Mo retweetledi
Mo
6.7K posts


Mo
@Mo_RELS
Head of Brand Development // Curator @Ledger | My views are my own. Banner by @agoriamusic
Web3 Katılım Kasım 2018
2.4K Takip Edilen6.8K Takipçiler
Mo retweetledi
Mo retweetledi
Mo retweetledi

You just patched last month’s Nginx vulnerability that was actively exploited in the wild?
It’s already time for a fresh 0-day RCE.
The whole world is basically “pwned-by-default”, patching vulnerabilities before they’re exploited feels like a Sisyphean task... 🫠
Nebula Security@nebusecurity
Introducing nginx-poolslip, a fresh RCE for the the latest nginx release 1.31.0. nginx-rift has been patched, but our security agent Vega has found a new 0 day. We will release the full technical writeup with ASLR bypass 30 days after the patch on nebusec.ai.
English
Mo retweetledi
Mo retweetledi
Mo retweetledi

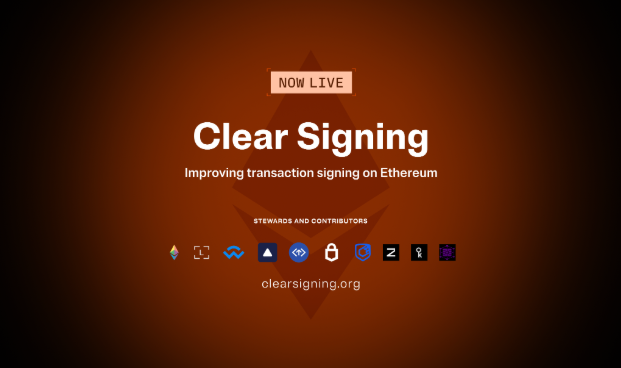
Clear Signing is going universal.
Since tackling blind signing with ERC-7730 in 2025, the mission has expanded. We’ve passed the governance torch to the Ethereum Foundation, adding cross-chain support, and taking Clear Signing from a @ledger feature into a shared industry standard. 🧵👇
English
Mo retweetledi

