Merulez
409 posts

Merulez
@Merulez99
🛡️Security Researcher | Co-founder @ValvesSec
Katılım Ocak 2022
529 Takip Edilen359 Takipçiler
Sabitlenmiş Tweet
Merulez retweetledi

We’ve got some exciting things coming to EZManger in the next few weeks with this audit! @ValvesSec has been incredible throughout the process, and we’re happy to trust them to make EZManager as secure as possible.
Valves Security@ValvesSec
Valves 🤝 EZManager (@EZManagerCL ) EZManager tracks every position lifecycle. From opening and rebalancing to capital changes, compounding, and collections. We are going to ensure their contracts meet the highest security standards 🫡
English
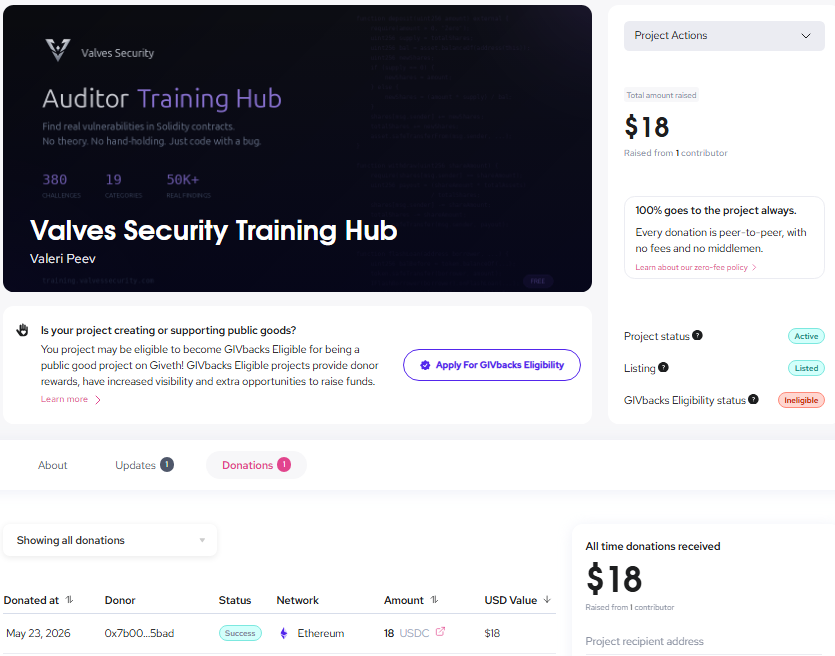
Someone just made the first donation to our Valves Security Training Hub on Giveth.
$18 from an anonymous contributor.
It may look small, but honestly this means a lot.
We spent countless hours building this because we wanted aspiring auditors to have a free place to train on real vulnerability patterns, not just random CTF puzzles.
Just a resource we wish we had when we started.
To whoever donated: thank you.
And to everyone supporting, sharing, testing, or learning from the hub - you are the reason we keep building this.
giveth.io/project/valves…
English
The goal was never to look like the biggest audit firm.
The goal is to be the team founders trust when they want honest, deep, no-BS security work before launch.
That’s what we’re building with Valves Security.
Valves Security@ValvesSec
We're on a mission to save millions (potentially billions) in exploits over the next 365 days. Big names in the space already trust us with their protocol security. Your codebase deserves the same level of protection🛡️ Book an audit now: valvessecurity.com/audit
English
Merulez retweetledi

