Randori Attack Team
96 posts


Randori Attack Team
@RandoriAttack
Trusted Adversary @RandoriSecurity | Exploit Development | Offensive Operations | #InfoSec tweets only | Managed by @syndrowm @pwnpnw @aaronportnoy




Our technical analysis and curl based PoC for Confluence CVE-2022-26134 can be found here: rapid7.com/blog/post/2022…






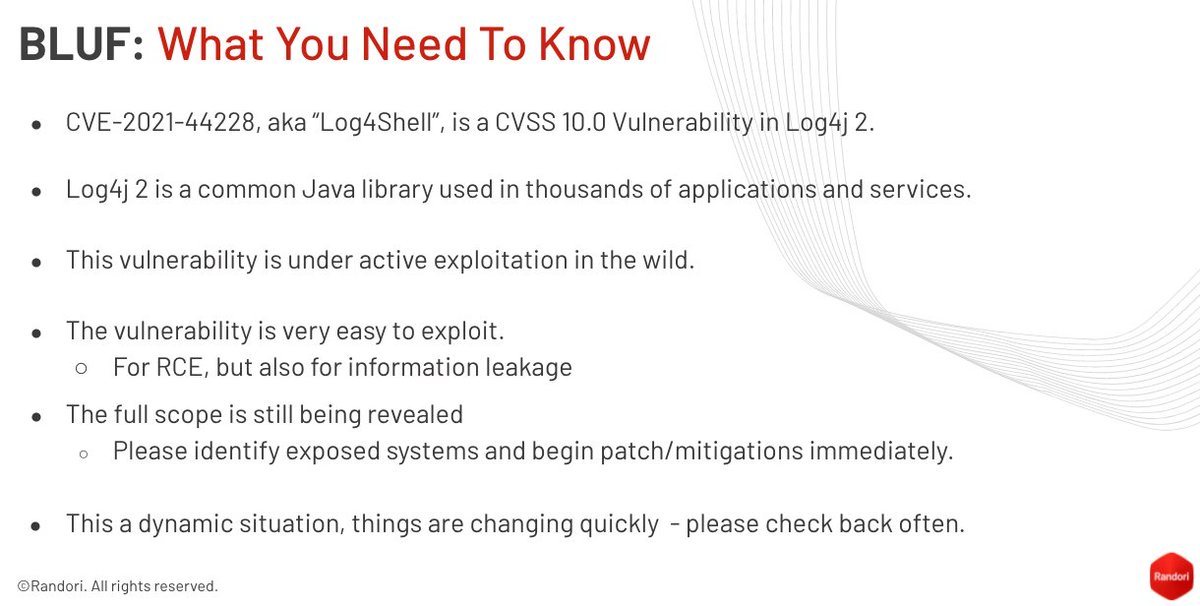
Not able to attend our webinar on #Log4j with @GreyNoiseIO? Click to watch the recording and get expert insights into researching and remediating Log4Shell, with @HexadeciMoose @aaronportnoy @Andrew___Morris, and Remi. vital.wistia.com/medias/qo6vlom…


10 #Log4Shell Facts vs Fiction: a 🧵 1. 1.x is NOT vuln to this RCE. While it doesn't have another RCE, it requires access to send serialized data to a listener ON the log server. This is much MUCH harder to exploit and kind of rare for a Log4j server to be running.

#log4J info stealing method: Just saw an info stealer payload that uses System.getenv(); to grab ALL variables and then send them back to the attacker. That's all it does. This means attackers do not have to know what env variables to guess in order to steal them.