Miasm
70 posts

Miasm retweetledi

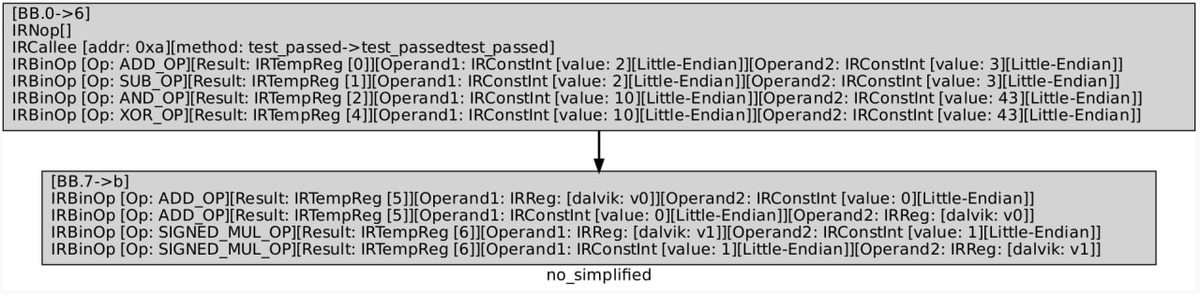
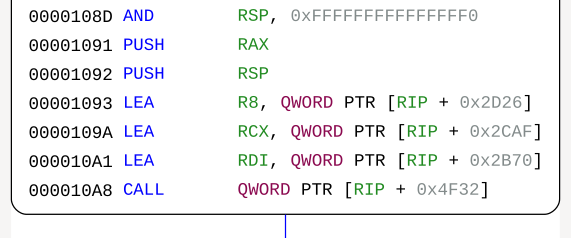
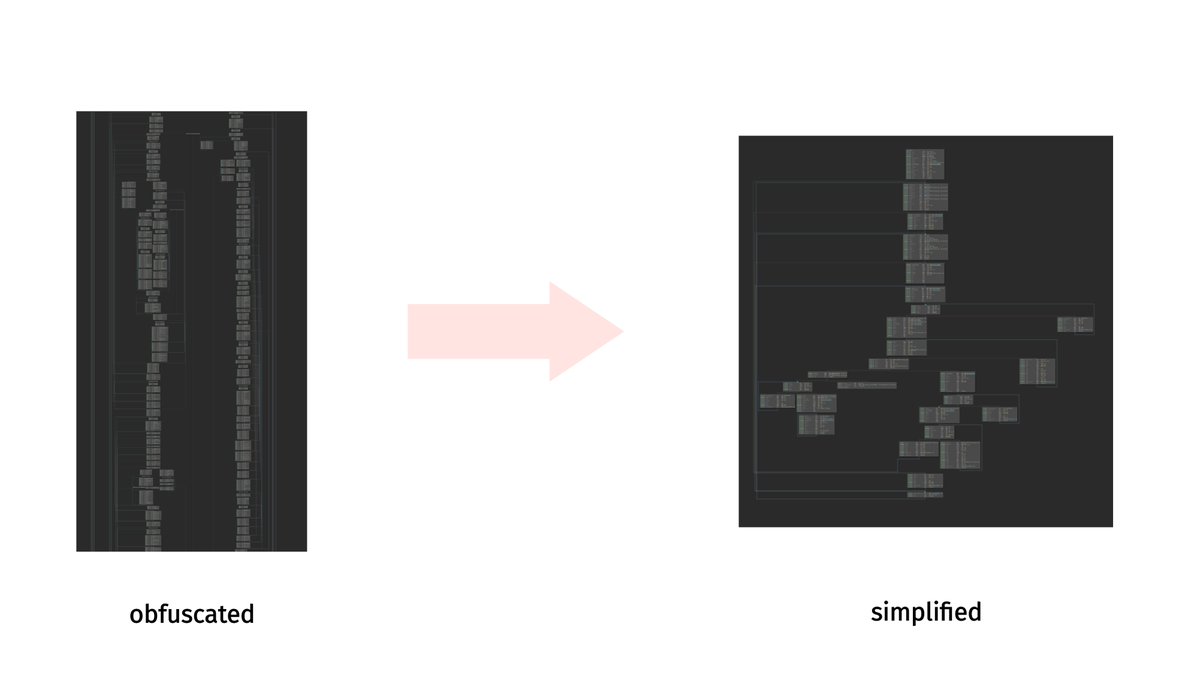
While there are several frameworks for #reverseengineering that provide features we needed to see
through Wslink’s virtual-machine-based obfuscator, we used @MiasmRe in this project simply because
it’s actively maintained and we’re already familiar and satisfied with it. 4/5
English
@_trou_ It's more and more difficult to "manually" address problems generated by tools : 25 years ago, obfuscation, optimizations or even program size had "human size". Now, most of them are tool generated (even source code). So we also have to use tools to be able to solve them.
English
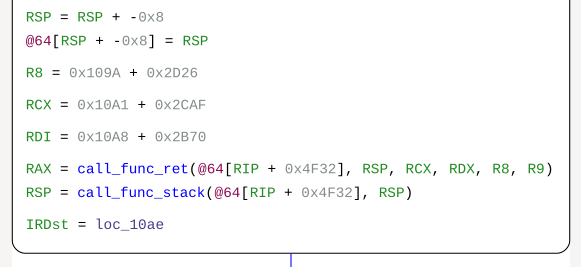
Little update: based on the great @NCCGroupInfosec blog post (research.nccgroup.com/2021/10/12/a-l…), we added color support for IR and ASM graph output: Thank you guys !
English
Miasm retweetledi