Mo retweetledi
Mo retweetledi
Mo retweetledi

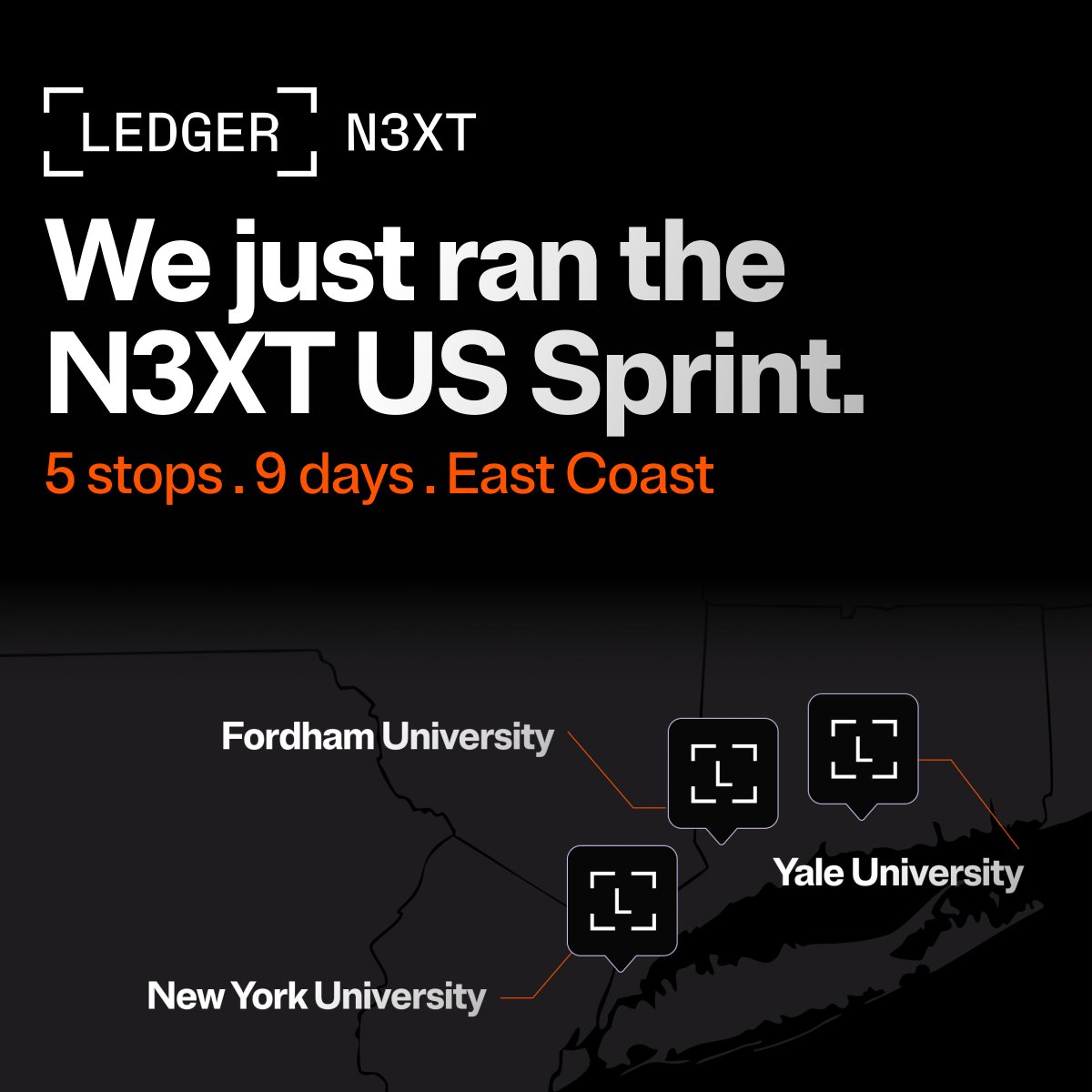
Last week @Ledger N3XT — our education program across college campuses — went to Cambridge. Honestly one of the most inspiring parts was just spending time with students who are thinking this deeply and rigorously about identity, ownership, AI, privacy, and the infrastructure being built underneath all of it.
800 years of academic history, two days of conversations about digital identity, consent, and trust.
We started with a fireside chat and Q&A. The students came prepared.
One Masters student asked whether Ledger is evolving from securing assets into infrastructure for human identity — and whether that future protects choice or concentrates control. Not a casual question.
A CS student pushed on quantum risk, identity, and why hardware matters at all in an increasingly AI-native world. His point was essentially: if intelligence becomes abundant and synthetic agents become indistinguishable from humans online, software alone stops being enough. At some point you need a physical root of trust tied to consent, identity, and verification in the real world.
Then he moved to privacy: send someone £2 for coffee on-chain and they can potentially see everything you own.
Those questions earned him a Ledger device. Most of the room got close.
Dinner at The Cambridge Union turned into conversations about decentralised infrastructure for interplanetary settlement, synthetic identity verification, and agentic systems. Less “future of tech” panel talk, more people actively trying to work through the implications.
The next day we toured Trinity’s Great Hall, the Wren Library, Newton’s apple tree. What stayed with me wasn’t the history so much as the continuity of the questions. How people establish truth. Authority. Consent. Ownership.
We met with professors and students and started laying groundwork for deeper collaboration. Cambridge has a habit of stress testing ideas until they either collapse or sharpen. That’s useful.
We’ll be back.
ledger.com/blog-ledger-n3…

English
Mo retweetledi

This morning, THORChain was drained of roughly $10.8m
Node operators have freezed the network for nearly 13 hours. The full analysis isn't out yet, but according to @jpthor, this could be a MPC exploit.
ECDSA and TSS is hard. THORChain's vaults rely on TSS, a flavor of MPC where a quorum of nodes jointly produces a signature without ever reconstructing the private key. Clean for Schnorr or EdDSA; painful for ECDSA, which Bitcoin and Ethereum require. That's why we saw plenty of protocol attempts (Lindell17, GG18, GG20, CMP, CGGMP21, DKLS, KU23...), each patching flaws in the previous one.
GG20 has a track record. THORChain's TSS uses GG20, on a fork of Binance's tss-lib. GG20 has shipped two well-publicized critical bugs: CVE-2023-33241 and TSSHOCK. CGGMP21, now cggmp24, are the latest protocols, but GG20 is still widely deployed.
I often hear a misconception when I hear about MPC setup: "The key is split across many nodes, so any single co-signer doesn't really matter".
In every published GG18/GG20 attack, one malicious or compromised co-signer is enough to extract everyone else's shard and reconstruct the full key.
AI changes the threat model. Compromising a full software node, complex Go stack, exposed P2P, custom signing daemons, a churn protocol that admits new participants on a schedule, has always been difficult and acted as a barrier. With LLM-driven vulnerability discovery and exploit synthesis, the bar to compromise one of N validators is dropping fast.
Here, it's a plausible TSSHOCK-style playbook:
- compromise one operator
- wait for it to churn into an active Asgard vault
- send malformed proofs during keygen or signing
- reconstruct the key offline
- sweep in a single transaction
It's unclear yet if the attacker used a known-unpatched GG20 weakness, or a fresh cryptographic flaw.
But, in all cases, MPC and TSS are not a substitute for hardening every co-signer. They sit on top of co-signers that must each be treated as critical infrastructure, hardware-isolated enclaves, minimally exposed, continuously audited, and running protocol with security proofs.
While the investigation progresses, be careful in your interactions onchain. These TSS setup are used in various protocols.
English
Mo retweetledi
Mo retweetledi
Mo retweetledi
Three years ago, we started the Clear Signing initiative as an open-source standard.
Today, Clear Signing is becoming the industry default for transaction security.
The Clear Signing Working Group brings together contributors from across the industry, all working towards a common goal of replacing blind signing with human-readable signing experiences, with the @ethereumfndn acting as a neutral steward.

