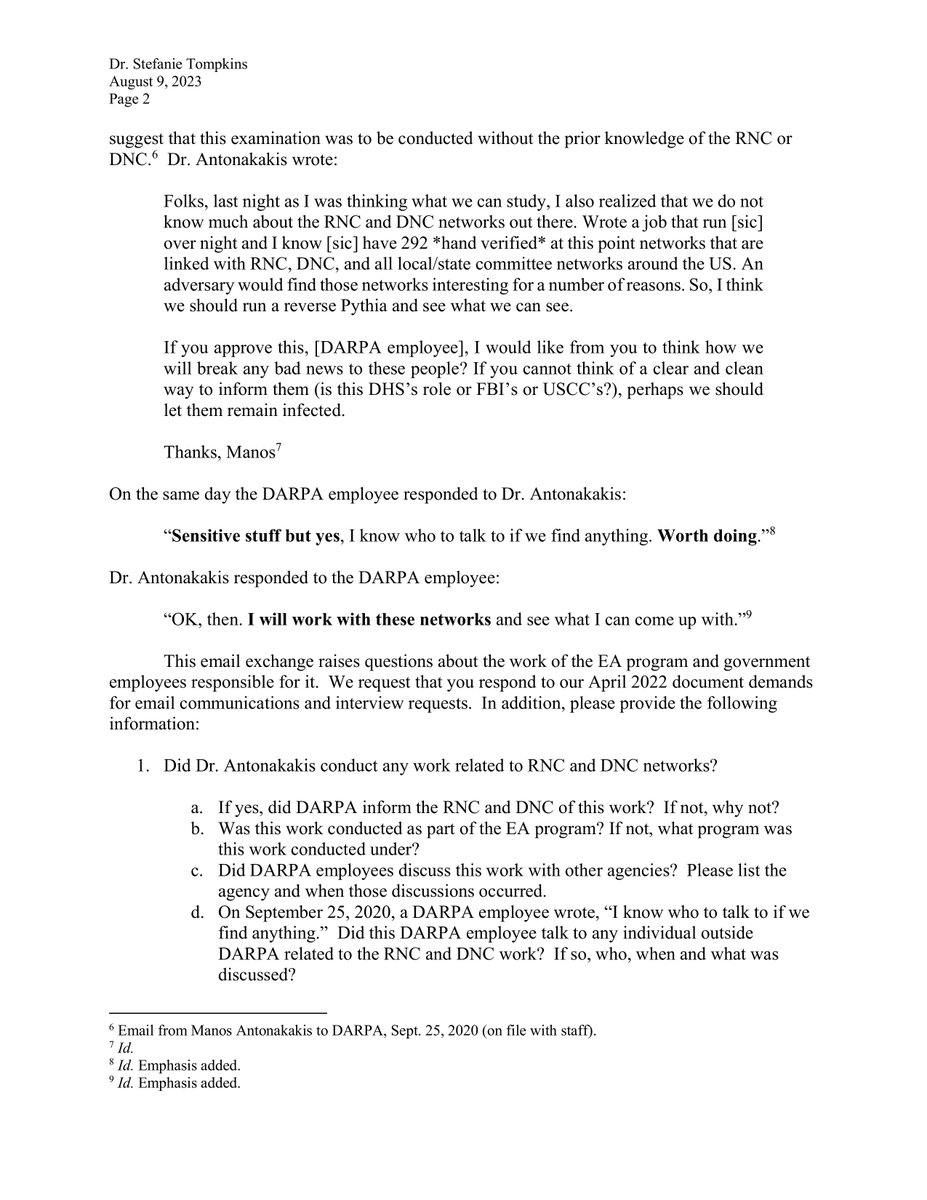
🚨 Tweet #14: What you have read in this thread is not new to everyone.
Two United States Senators already knew.
And Special Counsel John Durham already knew.
Here is what they found and what they did about it.
United States Senator Chuck Grassley of Iowa and United States Senator Ron Johnson of Wisconsin uncovered email evidence of Professor Manos Antonakakis's Defense Advanced Research Projects Agency funded work.
What they found in those emails stopped them cold.
A Defense Advanced Research Projects Agency employee - referring to the Georgia Tech operation - wrote this:
"Sensitive stuff worth doing."
Same Defense Advanced Research Projects Agency (DARPA) employee. Same email chain. Same date as the United States Postal Service swing state scanning email — September 25, 2020:
"I know who to talk to if we find anything."
Not "I know who to report it to."
Not "I know who to alert."
But "I know who to talk to if we find anything."
That is not the language of a defensive cybersecurity operation protecting elections.
That is the language of an intelligence operation with a predetermined recipient for whatever was found inside American voting infrastructure.
Who was that person?
That question has never been answered publicly.
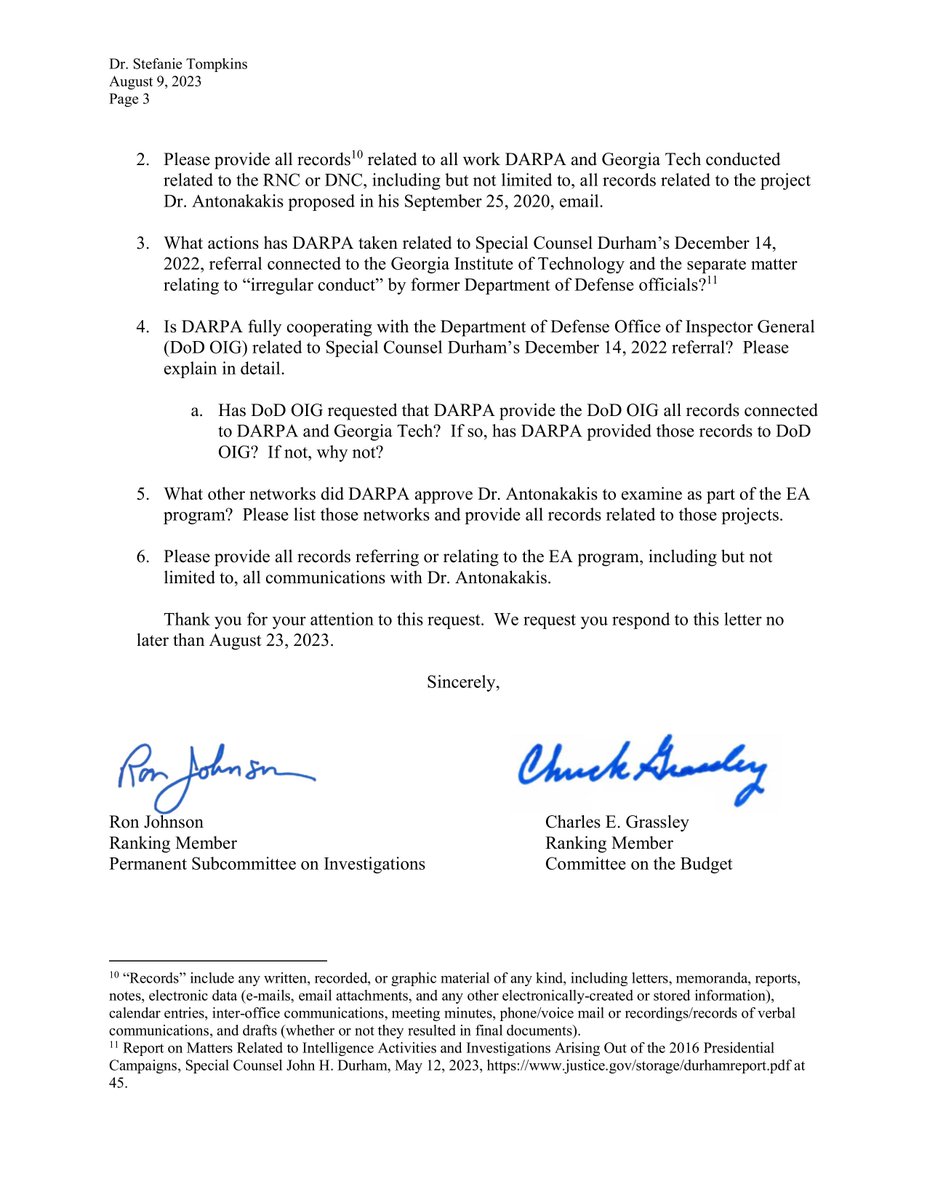
Now add this. Special Counsel John Durham completed his investigation in May 2023.
In his final report Durham made a criminal referral to the Department of Defense Inspector General.
That referral specifically identified:
"One matter involving the execution of a contract between the Defense Advanced Research Projects Agency and the Georgia Institute of Technology."
One sentence. In a Special Counsel report to the United States Congress.
The Defense Advanced Research Projects Agency. Georgia Tech. A specific contract. Referred for potential criminal investigation.
Durham found something significant enough in that contract to send it to the Department of Defense's own internal investigator.
The Department of Defense Inspector General received that referral.
What happened next has never been made public.
-No findings were announced.
-No charges were filed.
-No report was released.
-The referral vanished.
Now look at what you have seen in this thread:
A Defense Advanced Research Projects Agency planning document targeting voting machine manufacturers.
Active surveillance of Dominion Voting network traffic thirteen days before the election.
Egress points found in voting machine infrastructure.
Russian and Iranian command and control confirmed in state and local election networks.
An Army unit trained on the surveillance weapon used to do all of this.
We caught the US Army inside a Dominion EMS.
A Defense Advanced Research Projects Agency employee who knew exactly "who to talk to" if anything was found.
And a Special Counsel referral to the Department of Defense Inspector General that quietly disappeared.
Two United States Senators saw enough to raise alarms.
The top prosecutor in America saw enough to make a criminal referral.
You were never told any of it.
Look at what US Senators Ron Johnson and Chuck Grassley were after in their (second) letter to DARPA:
English
MarketingWaterhole retweetledi