I finally decided to publish my complete toolset written for Tinynuke analysis
You'll find config and injects grabber, dll extractors, Ghidra deobfuscation scripts and @cea_sec miasm based scripts
github.com/Heat-Miser/tin…
#Tinynuke #ReverseEngineering #Malware
English
@crackin76726107 Hum, as Miasm is a framework, I would answer "as the user has decided to implement it" :)
To be honest, the picture gives nearly no clue. Is it code flattening?
English
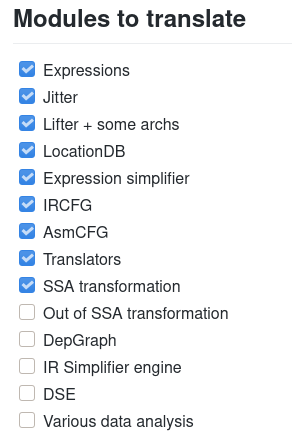
@BincatLady @moyix Yes, the core algorithms are re-coded in Rust to improve speed (Jitter / Lifter / code analysis / ... ) and to clean APIs a bit :)
But bindings allow python scripting currently!
English
@crackin10554874 Hi @crackin10554874, can you be a bit more precise for example on the Miasm gitter ?
gitter.im/cea-sec/miasm
English
Miasm retweetledi

Giving the workshop on code deobfuscation was great fun. Thanks for your active participation! #HITB2021AMS
Check out code, slides and samples here: github.com/mrphrazer/hitb…
English
Congratulation, you both succeeded in:
- resolving the challenge
- writing a great tutorial on how to add a custom architecture in Miasm & exploit the IR!
Suraj Malhotra@MrT4ntr4
Writeup for FCSC CTF 2021 - 'VMV' "Defeating Nested Virtualization with @MiasmRe" mrt4ntr4.github.io/FCSC21-CTF-VMV/ I explain how to write a custom architecture in Miasm and then use some pattern detection logic to solve the challenge. This took most of my time, Hope you guys like it!
English
Miasm retweetledi

If you want to learn more about control-flow graph construction, analysis and loop detection, check out my slide deck. I also wrote a blog post on how these concepts can be easily explored with @MiasmRe.
synthesis.to/2021/03/15/con…
English
Miasm retweetledi

A good example of automatic code deobfuscation based on pattern matching is stadeo by @ESET. They use @MiasmRe to automatically remove control flow flattening for the stantinko malware family.
github.com/eset/stadeo
English
@mr_phrazer @r2gui Great workshop Tim!
Hopefully, IR translation/symbolic execution/z3 translation will be nearly instantaneous in the @rust version of miasm ;)
English
Miasm retweetledi

Friday, 19:00 GMT+2 at #r2con2020:
In a live coding, I will use @r2gui and @MiasmRe to automatically identify and remove opaque predicates in an APT malware sample.
Check it out: rada.re/con/2020/youtu…
English
Miasm retweetledi

Emulating the NotPetya bootloader with @MiasmRe, an article by @la_F0uin3 and myself, translated from an article originally published in @MISCRedac :
aguinet.github.io/blog/2020/08/2…
Code available here: github.com/aguinet/miasm-…

English
@0xrepnz @_sudhackar For a real case symbolic execution example, here is (an old) one: miasm.re/blog/2016/09/0…
English

@_sudhackar @MiasmRe Symbolic execution is very interesting, I read "practical binary analysis" and Triton is interesting as well. The question is: Is it useful outside of CTFs and labs.. I'm not an expert on this topic but I only see it in labs and CTFs 😕
English

Finally got some time to try @MiasmRe to solve a crackme. I wrote a blog on how to use its Dynamic Symbolic Execution engine to automatically find and solve constraints since there are not many blogs on it
sudhackar.github.io/blog/learning-…
English