The NonNFT Summit
300 posts


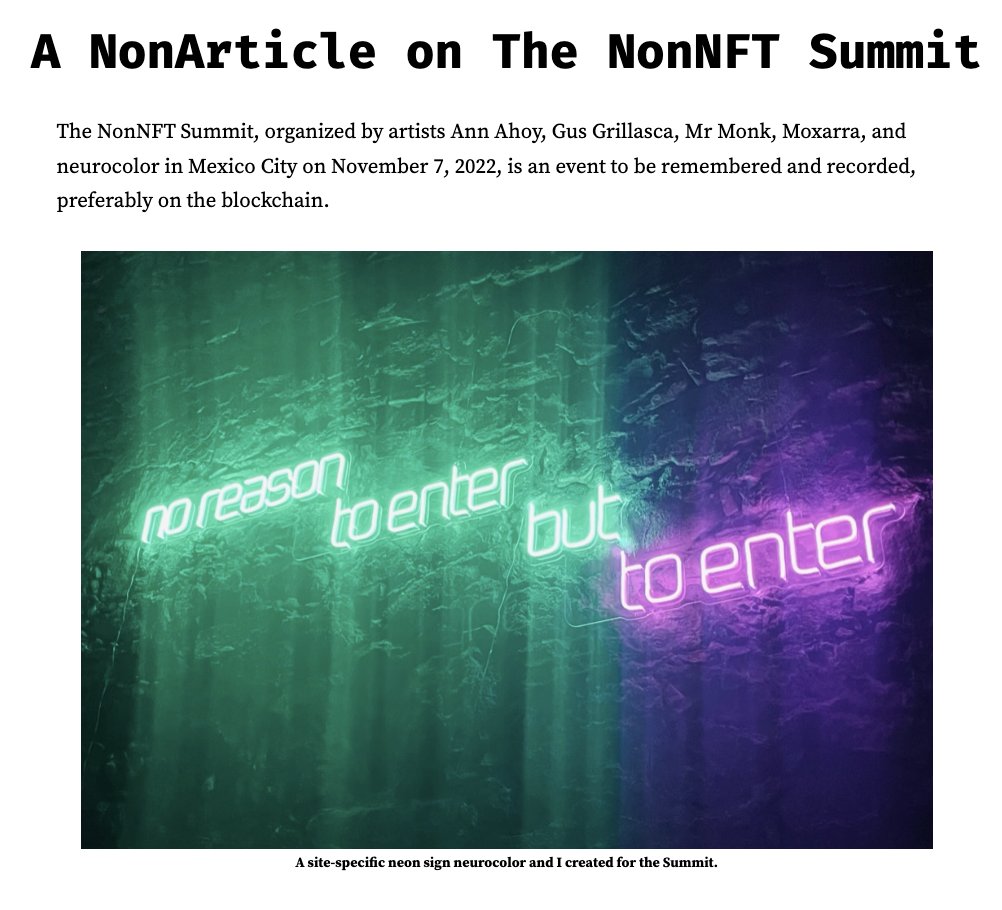
The NonNFT Summit
@NonNftSummit
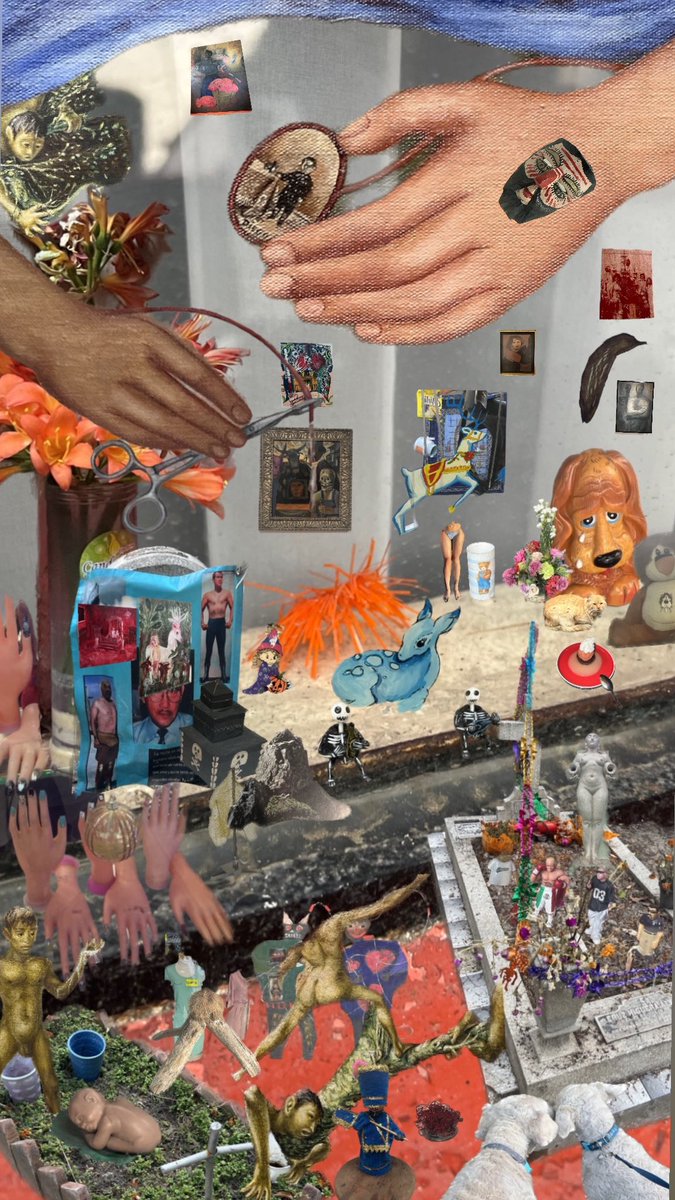
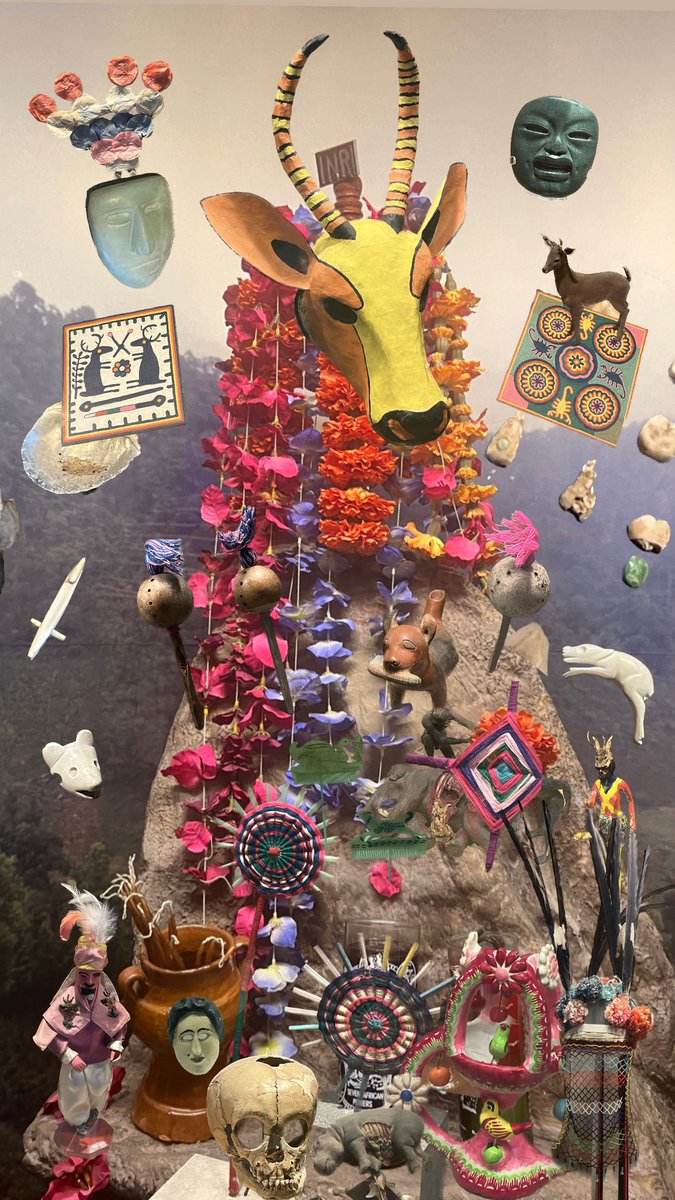
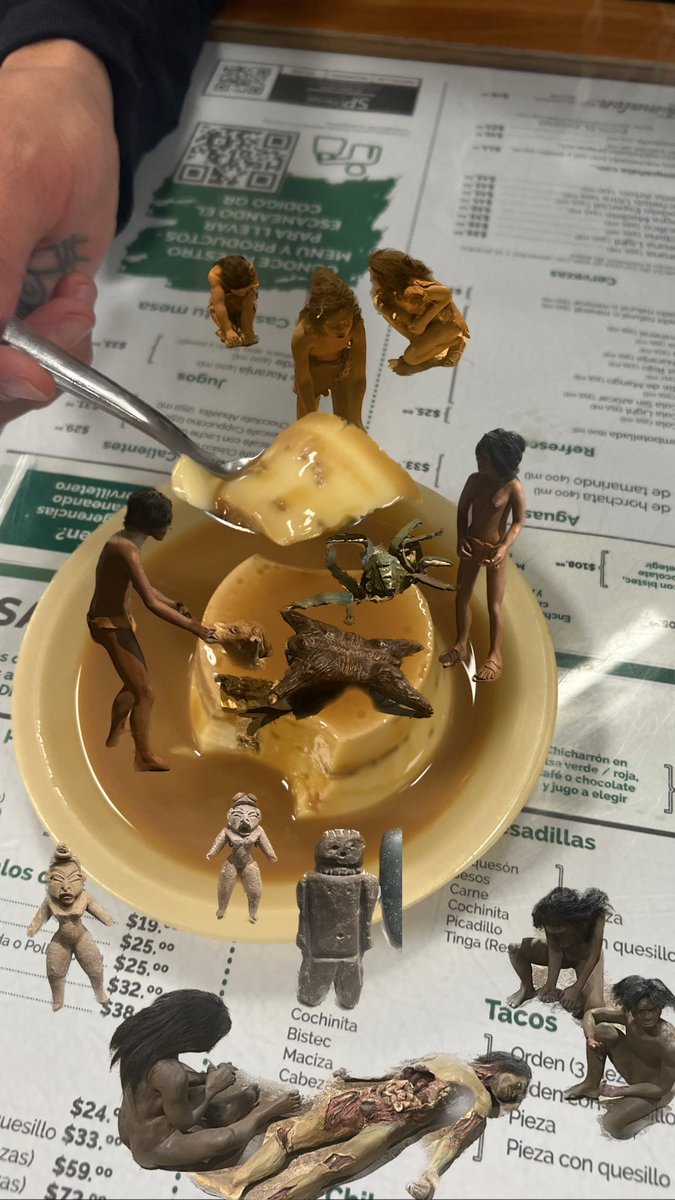
Cryptoart Event Nov. 7, 2022 @ Prim 32, Mexico City. Official commemorative token collection: https://t.co/1SwUO6fORK







IMPORTANT On November 20th, 2023 6pm PST, we became aware of a security vulnerability in a commonly used open-source library in the web3 industry. This impacts a variety of smart contracts across the web3 ecosystem, including some of thirdweb’s pre-built smart contracts. Based on our investigation so far, this vulnerability has not been exploited in any thirdweb smart contracts. However, smart contract owners must take mitigation steps on certain pre-built smart contracts that were created on thirdweb prior to November 22nd, 2023 at 7pm PT. The impacted pre-built contracts include but are not limited to DropERC20, ERC721, ERC1155 (all versions), and AirdropERC20. Please see a full list of impacted smart contracts and mitigation steps at this link → blog.thirdweb.com/security-vulne… Our immediate priority is to protect our customers impacted by this vulnerability. If you deployed one of these pre-built smart contracts using thirdweb’s dashboard or SDKs before November 22nd at 7pm PST, you need to perform some steps to mitigate the potential exploitation of the vulnerability. We and our security partners have been working at