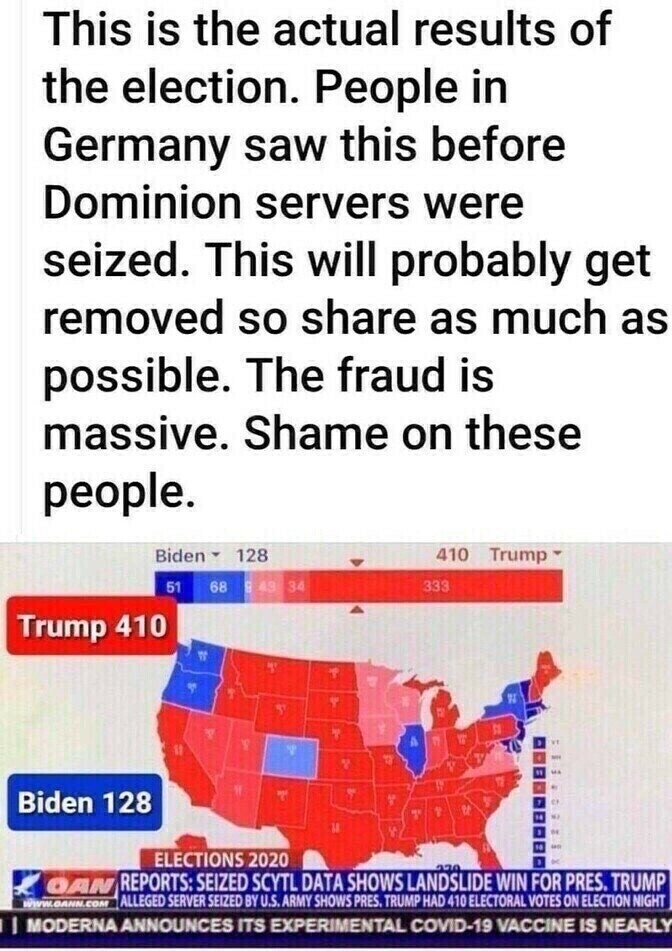
@PeterBernegger Didn’t Tina Peters have the goods that would blow the lid off the whole thing? She recorded the true results before the machines were reset with the manipulated results. There should be a federal inquiry brought about this case by the DOJ?
English
MarketingWaterhole retweetledi

