
if you don't have these in your configs you're ngmi
Philip Jennings
2.9K posts


@MikhailJennings
Privacy, cryptography and multi level cloud based cyber security (jk).

if you don't have these in your configs you're ngmi

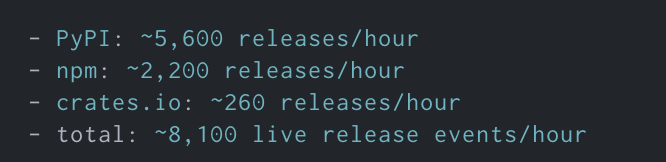
Why literally no one of the “scanning your dependencies” company found this in ~realtime and we had someone manually finding this because crashed the machine ? Something is wrong. Everyone is good writing after the fact.


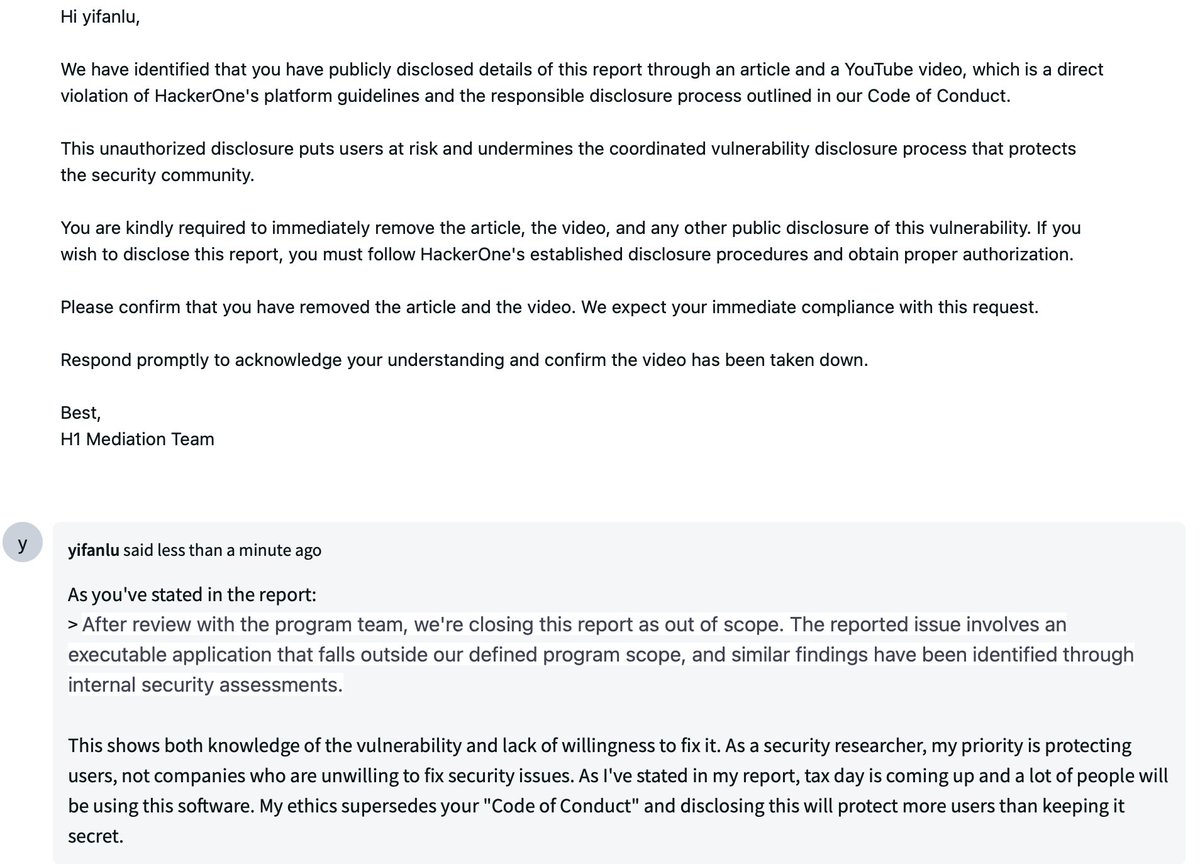



Thread - My own opinion & this is to the Bug Hunters, What @Hacker0x01 is doing re AI, is essentially stealing “our work” “our research” for their own profitability. They are for sure breaking client agreements, wherein a clients data / vulns belong to the client. Not H1!!



Frontend libraries I refuse to code without in 2025: 🔶 zod – validation 🔶 react-hook-form – forms 🔶 tRPC + react-query – data sync 🔶 shadcn – UI 🔶 motion – animations 🔶 date-fns – date utils 🔶 zustand – state management 🔶 nuqs – search params 🔶 recharts – charts 🔶 ai – AI toolkit 🔶 react-table – tables (still underrated) Your turn… Which libraries are MUST-HAVE in your stack? Drop your top 3 below.



If you have 2+ years exp in Java. Don't skip these 6 multithreading problems 👇 1. Producer-Consumer : Use BlockingQueue or wait/notify. 2. Print 1–100 (2 Threads) : Alternate using shared counter + lock 3. Print “ABCABC...” : Sync 3 threads with Lock or notifyAll. 4. Custom Thread Pool : Build using worker threads + queue. 5. Deadlock Scenario : Simulate & prevent via lock ordering. 6. Rate Limiter : Implement Token/Leaky Bucket logic.
