Sabitlenmiş Tweet
Narsing
16.4K posts


Narsing
@Narsing_01
Software Engineer 🌪️ 💡 Digital diary | d 🌻🌈
Pune, India Katılım Mayıs 2019
3.8K Takip Edilen450 Takipçiler
Narsing retweetledi

Some arrangements of words can replenish your energy & your courage. This is one.
cinesthetic.@TheCinesthetic
“Pressure is a Privilege. And if you’re feeling any pressure or weight of expectation, you are breathing rare air, that very few of us get to live inside”. - Tom Hiddleston
English
Narsing retweetledi
Narsing retweetledi
We mapped the Kubernetes control plane.
If you want to understand what happens after `kubectl apply`, this series is for you.
5 articles covering the API server, etcd, the controller manager, and the scheduler.
learnkube.com/kubernetes-con…

English
Narsing retweetledi
Narsing retweetledi

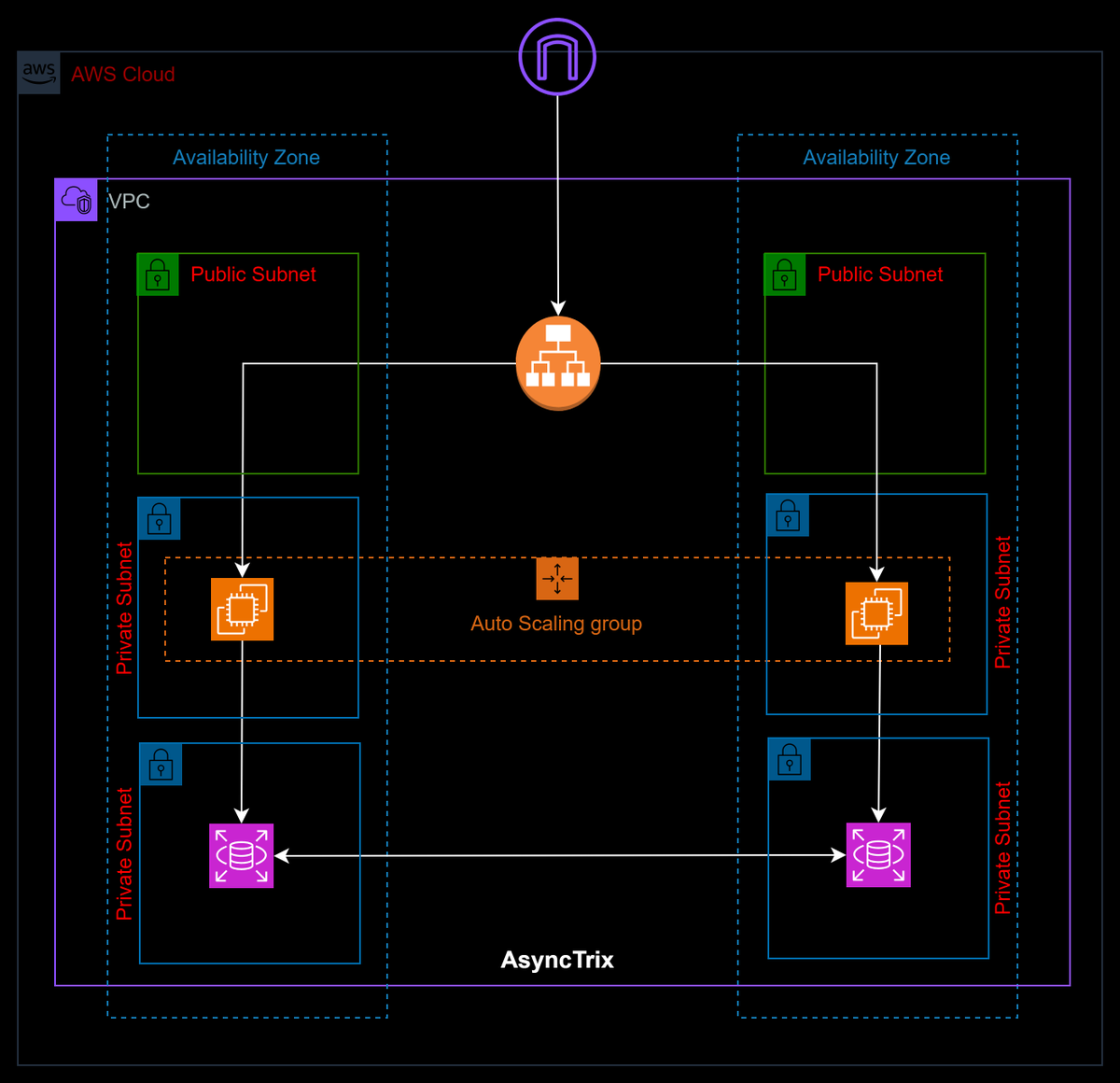
🏗️ AWS 3-Tier Architecture - Simplified 🔥
🌐 Access Tier
• ALB → Single entry point ⚖️
• Distributes traffic across AZs 🌍
• Handles HTTPS (SSL termination) 🔐
• Path / host-based routing 🧩
• No business logic 🚫
--------------------------------
⚙️ Application Tier
• EC2 → Private subnets 🧠
• No public IP → secure 🔒
• Auto Scaling Group ⚡
• Scale up/down automatically 📈
• Runs APIs & backend logic 💻
• Uses NAT for outbound 🌐
👉 Rule
• Keep it stateless ⚠️
--------------------------------
🗄️ Data Tier
• RDS / DynamoDB 💾
• Private subnets only 🔐
• Multi-AZ replication 🔁
• Backup & recovery 🛟
• No internet access 🚫
--------------------------------
🧠 Core Idea
❌ Not about public vs private
✅ About responsibility separation
• ALB → Traffic ⚖️
• EC2 → Logic ⚙️
• DB → Data 🗄️
--------------------------------
🔥 Production Truths
• ALB = stateless ⚡
• App must be stateless ⚠️
• DB = bottleneck 📊
• Security Groups = firewall 🔐
• Private subnet ≠ no internet 🌐
--------------------------------
🎯 Flow
User → ALB 🌐
ALB → EC2 ⚙️
EC2 → DB 🗄️
--------------------------------
🚨 Golden Rule
Never expose EC2 or DB directly ❌
--------------------------------
💡 Big Picture
→ Secure 🔒
→ Scalable ⚡
→ Production-ready 🛠️
English
Narsing retweetledi