President Trump knows how our elections were stolen. He knows who did it. I'll tell you now (again) who the head of the snake is:
it's the CIA, along with countless tentacles making a very long list.
Which makes it sovereign fraud, as I've been publishing about and stating in my speeches for years.
Arrests are coming - for timing see my Tweet of June 20th, 2025. Thousands of arrests, personally I think it will be over 10,000 arrests. That's how bad it is and why it is taking longer than anyone wants. People have been flipping though. Its international, national then down to your local election officials (the corrupt ones).
Countless politicians are in on it. Mainly democrats but many republicans also (not much if any difference).
It was/is treason along with a host of other crimes such as sedition, conspiring to defraud the US Government.... the list goes on and on. They wanted to control the world. The USA was standing in their way.
Noting the statute of limitations has not run out where there are many felony crimes which have 10 year statute of limitations, for example. Another example - most are unaware that crimes involving foreign evidence requests (MLATs), can extend 5 year limits another 3 years. There are more.
I and many others are burning the midnight oil to provide as much information as possible to help in bringing these sick psychos to justice.
(part 3 of 4 of the other series still coming....busy busy)

English
MarketingWaterhole retweetledi

MarketingWaterhole retweetledi

Stealing an election was a gamble.
A serious and dangerous one.
The globalists put all their money on the distraction of the plandemic, the brainwashed left, and a strategically placed and weaponized judiciary to hold the election “legitimacy line,” no matter what evidence of fraud came to light.
They cheated not just in one big way, and not only in swing states. That would have been too obvious.
They cheated in every way possible, with mail-in ballots, Dominion tabulations, and while “counting” votes.
But because all pre-election polls were intentionally manipulated to make the steal less alarming, they had no way to predict how many legal votes for Trump there would be.
THIS WAS THE BIGGEST FLAW IN THEIR PLAN!
Fast-forward to election night…
Things were immediately crazy. Trump was doing well all over the map, even in states considered Trump-proof.
Trump was approaching record-breaking territory.
The cheaters should have paid more attention to the pre-election Trump support in California. (If they followed me here, they would have!)
But they were too busy planning the steal to worry about ACTUAL Trump support.
The LEGAL ballots were irrelevant… until election day.
They had to load thousands of Biden faux ballots in unexpected places, which drove up the total to unexpected levels.
Then, the linchpin: Fox News called Arizona for Biden immediately, even with a large Trump lead.
It was the APB to all involved in the steal.
Someone made a call and shut down counting in states that needed time to usher in fake, no-crease “mail-in Biden ballots” and make adjustments to the Dominion counts, feeding and re-feeding Biden ballots over and over.
Who the heck made that call?
Maybe ask Bret Baier or Martha.
Remember the “water main emergency” in Georgia that somehow lined up with the shutdown of counting in multiple states and later, wasn’t a water main emergency?
What? Come on, now…
People went to bed with Trump leading and woke up to an 81-million-vote victory for the guy who hid in his basement.
Those of us who watched the chaos throughout the night saw Trump LOSE tens of thousands of votes, not just once but several times, and on live TV.
The election results were a sloppy, unbelievable mess, and the election crimes were random, like panic-driven carelessness often is.
But this randomness also saved the globalists from immediate exposure.
Then, the fallout began, first as a trickle, then a flood.
Over 2,000 affidavits were filed (then ignored) by election workers (both parties, under penalty of perjury) who saw irregular activity.
Videos surfaced of ballots by the thousands being dropped off at dark docks late at night at locations where we’d been told counting had stopped and workers went home.
Who let these ballot-droppers in with their “special delivery”?
Then there was the impossible, non-partisan math.
Sadly, a disturbing percentage of US citizens were—and still are—okay with a stolen election as long as Trump is not President.
There is NO SUCH THING as a FREE country without FAIR elections.
@LeaderJohnThune PASS THE SAVE AMERICA ACT!

English
MarketingWaterhole retweetledi
MarketingWaterhole retweetledi
MarketingWaterhole retweetledi

@GinaSaysSo All conspiracy bull. All of it. Educate yourselves instead of 1A blabbering all the time.
English
MarketingWaterhole retweetledi

@DadirriHealing Well it happened on live tv. That's not disputed. I am well researched and stand by what I post here. Buzz off if you don't like it. Free country and all. I promise not to find you. Healer? Yeah. Okay.
English
MarketingWaterhole retweetledi

@GinaSaysSo Vote tally’s never reverse. Used to work elections for tv station. Never have I seen that.
English
MarketingWaterhole retweetledi

@GinaSaysSo Raffensperger and Abrams wallpapered the state of GA with mail in ballots. Someone’s cat got a ballot!! I lived in GA for 40 years and until 2020 you had to request a mail in ballot in writing. 2020 we got 2 for my husband and 2 for me. Neither of us requested them!! We knew!!
English
MarketingWaterhole retweetledi

@GinaSaysSo @JanCall01931980 They had to get a couple red states (Georgia and Arizona) in on it because only relying on Pennsylvania, Michigan and Wisconsin wasn't enough. If Trump won AZ and GA, Biden would need all 3 of those states to win. Without WI he could have gotten 270 but that's way too close.
English