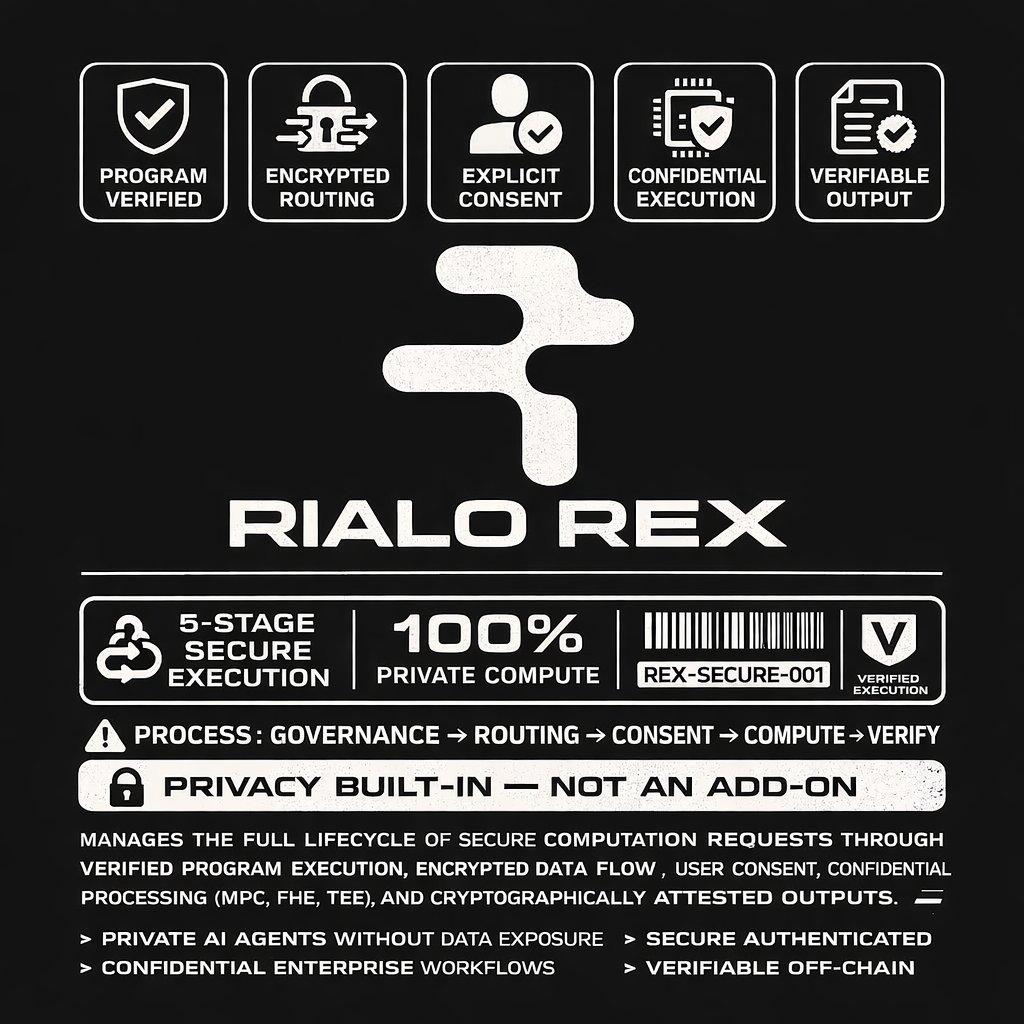
MPC. FHE. TEEs. All powerful on their own, but none solve the coordination problem. The hard part isn’t just encrypting computation; it’s the orchestration required to make it functional and secure. That’s what Rialo Extended Execution (REX) does. REX is a protocol-level orchestration system for confidential computation that manages the entire lifecycle of a secure request: Program Governance – Programs to be executed are verified and approved for specific execution runs before they ever touch the core. Encrypted Routing – Encrypted inputs are routed cryptographically to a computation core only after the appropriate program logic is loaded. Explicit Consent – Computation is performed only after explicit authorization from both the application and the user, enforced by strict policy. Confidential Compute Core – Secure execution using MPC, FHE, or TEEs, including protected Web2 API calls within an isolated environment. Verifiable Outputs – The system generates and verifies cryptographic attestations that prove a specific computation was correctly executed before routing the result to its destination. REX transforms Rialo into infrastructure for real-world secure computation: Private AI agents that process personal data without seeing it. Sensitive enterprise workflows that maintain competitive secrecy. Authenticated API automation for secure, off-chain interactions. Verifiable off-chain compute with immutable on-chain guarantees. This is native privacy at the protocol layer. Get Real. Get Rialo.