We're on a mission to save millions (potentially billions) in exploits over the next 365 days.
Big names in the space already trust us with their protocol security. Your codebase deserves the same level of protection🛡️
Book an audit now: valvessecurity.com/audit
English
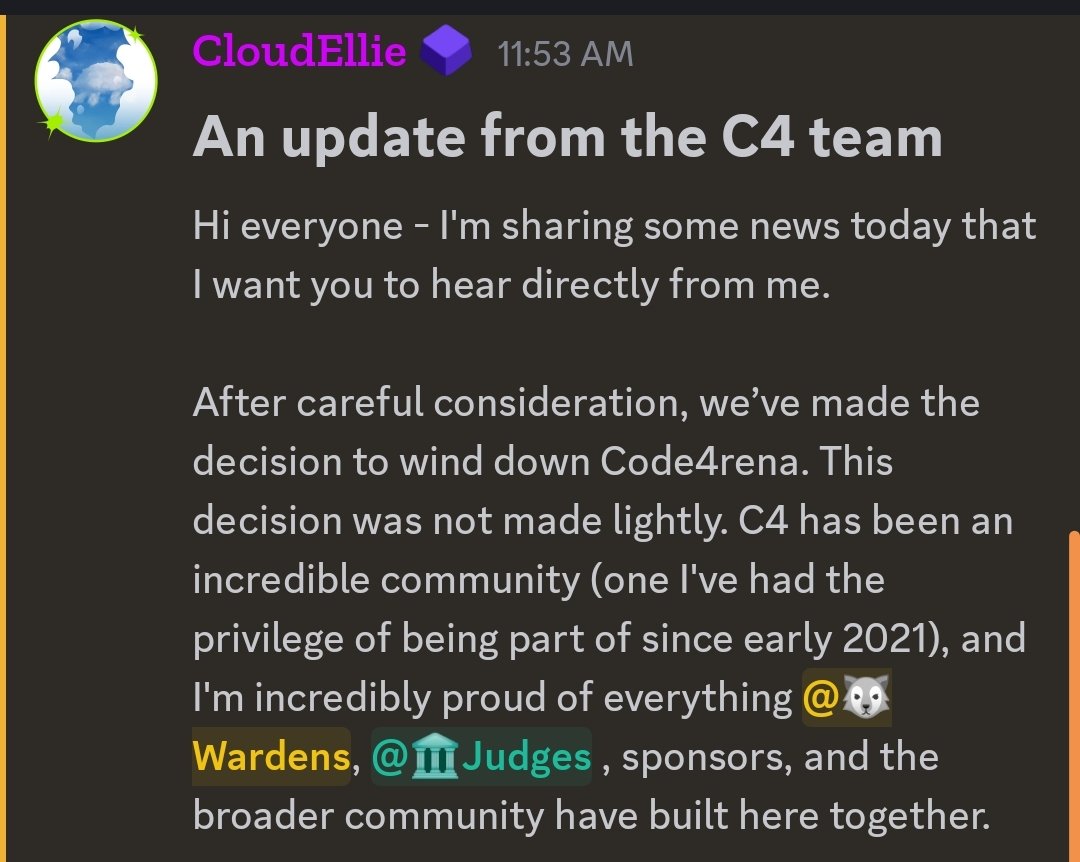
Code4rena winding down does not make contest results worthless.
But it does change the lesson.
For years, contest placement was one of the cleanest public signals that someone could find bugs under pressure.
That still matters.
But in private audits, the harder skill is different:
- Can you explain the issue clearly enough that the team fixes it correctly the first time?
A leaderboard proves speed.
Client trust proves judgment.
You need both.
English
Merulez retweetledi

Not great for just one year... 😤
We should all do much better!
At @ValvesSec we’re stepping up. We are going to save millions in exploits over the next 365 days.
You should do the same.
Let’s secure this whole space together. 🔥

English
Merulez retweetledi

Valves 🤝 EZManager (@EZManagerCL )
EZManager tracks every position lifecycle. From opening and rebalancing to capital changes, compounding, and collections.
We are going to ensure their contracts meet the highest security standards 🫡

English
Merulez retweetledi
Merulez retweetledi

Hands-off farming is here! Agent Max automatically opens positions on MaxFi, making it even easier than before. Get ready for the MaxFi seed round next week! #DeFi #AutomatedTrading
English

@Vesko_210 auditor sign-off matters yeah. but framing 'non-auditor used AI' misses that auditors using AI as scaffold ship faster. AI accelerates the audit instead of replacing it. the value layer is human accountability + AI throughput together. neither alone covers millions.
English
Merulez retweetledi
@Vesko_210 It's like saying everyone who has a camera is a professional photographer 🤡
English
Merulez retweetledi
Merulez retweetledi

@Merulez99 I still dont understand why but he also have couple of confirmed findings this way
English