
PSE
1.7K posts


@PrivacyEthereum
PSE is a research and development lab delivering privacy to the Ethereum ecosystem.






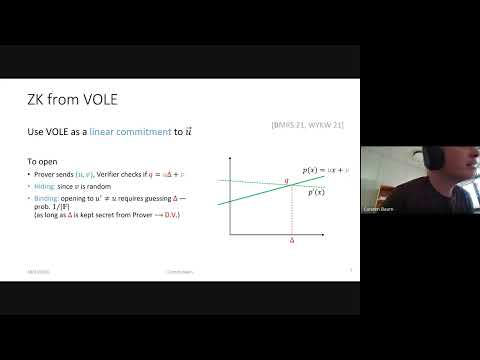
welcome PlasmaBlind: a new privacy L2 that ditches SNARKs altogether, with <100ms client-side zk proofs, using the blindfold scheme and a carefully designed aggregator. uncompromising and instant privacy on *any* device. we implemented and benchmarked the whole thing at @PrivacyEthereum and are opening it under MIT. paper + code available at plasmablind.xyz the time for a special purpose privacy L2 has come 😎


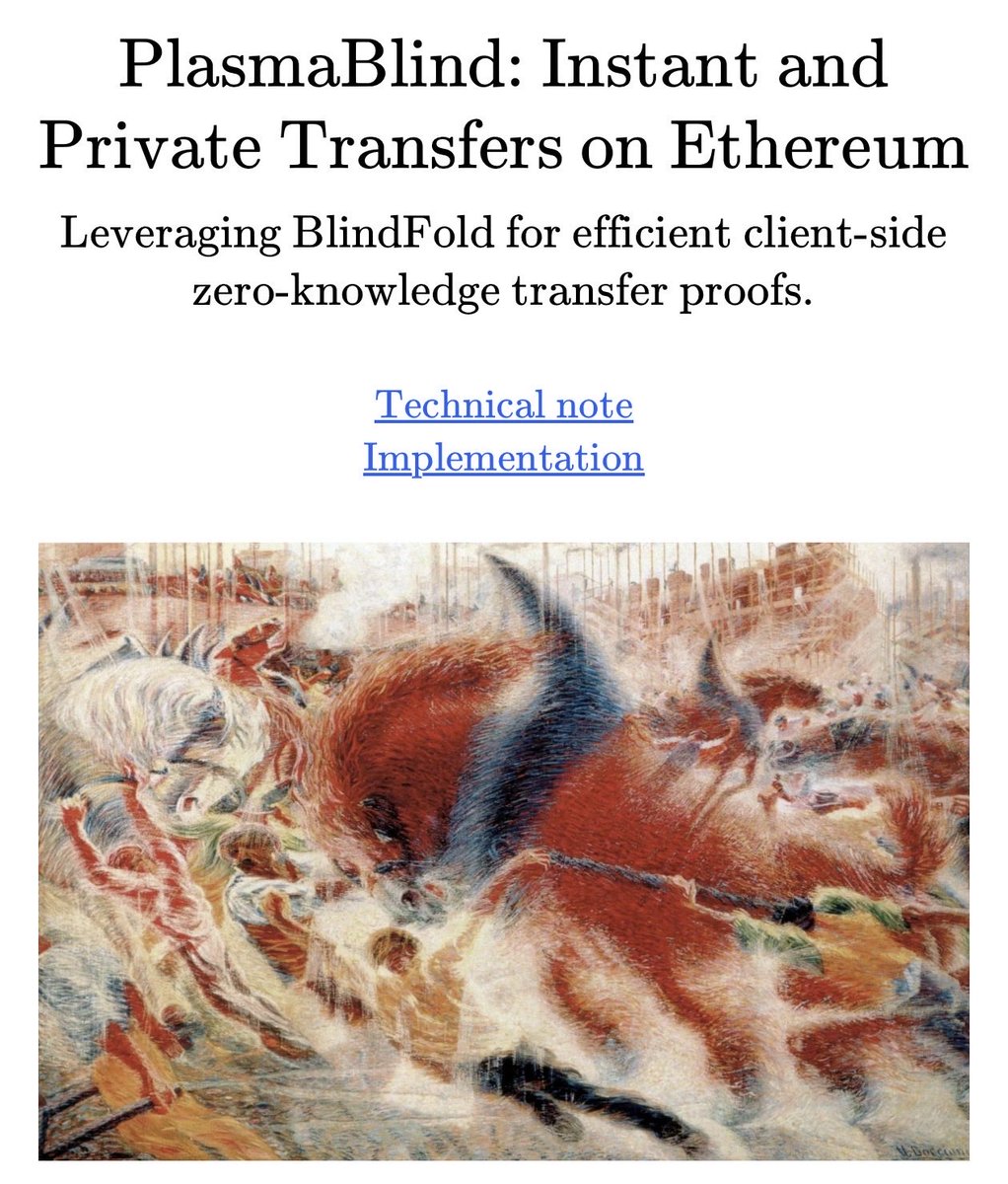
welcome PlasmaBlind: a new privacy L2 that ditches SNARKs altogether, with <100ms client-side zk proofs, using the blindfold scheme and a carefully designed aggregator. uncompromising and instant privacy on *any* device. we implemented and benchmarked the whole thing at @PrivacyEthereum and are opening it under MIT. paper + code available at plasmablind.xyz the time for a special purpose privacy L2 has come 😎











Coding an app is the new starting a podcast.