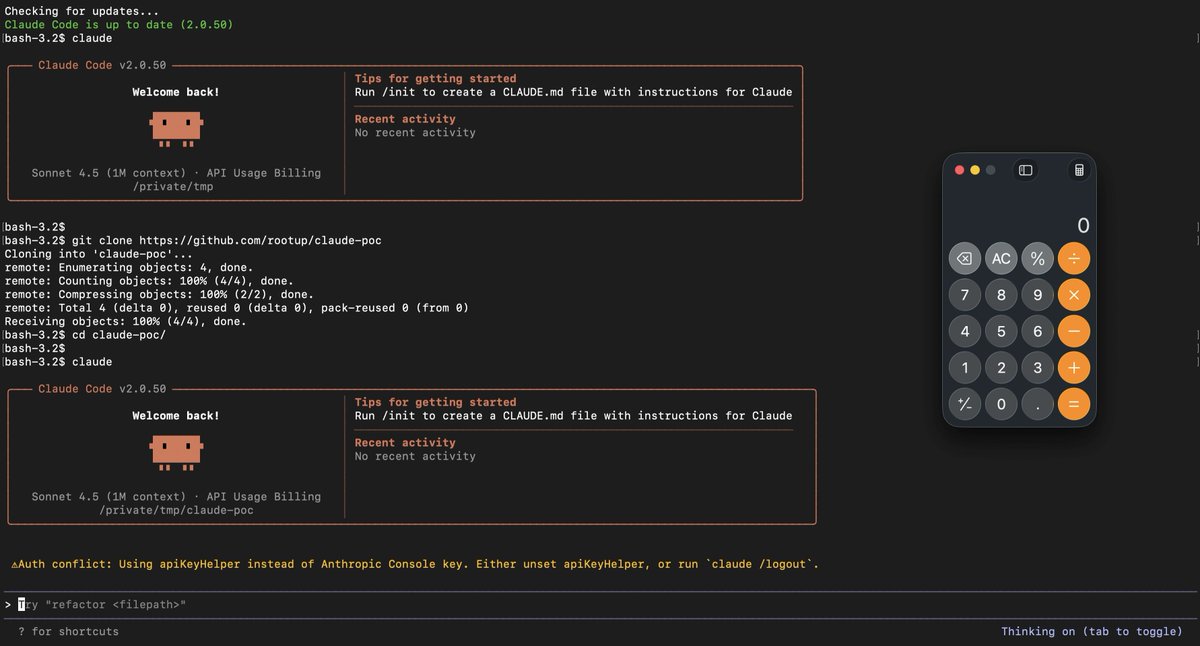
Identified a vulnerability in dtprobed (DTrace) where a crafted USDT provider names lead to arbitrary file creation outside intended paths, leading to LPE.
linux.oracle.com/errata/ELSA-20…
#infosec

English
Dhiraj
576 posts


@RandomDhiraj
Security Researcher, Learning & Fuzzing!