
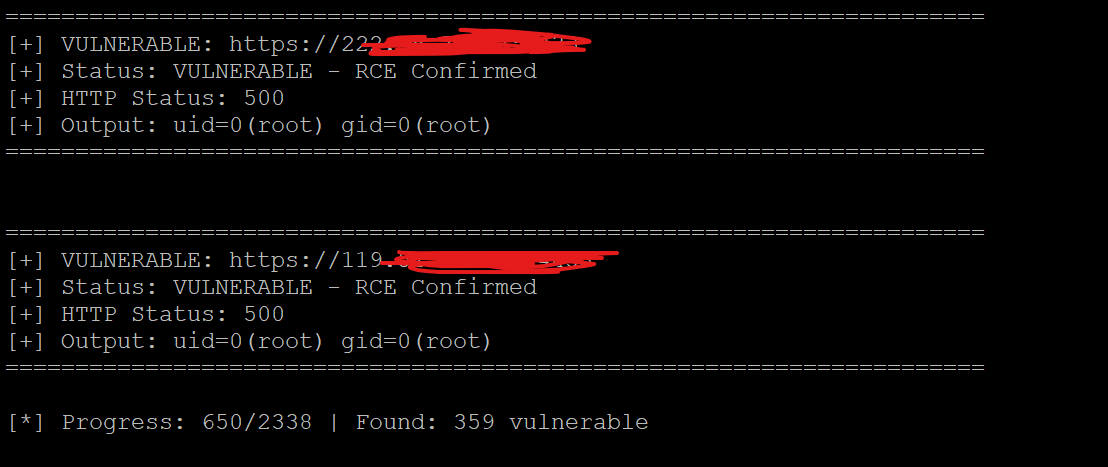
🎄🎁 Here is a 0day unauthenticated root RCE affecting over 70,000 devices on the internet. pwn.ai/blog/cve-2025-… For our first post, we show how pwnai autonomously found a root rce affecting XSpeeder, over 8 months ago. To our knowledge, this is the first agent-found, remotely exploitable 0day RCE published. Merry Christmas & Happy New Year 🎅💥










