NETSCOUT
17.1K posts

NETSCOUT
@NETSCOUT
We provide the #data that drives #observability, fortifies #cybersecurity, and keeps the world's most essential organizations resilient against disruptions.
Westford, MA Katılım Kasım 2008
5K Takip Edilen13.8K Takipçiler

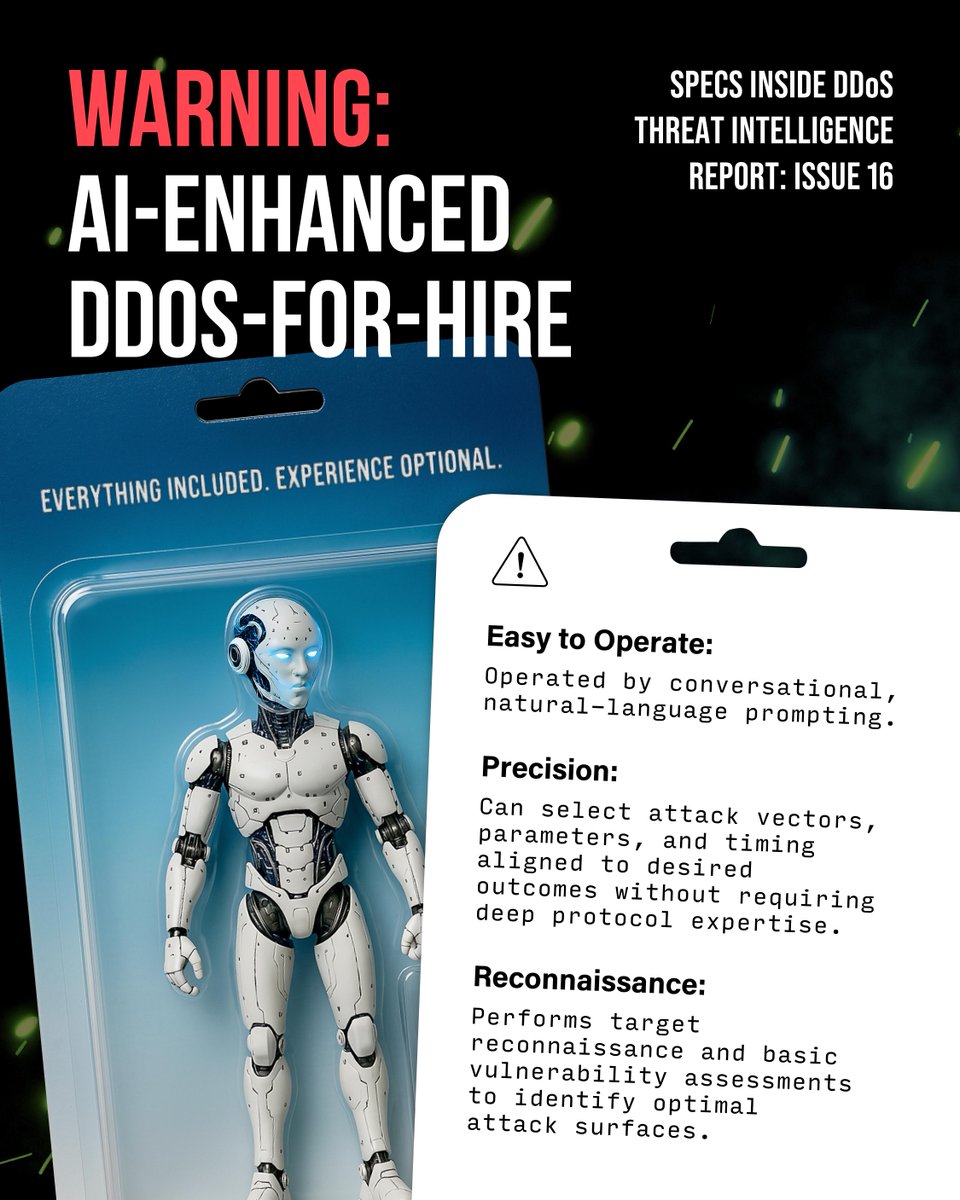
⚠️ The barrier between intent and execution is disappearing.
New DDoS platforms now embed conversational AI allowing attackers to describe an objective and let the system handle the rest.
From our vantage point across global network traffic, this evolution is already changing how attacks are launched and scaled. Are your defenses ready for what comes next? netscout.link/6011BBG3I3
English

Security leaders are rethinking what progress in cybersecurity really looks like. Speed still matters, but resilience is becoming the bigger priority.
That shift will be explored at @rapid7's 2026 Global Cybersecurity Summit, where our CISO, Deb Briggs, will join peers to discuss how teams are reducing attacker advantage and strengthening the digital experiences organizations depend on every day.
Learn more. Save your spot. netscout.link/6011BB1NP9
English

Cyberattacks aren’t changing by type. They’re changing by access and speed.
NETSCOUT’s Darren Anstee says conversational AI lowers barriers, making attacks easier to launch and scale. Simplification and automation are the real threat.defenders have to rethink “now what.” netscout.link/6013BB1RyU
English

When AI is fed high-fidelity operational data:
• Root cause analysis improves
• Cross-domain correlation becomes feasible
• Signal-to-noise ratio increases
Result: more reliable models and faster operational decisions.
More here: netscout.link/6016BBEAgK
English

It is never just five seconds.
It is lost transactions. Frustrated users. Escalations.
Fixing the problem starts with understanding it.
We help teams get there faster. netscout.link/6010BBEQFK
English

More sophisticated. More destructive. Harder to stop.
Our Threat Intelligence Report underscores the scale of today’s threat landscape, while @IDC research identifies the 9 critical challenges organizations face in DDoS mitigation. https://secu netscout.link/6012BBBCNG netscout.link/6018BBBCN8
English

Summer travel stresses more than operations. It tests every digital touchpoint.
When apps slow, queues grow and passengers feel it instantly.
Peak demand does not have to mean peak risk. If this is on your radar, you are not alone. It is a challenge we help solve every day. netscout.link/6013BBBszT
English

This Telco Magazine piece highlights a shift happening across service providers 👇
• AI used to reduce time to isolate issues
• Automation that protects availability at scale
• Cleaner data that actually supports decisions
• Less customer impact when attacks hit
For telcos, resilience is now an operating model, not a toolset. netscout.link/6016B6hIgn

English

Shadow AI isn’t just a policy issue.
It’s creating real, persistent infrastructure that operates outside your architecture diagrams.
If you’re not looking at actual traffic and behavior, you’re probably missing it.
🔗 netscout.link/6017B6C5YJ
English

