nicolas vamous retweetledi

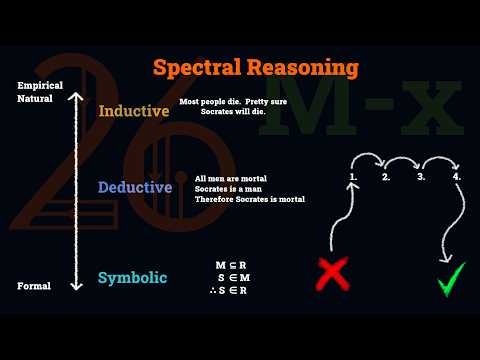
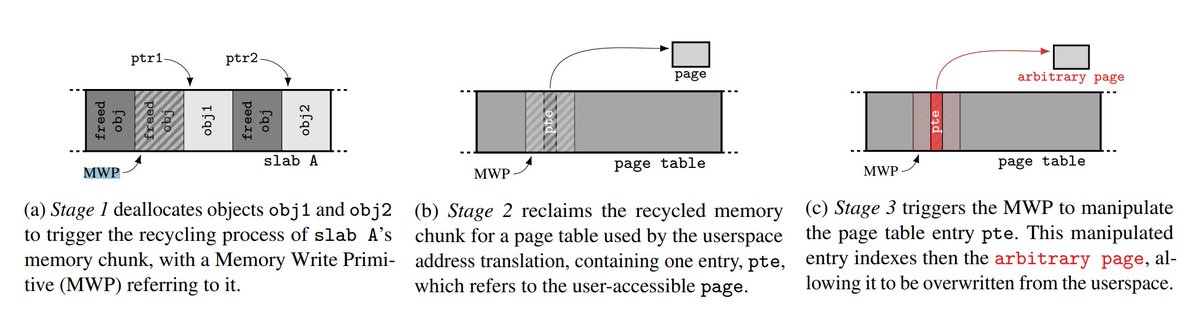
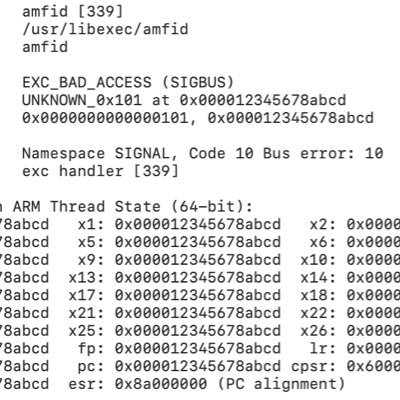
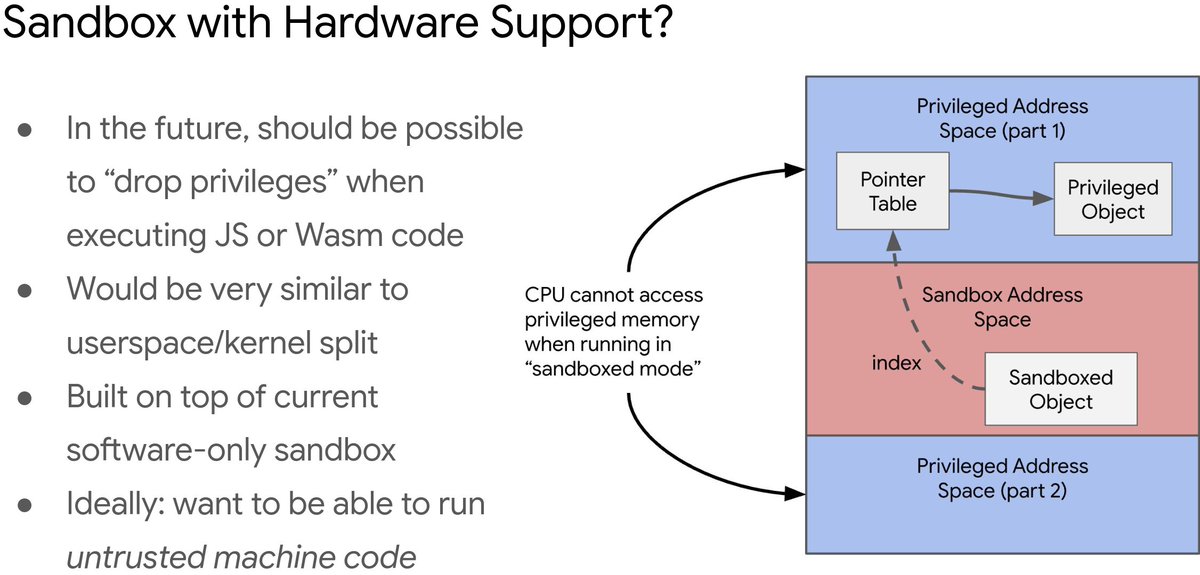
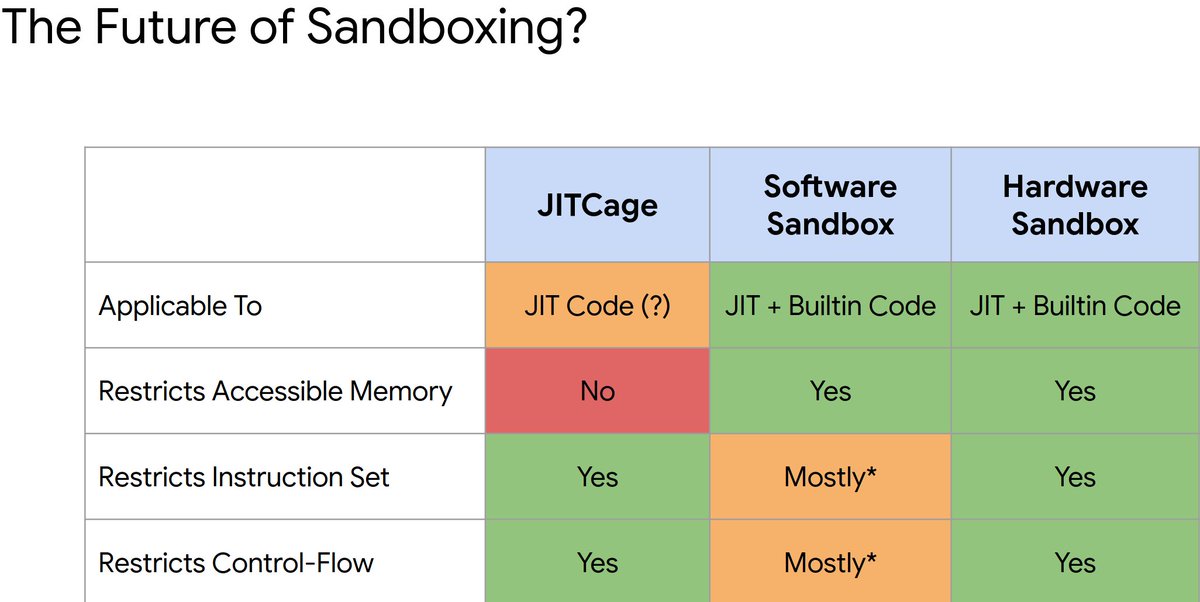
Slides from Samuel Groß talk(@5aelo) about v8sbx hw-support
powerofcommunity.net/2025/slide/s-9…
developer.arm.com/community/arm-…


xvonfers@xvonfers
issues.chromium.org/issues/3503248… docs.google.com/document/d/1l3… docs.google.com/document/d/12M… issues.chromium.org/issues/4281795… issues.chromium.org/issues/4265147… issues.chromium.org/issues/4279469… issues.chromium.org/issues/4293416… issues.chromium.org/issues/4291428… issues.chromium.org/issues/4291737… chromium-review.googlesource.com/c/v8/v8/+/6874…
Deutsch