Sabitlenmiş Tweet
Quantum Vision Holdings
97 posts


Quantum Vision Holdings
@QVHINC
Building Post Quantum Security Infrastructure for Regulated, Mission Critical Systems.
Katılım Ocak 2026
78 Takip Edilen21 Takipçiler

$86.9M in crypto exploits this year; without quantum.
That should reframe the conversation.
These incidents are not isolated. They reflect structural weaknesses in how keys are generated, stored, and trusted.
If systems are failing under current conditions, the introduction of post-quantum risk will not be incremental, it will be systemic.
The National Institute of Standards and Technology has established the next baseline: FIPS 203, 204, 205.
The question is whether infrastructure is being built to adapt or simply patched to respond.
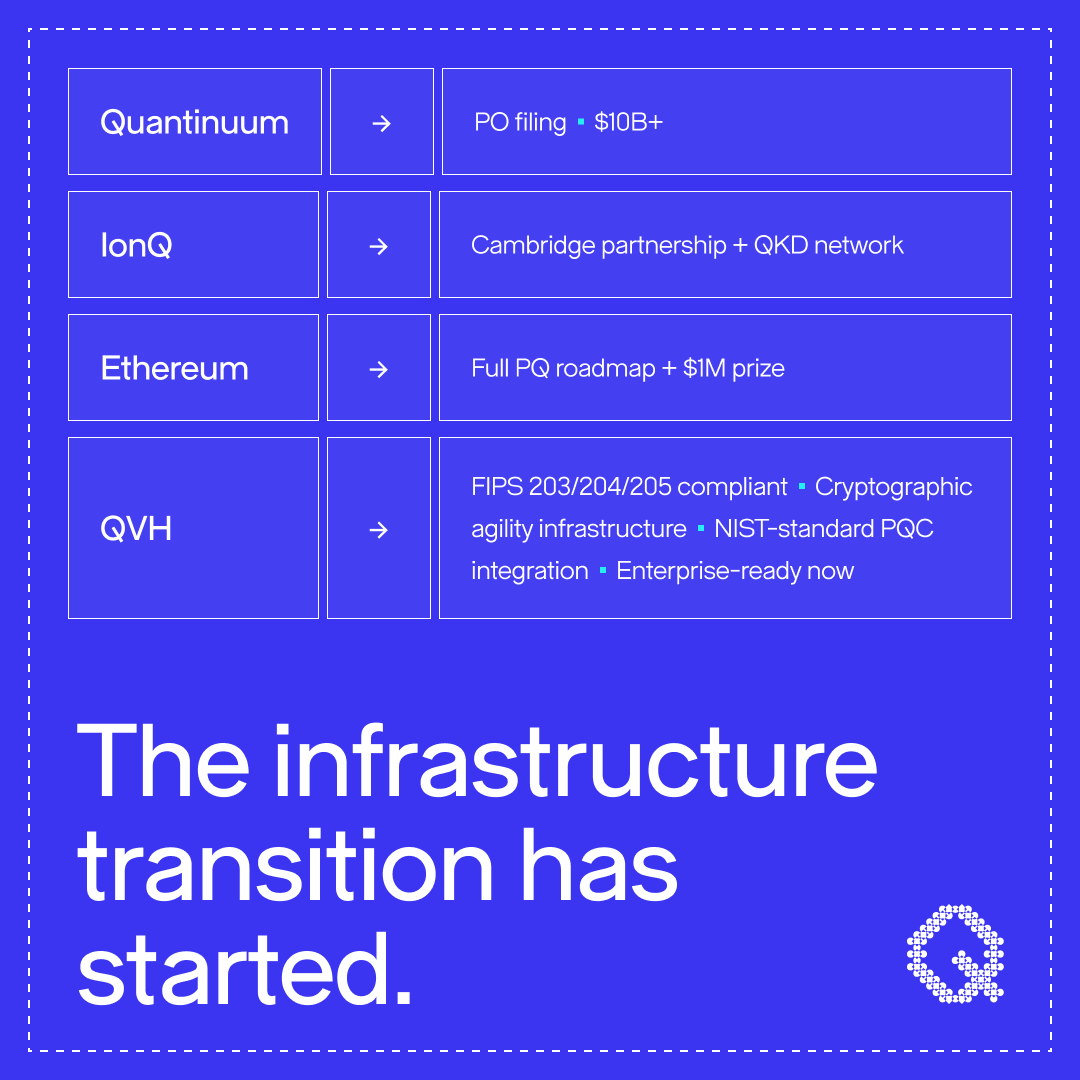
QVH implements all three standards in a unified cryptographic agility stack.
This is not reactive security. It is foundational.
English

