Proximus Luxembourg CSIRT
977 posts


Proximus Luxembourg CSIRT
@PXS_LU_CSIRT
Proximus Luxembourg Cyber Security Incident Response Team








F5 Breach #ai-recommendations-54" target="_blank" rel="nofollow noopener">my.f5.com/manage/s/artic…


🚨 Critical zero-day tagged as CVE-2025-61882 (CVSS 9.8) affecting Oracle E-Business Suite I've created a vulnerability detection script here: github.com/rxerium/CVE-20… This vulnerability is remotely exploitable without authentication. Patches are available as per Oracle's Security Advisory: oracle.com/security-alert…












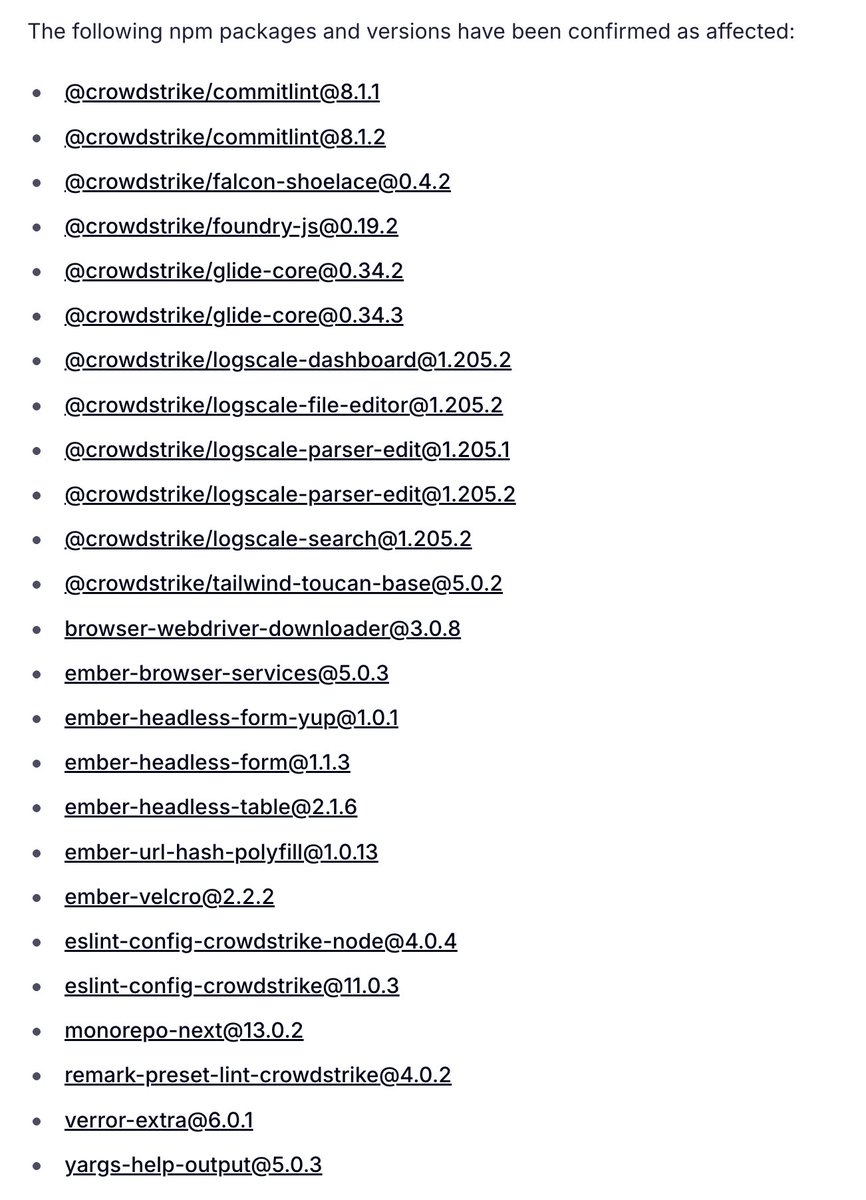
This is not over. 👇 🚨 A new wave of the npm supply chain attack just hit again. This time targeting CrowdStrike packages. Socket detected malware-laced updates that steal developer creds, spin up rogue GitHub Actions, and exfiltrate secrets. Developing story...