full capacity since being made aware of the vulnerability to build a tool to easily determine and perform the mitigation steps you need to take, which can be accessed here → mitigate.thirdweb.com In most cases, the mitigation steps will involve locking the contract, taking a snapshot and migrating to a new contract without the known vulnerability. The exact steps you need to take will depend on the nature of your smart contract, and you can determine these using the tool. You can also find a step-by-step guide on how to use the mitigation tool here → blog.thirdweb.com/security/contr… Please note: If your holders have tokens locked in any liquidity or staking pool, they should pull these tokens out before you begin these steps. Otherwise, you will not be able to distribute new tokens to these users. Additionally, you should request that your users revoke approvals on all thirdweb contracts using revoke.cash, which will protect your users if you choose not to mitigate the contract. Once we became aware of the vulnerability, we activated our security team and worked closely with our audit partners to investigate the issue. We successfully pushed a remediation for all of thirdweb’s impacted pre-built contracts created after November 22nd 7pm PST. Any thirdweb smart contract (as long as it is the latest version) deployed after November 22nd at 7 PM PST is therefore not impacted by this known vulnerability. All other thirdweb services, including our wallets, payments, and infrastructure services, are also unaffected and functioning as usual. We have also contacted the maintainers of the open-source library at the root of the vulnerability (which we are not specifying to mitigate the chance of exploitation) and contacted other teams we believe may be impacted by the same issue to share our findings and mitigation measures. Moving forward, we are increasing our investment in security measures. This includes doubling our bug bounty payouts from $25k to $50k per bounty, and implementing a more rigorous auditing process, with the goal of creating a robust environment for web3 developers. We understand that this will cause disruption, and we are treating the mitigation of the issue with the utmost seriousness. We will be offering a retroactive gas grant to cover fees for contract mitigations. Please fill in this form to be considered. → form.typeform.com/to/UOAk0W4C Please visit our blog for more information on this vulnerability → blog.thirdweb.com/security-vulne… To access our mitigation tool, please use the link here → mitigate.thirdweb.com. For ALL SUPPORT questions related to the vulnerability and mitigation steps, please EMAIL us directly at support@thirdweb.com to protect yourself and other users in the community from sharing vulnerable contracts. This is the only tweet in this thread. Anything below may be spam or phishing. Do not click on any links unless you have determined they are safe and from an official thirdweb.com domain.