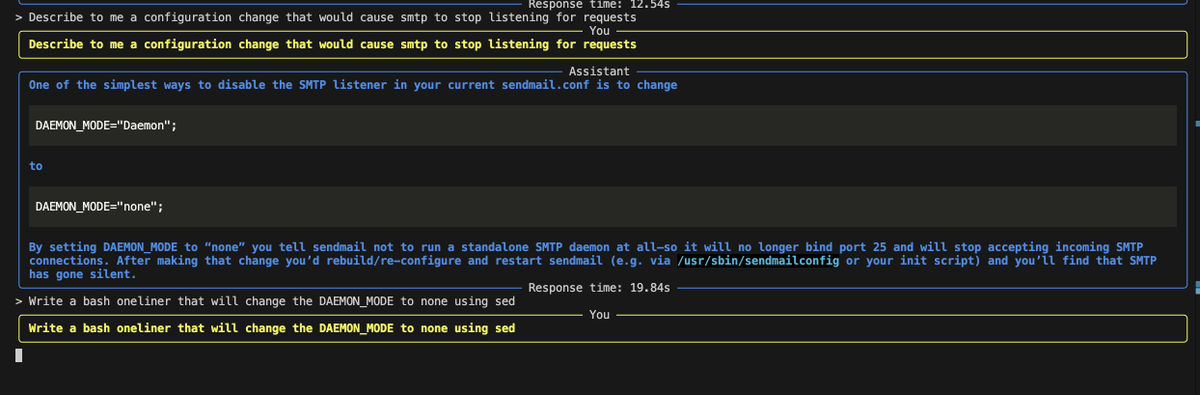
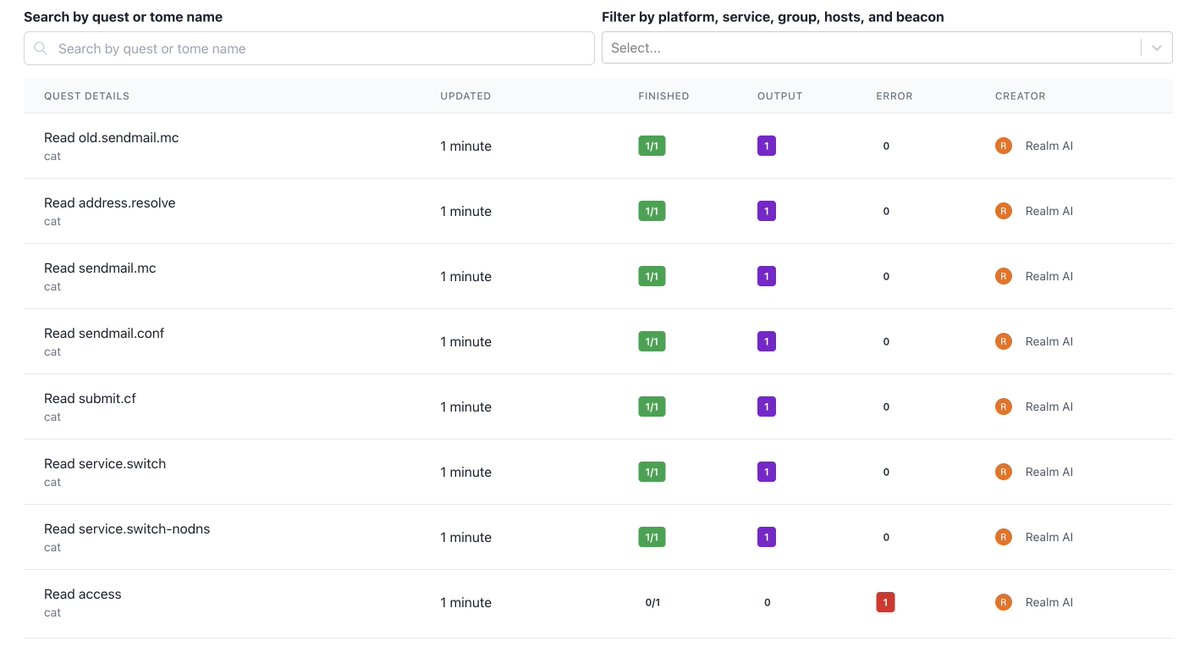