Most organizations haven’t internalized this yet: Post-quantum cryptography now has a timeline.
Canada has begun formalizing timelines for post-quantum cryptography adoption across federal systems.
This isn’t about today’s risk. It’s about protecting data that will be targeted years from now under a “harvest now, decrypt later” model.
The National Institute of Standards and Technology has already defined the standard: FIPS 203, 204, 205.
What’s being underestimated is the implementation.
This is not an upgrade to existing systems. It’s a redesign of trust, identity, and key infrastructure.
QVH implements all three standards in a single cryptographic agility stack.
That’s not a feature set. It’s architecture.
English

Quantinuum is filing to go public at $10B+ valuation. IonQ just partnered with Cambridge and delivered one of Europe's largest QKD networks.
Vitalik Buterin published a full post-quantum roadmap for Ethereum; with a $1M prize attached.
The quantum timeline isn't compressing someday. It compressed this week. If your PQC migration plan still says "2028, begin assessment," you're already behind. QVH is building the security layer for it.
#QuantumComputing #PQC #Quantinuum #IonQ #Ethereum #Cybersecurity
English

The PQC debate is focused on the wrong problem.
Everyone's arguing algorithms. Almost nobody can answer a simpler question: where is your cryptography actually running right now?
You can't migrate what you can't see. And most organizations are carrying more Quantum Debt than they realize.
The math is solved. The operational work? Barely started.
#QuantumComputing #CISO #PQC #DataSecurity
English

The genomic, biometric, and clinical records inside our hospitals aren’t just medical data anymore they’re sovereign intelligence.
AI systems are already capable of indexing stolen datasets to map vulnerabilities across populations, leaders, and high-value individuals. And with the quantum timeline advancing, “harvest now, decrypt later” is no longer a theory, it’s a strategy.
At QVH, we’re building the post-quantum infrastructure needed to protect the systems that protect us.
Hardware-rooted entropy, quantum-safe key management, and secure clinical architectures are no longer optional. They’re part of national resilience.
This isn’t cybersecurity. It’s healthcare defense.
#PostQuantum #HealthcareIT
English

The post-quantum security market is solving the wrong problem.
Most of the focus right now is on:
🔹new algorithms
🔹encryption libraries
🔹developer SDKs
All important. None sufficient. Because encryption doesn’t live in isolation.
It depends on infrastructure:
🔹hardware
🔹key management
🔹entropy
🔹integration layers
If your keys are generated on compromised hardware, your encryption is already broken.
If your key management can’t handle PQC at scale, your migration fails before it starts.
Post-quantum crypto on weak infrastructure is still weak security.
The real problem isn’t upgrading encryption. It’s rebuilding the system that depends on it.
That’s the layer we’re focused on at QVH.
#PostQuantumCrypto #CyberSecurity #CryptoInfrastructure
English

The mandates are public.
The timelines are set.
The question is:
Who is actually building the layer that makes this transition possible?
#PostQuantumCrypto #CyberSecurity #QuantumSafe #CNSA2
English

