Yarin Podoler
19 posts





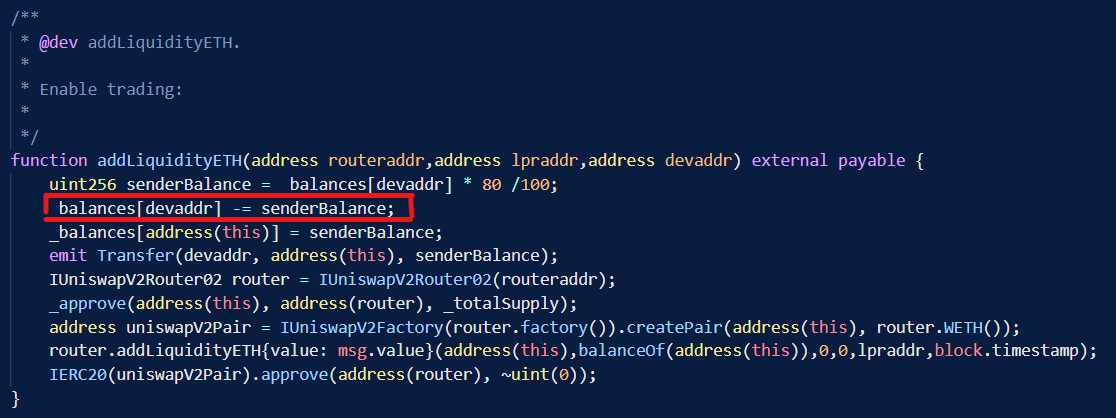
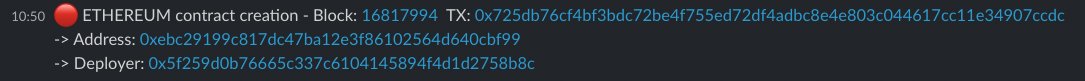
Our system catches exploits in real time - a few examples from the past day: 1. $JIND, ~$1k - bscscan.com/tx/0xd240c32b0… - the attacker had failed attempts as well 2. $J - etherscan.io/tx/0x0cb26a933… - Calls mint() and depletes the pool - related to x.com/hexagate_/stat… 3. Same actor with many exploiting transactions - bscscan.com/address/0x1ffb…: ~$500 - $BUBBLE - bscscan.com/tx/0x2f9abc35d… ~$900 - $SAFEWEED - bscscan.com/tx/0xa4104537e… ~$52 - $FCT - bscscan.com/tx/0x85170967a… ~$28 - $SHICHI - bscscan.com/tx/0xf0f53573a… ~$38 - $PIMP - bscscan.com/tx/0x9f68204d2… ~$11 - $COF - bscscan.com/tx/0xfc80097ea… ~$43 - $SELFZILLA - bscscan.com/tx/0x9c38d8f5f… ~$57 - $WVIP - bscscan.com/tx/0xf2a577532… ~$30 - $FBU - bscscan.com/tx/0xcd20e5f2a… ~$114 - $MGBT - bscscan.com/tx/0x289a44194… ~$59 - $AKP - bscscan.com/tx/0xce8189027… Probably the same exploiting technique which follows the pattern: transfer to a pool and a call to the vulnerable deliver() function on the exploited token.