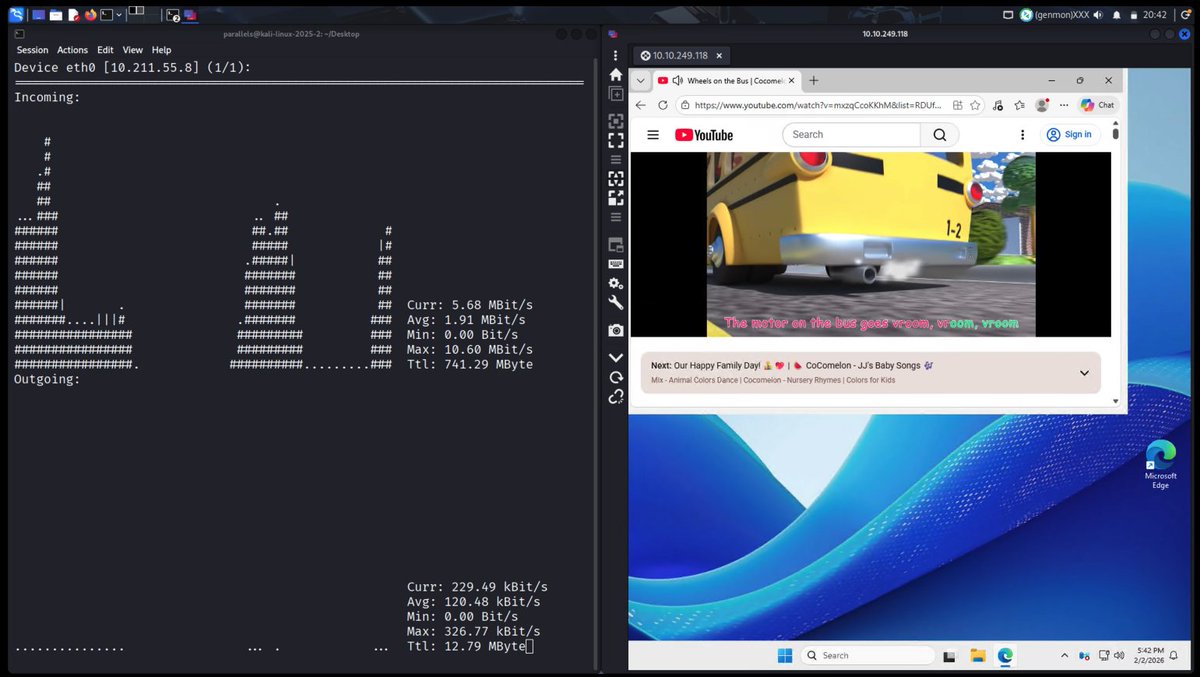
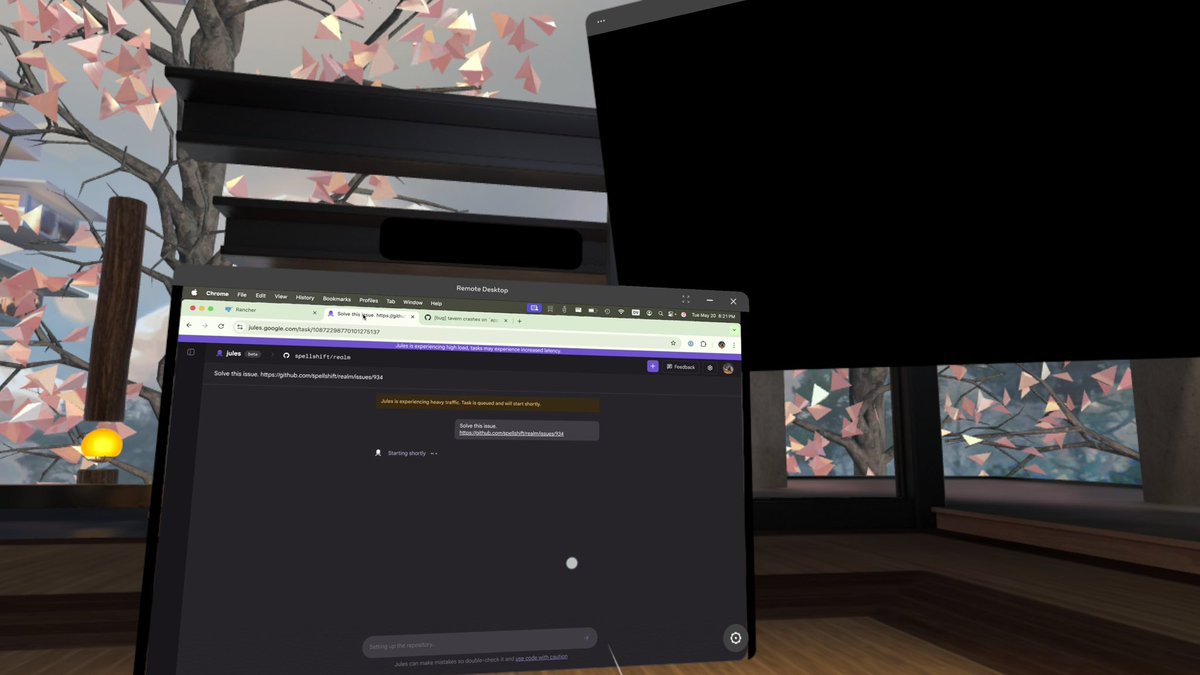