This week’s conversations around the cyber incident affecting Stryker Corporation sparked a broader discussion about the future of cybersecurity.
A few takeaways that stood out:
Modern systems are becoming deeply interconnected from medical devices and healthcare networks to energy, transportation, and other critical infrastructure.
As these systems evolve, cybersecurity is shifting from protecting isolated IT environments to protecting entire digital ecosystems that support real-world operations.
At the same time, governments and researchers are already preparing for the next era of cybersecurity challenges, including the implications of emerging technologies like quantum computing and the need for post-quantum cryptography being developed by organizations such as National Institute of Standards and Technology.
Taken together, these developments point toward an important shift: Cybersecurity is increasingly becoming infrastructure security.
Protecting the systems that support modern society will require collaboration across industries, governments, and technology providers as digital environments continue to grow in complexity.
It’s been interesting to see how this conversation has evolved throughout the week.
Curious to hear how others in the cybersecurity and infrastructure communities are thinking about these challenges.
#Cybersecurity #CriticalInfrastructure #HealthIT #PostQuantumCryptography
English

Three structural cybersecurity risks in healthcare that are still widely underestimated:
1. Medical device lifecycle risk
Many medical devices remain deployed for 10–15 years or longer.
That means security architectures designed today may need to protect systems operating well into the next decade.
Updating or replacing devices in clinical environments is far more complex than updating typical IT systems.
2. Long-lived healthcare data
Patient records often require protection for 20+ years.
Clinical research data and medical imaging archives can remain sensitive even longer.
This creates a unique problem: encrypted healthcare data captured today may remain valuable decades from now.
3. Expanding device connectivity
Hospitals now operate thousands of connected devices across clinical networks.
🔹Imaging systems
🔹Monitoring platforms
🔹Surgical equipment
🔹Diagnostic tools
Every connected system expands the potential attack surface.
Incidents like the one affecting Stryker Corporation are reminders that healthcare cybersecurity is increasingly about protecting long-lifecycle infrastructure.
It’s one of the reasons our team spends so much time thinking about this challenge at QVH.
#HealthcareCybersecurity #HealthIT #MedicalDevices #CyberSecurity
English

Recent reporting about the cyberattack affecting Stryker Corporation should be a wake-up call for how we think about healthcare cybersecurity.
Hospitals today operate thousands of connected medical devices, imaging systems, surgical tools, patient monitors, infusion pumps, all integrated into complex digital networks that support modern care delivery.
This connectivity has dramatically improved healthcare.
But it has also quietly transformed hospitals into some of the most complex cybersecurity environments in the world.
One challenge that doesn’t get discussed enough is time.
Medical devices often remain deployed in clinical environments for 10–15 years or longer.
Patient records may need protection for 20+ years due to regulatory and clinical requirements.
Clinical research data can remain valuable for decades.
Most cybersecurity architectures were never designed around timelines like that.
As healthcare systems become more connected, protecting them requires thinking beyond short-term threat response and toward long-lifecycle infrastructure resilience.
Healthcare will likely be one of the sectors most affected by that shift.
Incidents like the one impacting Stryker highlight something important: Healthcare cybersecurity is no longer just about protecting IT systems.
It’s about protecting complex infrastructure that supports patient care, and that infrastructure must remain secure for decades.
#HealthcareCybersecurity #HealthIT #MedicalDevices #CyberSecurity
English

Healthcare data isn’t PHI, it’s biometric sovereignty.
AI is already exploiting stolen medical datasets, and quantum computing will make today’s encrypted data tomorrow’s open book.
If hospitals are the new perimeter, then quantum-safe infrastructure is the new defense.
QVH is building the hardware, entropy, and PQ systems that make that defense real.
#PQC #CyberSecurity #HealthcareSecurity #QuantumSafe
English

Healthcare infrastructure has a different clock.
Many medical devices remain in service for 10 years or more.
Encryption standards, however, evolve on a different timeline.
That creates a practical question: How do you upgrade cryptographic foundations when the hardware they’re embedded in isn’t designed for frequent change?
This isn’t theoretical; it’s infrastructure planning.
Post-quantum transition in healthcare is about aligning two timelines:
🔹Device lifecycle.
🔹Security evolution.
That alignment takes intention.
#HealthcareIT #PostQuantum
English