NVIDIA is literally handing out certifications in Agentic AI, Physical AI, and OpenUSD. And most people don't even know they exist.
Here's your no-fluff guide to getting NVIDIA certified in 2026:
- Two tiers. Pick your level.
Associate (NCA): 60 min, ~50-60 questions,
Professional (NCP): 90-120 min, ~60-75 questions
No prerequisites. You can jump straight to Professional if you've got the experience.
Which track fits you?
- GenAI/LLMs: NCA-GENL → NCP-GENL
- AI Agents: NCP-AAI (live on Certiverse now)
- Data Science: NCA-ADS → NCP-ADS
- Infra/Ops: NCA-AIIO → NCP-AII
- 3D/Simulation: NCP-OUSD
- Physical AI: coming soon
How to prep:
- Download the Exam Blueprint PDF from nvidia.com/certification
- Take the mapped NVIDIA DLI courses (some free, some paid )
- Get hands on with GPU instances on AWS/Azure/GCP
- Practice under timed conditions. These are scenario based, not textbook trivia.
NVIDIA's April 30 global webinar is giving every attendee a 50% off exam discount code.
Register here: nvda.ws/41aiaEf
This is your chance to get NVIDIA certified that too at a huge discount just by attending a webinar.
#nvidia #certified #ai #code


English
Narsing retweetledi
Narsing retweetledi

If you are looking for an open source project to work on and enhance your CV. The Jenkins in Google Summer of Code 2026 is what you should be looking at!
Checkout the details below
jenkins.io/projects/gsoc/
English
Narsing retweetledi
Narsing retweetledi
Narsing retweetledi
Narsing retweetledi
Narsing retweetledi
Narsing retweetledi

How DNS works in 60 seconds:
What is DNS: Domain Name System
You type xyz.com in your browser. But the internet doesn't speak domain names. It speaks IP addresses.
So here's what happens behind the scenes:
1. Your browser asks: "Where is xyz.com?"
2. Your ISP's DNS resolver checks its cache. If it's been asked before, it answers instantly. If not, it starts asking around.
3. It asks the Root Name Server → "I don't know, but try the .com TLD server."
4. It asks the .com TLD server → "I don't know, but try the Authoritative server for xyz.com.
5. The Authoritative server answers: "xyz.com = 203.0.113.47"
6. The resolver caches the answer and sends it back to your browser.
7. Your browser connects to 203.0.113.47 and the website loads.
All of this happens in milliseconds. Every single time you visit a website.
And when DNS breaks? Nothing loads. No website. No app. Nothing. Even if the server is perfectly fine.
That's why "it's always DNS" is the most repeated sentence in IT.
Bookmark this 🔖

English
Narsing retweetledi

idk about arsenal but this motivated me for life
Sky Sports News@SkySportsNews
"Pressure is a privilege" Golden Globe winning actor Tom Hiddleston gives his thoughts on the huge clash between Manchester City and Arsenal 🎬
English
Narsing retweetledi

