Sabitlenmiş Tweet
P.H.A.N.T.O.M F.O.R.T
9.8K posts


P.H.A.N.T.O.M F.O.R.T
@Phantom_Secure
Web3 Auditor @ AGV Protocol | Bridging smart contract & infrastructure security gaps | On-chain + cloud/API pen-testing
lagos nigeria Katılım Aralık 2014
2.5K Takip Edilen1.5K Takipçiler

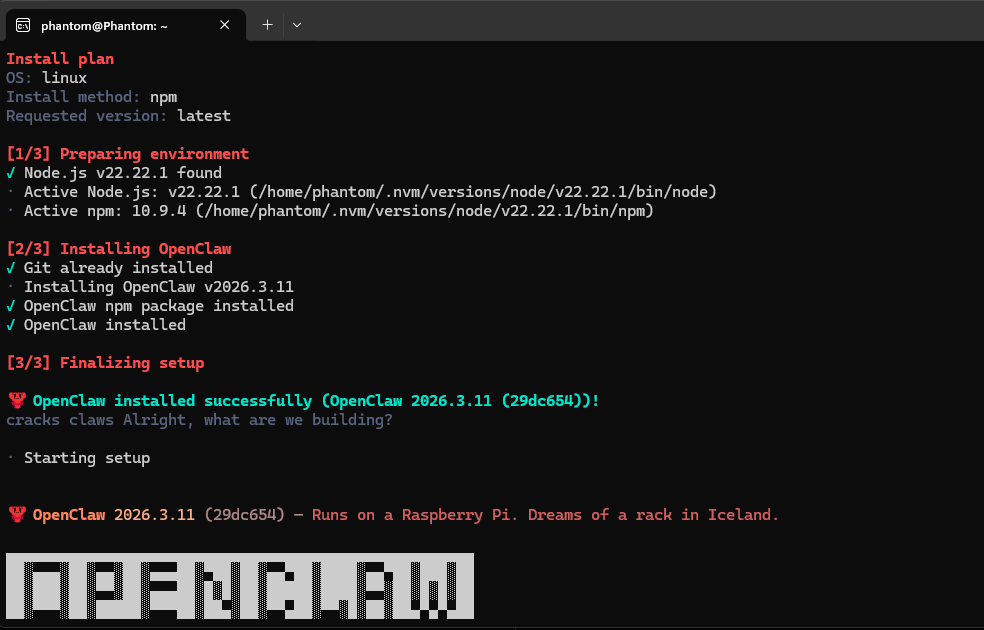
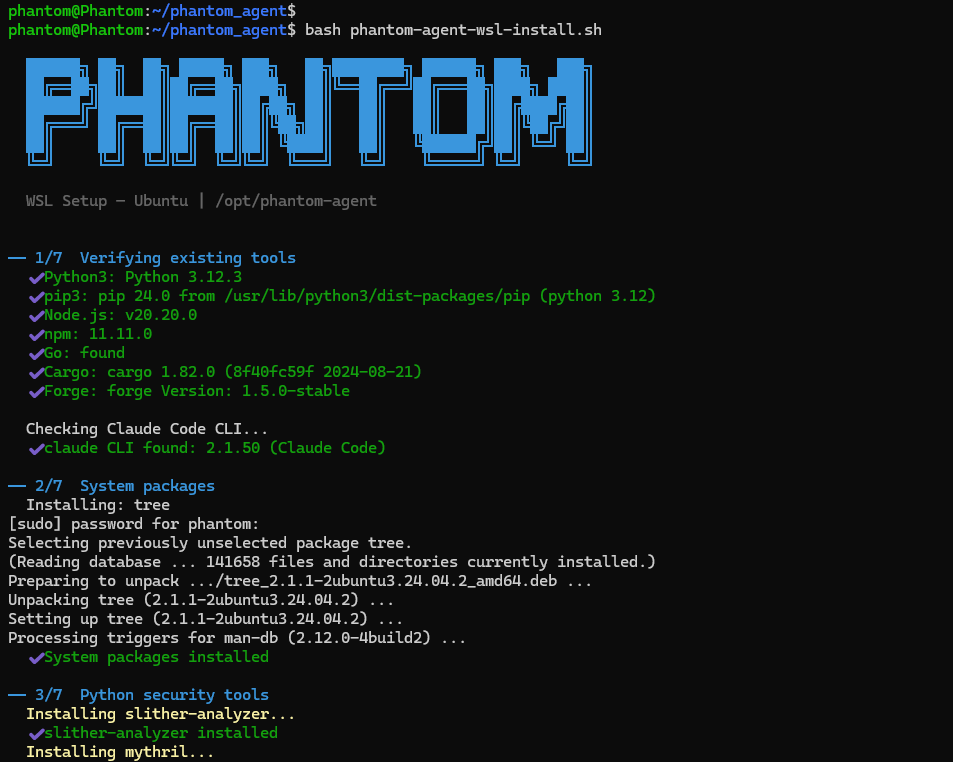
@rems_vynl The github link in the security auditor task, links to a non existent codebase.
Also, asking user to run a command that executes a script on their terminal as demo, is a red flag.
Kindly review these things if you are a real organisation.
English

@yehhmisi Those are outliers, and the conclusion is based on the average.
English

Funny because when you look at the history of computing….
The very first computer program was written by a woman, Ada Lovelace.
Grace Hopper created one of the first compilers, which made programming more human-readable.
Margaret Hamilton led the team that built the software that took humans to the moon.
Radia Perlman invented the technology that makes modern internet networks stable.
Katherine Johnson calculated flight paths that made space travel possible.
I could go on.
So reducing “girls” to color and aesthetics, and “boys” to specs is inaccurate.
Python Developer@Python_Dv
True 😂😜
English

@Fav_Truffle You only need to learn.
That is all the price there is to pay.
English
P.H.A.N.T.O.M F.O.R.T retweetledi

Don't Spend 4.44 million to find out what your company is weak at.
Waiting till your data is breached before taking security cautions is very risky
The average breach of information cost in the world stood at 4.44M in 2025 (IBM Cost of a Data Breach Report).
Reactive recovery consumes resources, undermines trust and attracts regulatory fines. Sometimes, the company is lost totally.
This can be prevented with Penetration testing, where vulnerabilities are identified and fixed in advance before they can be exploited. It is more cost-effective than fixing, it saves millions in lost business, legal fees, and downtime.
Shift to proactive security. Your company is entitled to resilience, rather than recovery.
#Cybersecurity
#PenetrationTesting
#DataBreach
#RiskManagement.
English
P.H.A.N.T.O.M F.O.R.T retweetledi

@Phantom_Secure @cyber_rekk Which job? People wey dey fail technical interview like crazy
English

>security engineer
>has never opened Wireshark
>has never written a detection rule
>has never investigated an alert
>doesn't know what CVE or CVSS means
>doesn't know how vulnerabilities are actually exploited
>talks about AI cybersecurity
but can't explain how a firewall works
You know yourself
Go and learn
English
🚨 SOMEONE SWAPPED ~50.43M $aEthUSDT (from Aave) swapped via CoW Protocol for 327.24 $aEthAAVE (~$35.9K value)
For $50M+ orders, always verify min received & paths—DEX liquidity can't handle it without massive loss
Source: etherscan.io/tx/0x9fa9feab3…

English

@Bigkene10 Stefan and Damon continued to live because at every point in time, they were either at the mercy of Elijah or Klaus.
English

@amadaoffor Logic won't hold, if I happen to breath fire.
English