

Nascent Security
36 posts


@NascentSecurity
Building for a more secure crypto ecosystem @nascentxyz



The biggest bug bounty in history is now live. @Uniswap just raised the standard of building in public 🪐 With $15.5M on the line, it's an unprecedented testament to the rigorous security of v4. Think you can find a critical bug? Give it a shot. 🔗 Bounty link below
Today, we are announcing our $4.5m pre-seed, led by @FigmentCapital and @nascentxyz with support from @robotventures, @hash3xyz, @BanklessVC, @breed_vc, and @publicworksfm. We will use these funds to develop The Credible Layer, a hack prevention protocol. Here's the story (there are some twists and turns): On August 1st, 2022, Nomad lost $190 million in one of crypto’s largest hacks—a turning point for @odysseas_eth, a protocol engineer at Nomad. Conversations with users, founders, and engineers revealed a sobering truth: Many can’t sleep for fear of being hacked; some have even left the space entirely. We’re not just losing the best builders and teams to hacks—we’re losing them to the fear of hacks. Read the full announcement here: phylax.systems/blog/phylax-sy… It should be obvious at this point, that one of the primary hurdles to adoption en masse is the BILLIONS of dollars of hacks that occur every year. Current solutions, like fuzzing, next block mitigation, and frontrunning protection, are valuable but by no means a silver bullet. They patch the problem—they don’t solve it. We need security that can’t be bypassed and is verifiable. This is what Phylax Systems is on a war path to deliver. We’re building the Credible Layer, a proactive security layer that allows dApps to define hack-prevention rules and communicate them to the block builder, specifying states they want to prevent. The assertion enforcer checks each transaction against these rules, stopping hacks before they happen. It is non-invasive and is functionally a coordination mechanism between dApps and the base layer, keeping dApps sovereign and secure. The Credible Layer is also fully transparent—anyone can view a dApp’s security rules and verify their enforcement. dApps pay fees for this validation, ensuring their assets remain safeguarded. Some may question the reliance on trusted entities to enforce these rules. However, this model builds on the trust assumptions that already underpin much of blockchain infrastructure; for example, a small number of entities currently support over 90% of Ethereum’s block production. We’re not advocating for increased centralization but rather creating new security mechanisms on top of existing, industry-tested trust structures. Regulators have scrutinized our industry due to high-profile hacks, and while their intentions may not always be entirely impartial and fair, this particular concern is valid. The recent $53MM Radiant hack underscores just how far we still have to go. It’s up to us to prove that security isn’t an afterthought but a core component of every crypto project. As an industry, we must prioritize security in our designs, our products, and how we position ourselves to users—it can no longer be secondary. As @nic_carter said: “We’re long overdue for moving DeFi hack mitigation from reactive to proactive, and Phylax is leading the charge.” We don't want to scar the mainstream as soon as we onboard them. We need security that makes them feel safe. We intend to make this a reality with the Credible Layer. To get the full picture of the Credible Layer, read the Whitepaper (we just released it): github.com/phylaxsystems/… And if you are interested in joining the waitlist for the Credible Layer please reach out here: t.co/DxKM64rvzo



The CertiK rabbithole seems to go deeper and deeper. OpenBounty, a bug bounty platform "incubated" by Shentu (the new name of Certik Chain), appears to be attempting to front run bug bounty reports. This is a direct violation of many large protocol's bug bounty terms (including one's that OpenBounty lists). The more suspicious thing, is that their website makes requests to a domain with CertiK in the name when you report a bounty... Does it seem safe to report a critical vulnerability to CertiK before notifying the protocol themselves...? Especially considering CertiK exploited Kraken last week. If you find a bug, report it to the protocol directly. Not some shady website associated with CertiK. Who is to know if they're going to: A) steal your bounty B) exploit the protocol Every day that passes I truly believe more and more that CertiK is a front for a North Korean black hat organization.
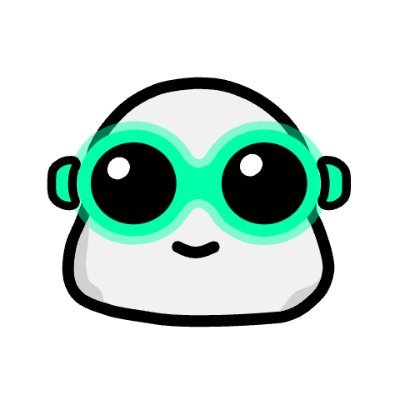

A couple important metrics pop in my head: 1. bounty $s / bountied line of code 2. bountied lines of code / protocol lines of code 3. bounty $s / TVL @BountyVision takes the first step to helping measure the quality of bug bounties via Bounty $s / TVL


No one outside of North Korea is happy with the current state of DeFi security Fortunately, there is something we can do about it: SPEND MORE ON SECURITY! Strap in for a discussion of security budgets, bounty flywheels, and a new tool from @NascentSecurity...

We are live! bounty.vision