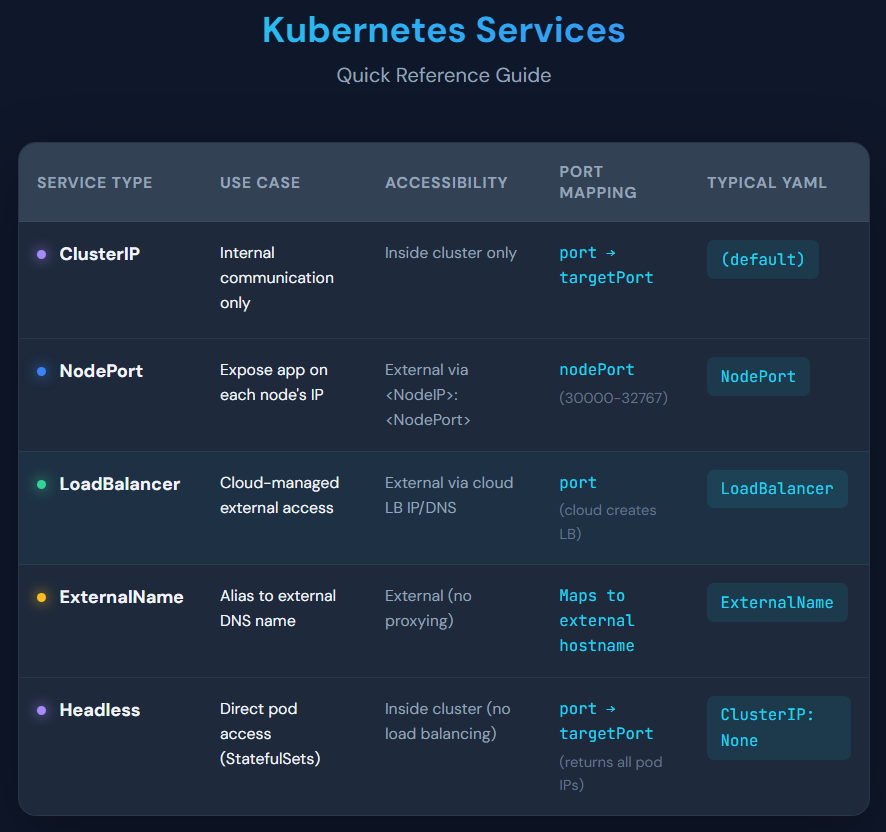
What is a Kubernetes Service?
A Service is like a stable “front door” for your apps running in Pods.
It gives you one reliable address (IP or DNS) so users or other apps can reach your Pods even if Pods are created, deleted, or moved.
Without services, accessing pods would be messy because their IPs keep changing.
Services:
• Use labels to find the right Pods
• Route traffic automatically
• Enable service discovery via DNS
(e.g. my-service.my-namespace.svc.cluster.local)
English
Narsing retweetledi

Kubernetes Secrets are not secrets. They never were.
You put your database password in a Kubernetes Secret. You felt like you did the right thing. You didn't.
Anyone with kubectl access runs one command and reads your password in plaintext. Base64 is a format, not encryption. You just stored your secret in a fancy text wrapper and called it done.
That secret also sits in etcd unencrypted by default. So you configure EncryptionConfiguration on your API server. Now Kubernetes encrypts secrets with AES before writing them to etcd.
But you still create secrets manually with kubectl. Someone creates one, leaves the company, and that secret runs in production for two years. Nobody knows what it does. Nobody ever rotated it.
So you bring in Vault.
> Vault gives you dynamic secrets, lease TTLs, automatic rotation, and a full audit log of every access.
> Your database password now expires every 24 hours and Vault rotates it automatically.
> You stop worrying about leaked credentials because they expire before anyone can do real damage.
But now every team needs to talk to Vault and every team does it differently. One writes a custom init container. Another one hardcodes the Vault token directly in the pod spec because the sprint deadline was the next morning.
So you use Vault Agent Injector.
> You add two annotations to your pod and a mutating webhook injects a Vault sidecar automatically.
> The sidecar authenticates to Vault using the pod's own Kubernetes service account and writes secrets as files inside the container. Your app reads files.
> You touch zero application code.
But your legacy app reads environment variables, not files.
So you switch to Secrets Store CSI Driver.
> The CSI driver mounts secrets directly as a volume into your pod at startup from Vault, AWS Secrets Manager, or Azure Key Vault.
> When the secret rotates in the external store the pod picks up the new value automatically without a restart.
But now you have 40 services and 40 SecretProviderClass manifests to maintain.
Someone rotates a secret and changes its path in Vault but forgets to update the manifest. The pod crashes at 2am. The secret exists in Vault. The path in your manifest points nowhere.
So you bring in External Secrets Operator.
> You write one ExternalSecret resource and ESO pulls the secret from Vault or AWS Secrets Manager and creates a native Kubernetes Secret on its own.
> You set a refreshInterval and ESO keeps everything in sync automatically.
> No manual kubectl. No drift. No 2am surprises because someone forgot to update a manifest.
Not everyone needs a perfect solution. Just understand which problem each tool actually solves, and you will know exactly where to go next.
English
Narsing retweetledi

Crossref is hiring a DevOps Engineer to join their Infrastructure Services team. This is a hands-on role focused on reliability, observability, and evolving large-scale systems.
Remote and global, with overlap in European time zones.
Apply by May 5, 2026.
lnkd.in/e7xg_qGc
English