Somewhere in the 1990s, a cryptographic decision was made that nobody questioned.
In 2026, 25,000 developers woke up holding the bill for it.
Nobody asked the developers.
Not when the cryptographic assumptions were baked into every protocol. Not when the standards were finalized. And not when the migration timelines started appearing in government memos.
The engineers just woke up one day holding the bill for a decision that was made in the 1990s.
Here is what that bill actually looks like.
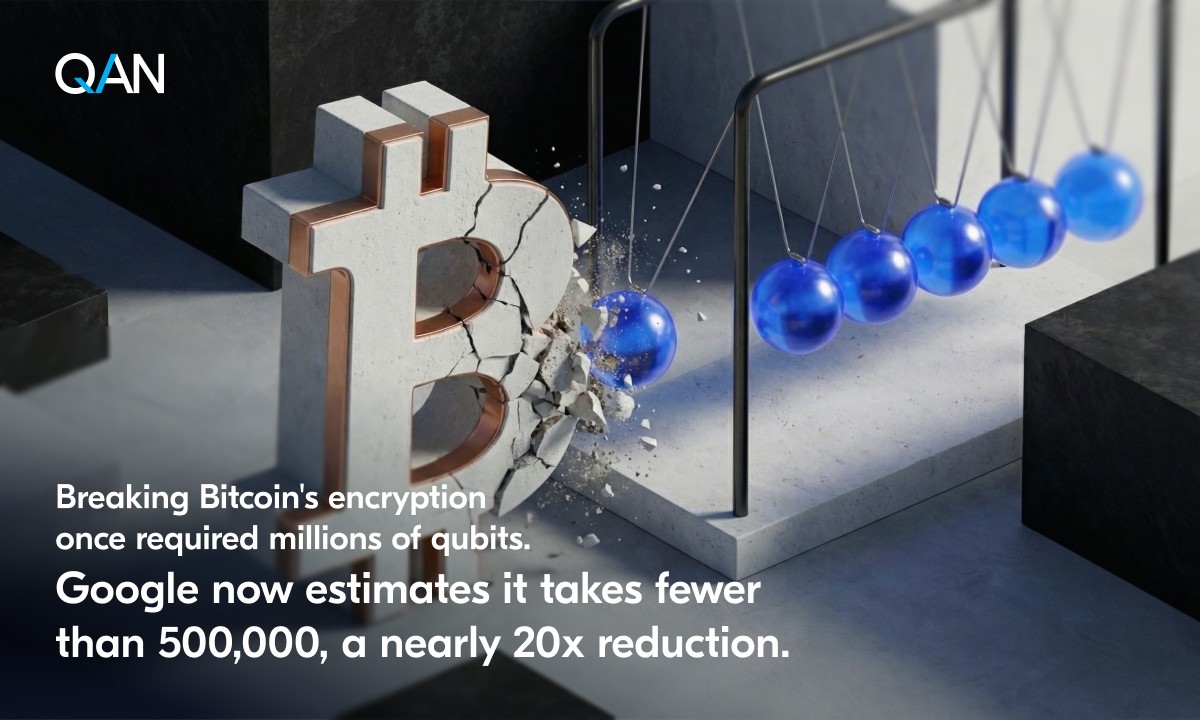
There are roughly 20,000 to 30,000 active blockchain and Web3 developers globally. Not millions. Tens of thousands. A remarkably small group to be maintaining infrastructure that holds trillions in value. Every single one of them is writing against cryptographic primitives, ECDSA, secp256k1, SHA-256, that were designed before quantum computing was an engineering concern rather than a physics thought experiment.
They did not choose those primitives. They inherited them. And they built entire ecosystems on top.
Now here is the ask.
Migrate.
Rotate keys across millions of wallets.
Upgrade signature schemes on live networks with billions in locked value.
Coordinate hard forks across decentralized communities that agree on almost nothing.
Rewrite SDKs, auditing frameworks, tooling, documentation, and mental models across an industry that is already running at full capacity just keeping up with what it has.
Oh, and do it before a timeline nobody can pin down precisely, against a threat that is invisible until the day it is not.
This is not a product roadmap item. It's a civilizational infrastructure problem. Handed to a generation of developers who were just trying to build.
And the cruelest part is this.
The developers who are most exposed are not the ones who made the original design choices. They are the ones who arrived later, learned the tools that existed, shipped real things, and are now being told the foundation those tools sit on has an expiration date.
Post-quantum cryptography is not complicated because the math is hard, though it is. It is complicated because ML-DSA and ML-KEM, the NIST-standardized algorithms meant to replace what we have, are not drop-in replacements. Signature sizes are 30 to 40 times larger. Key generation behavior is different. The entire security proof rests on different mathematical hardness assumptions that most working developers have never had reason to study.
The tooling is immature. The libraries are young. The audit standards for post-quantum smart contract security do not fully exist yet.
So what is the actual solution?
It is not telling developers to become post-quantum cryptographers on top of everything else they are already doing.
It is building the quantum-safe layer underneath them. Into the protocol. Into the base layer. So that a developer writing a smart contract in 2026 does not have to understand lattice-based cryptography any more than a developer writing a web app today needs to understand the TLS handshake.
The best infrastructure becomes invisible. It solves the hard problem at the layer where the hard problem belongs, and hands developers a clean surface to build on.
We understand this and we are not asking developers to carry the quantum migration. We ship the solution ourselves.
English