English
Mo retweetledi

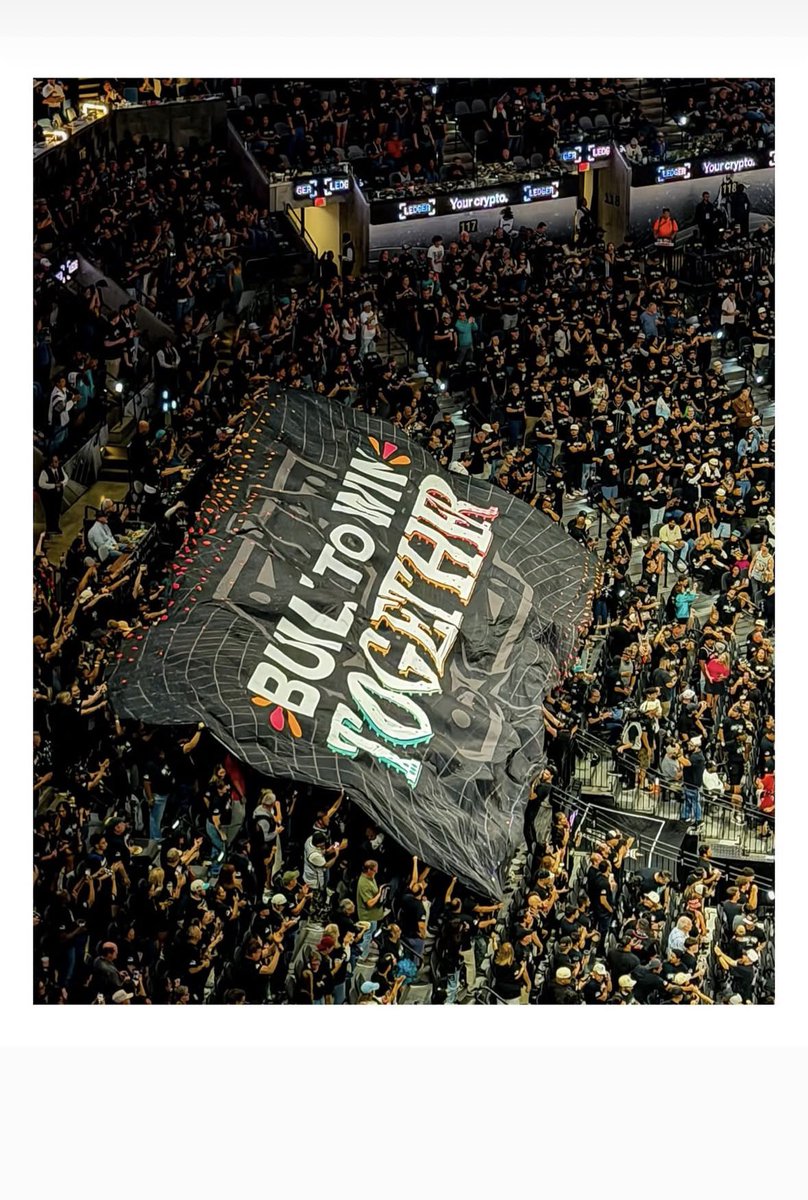
Wanted to take a moment to say thank you @Ledger . In our first year, they’ve stepped in and made things possible that otherwise wouldn’t be. We appreciate their genuine desire to help us build the atmosphere and keep Frost Bank Center Locked In.
English
Mo retweetledi

AI will be many things. But never human.
The danger is not that machines will wake up. It is that we will forget the difference, then give them the legal and emotional machinery of personhood.
I wrote about this for @RickRubin’s @tetranow 👇 :
(image courtesy of @infiniteyay)

English
Mo retweetledi

Congrats to the @Spurs 👏
Incredible team. Incredible vision. This is what happens when talent meets discipline.
Proud to see a bit of 🇫🇷 shining on that stage.
On to the next round.
x.com/nba/status/204…
NBA@NBA
The Spurs advance to the Western Conference Semifinals for the first time since 2017! NBA Playoffs presented by @Google
English