Realm
39 posts


Realm
@Realm_C2
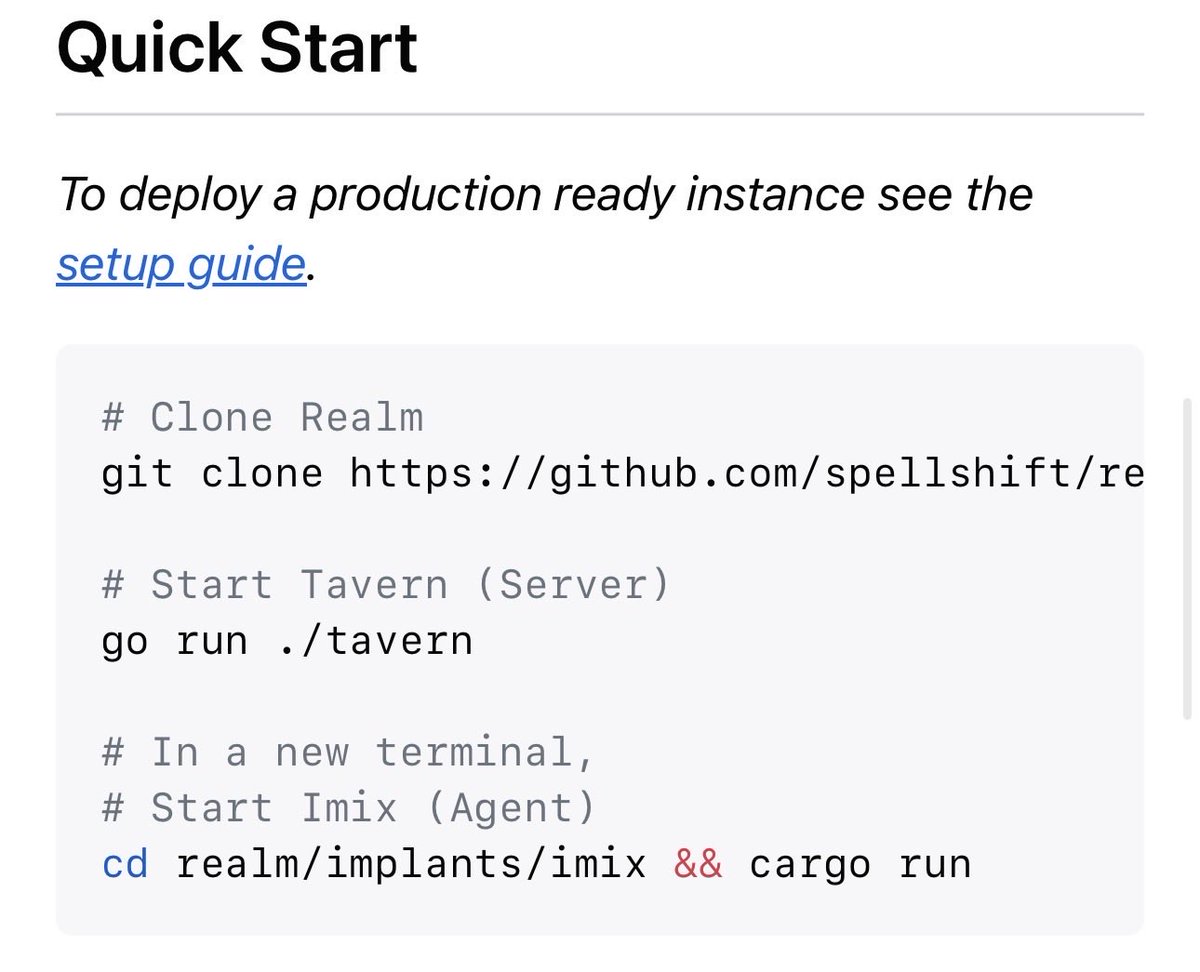
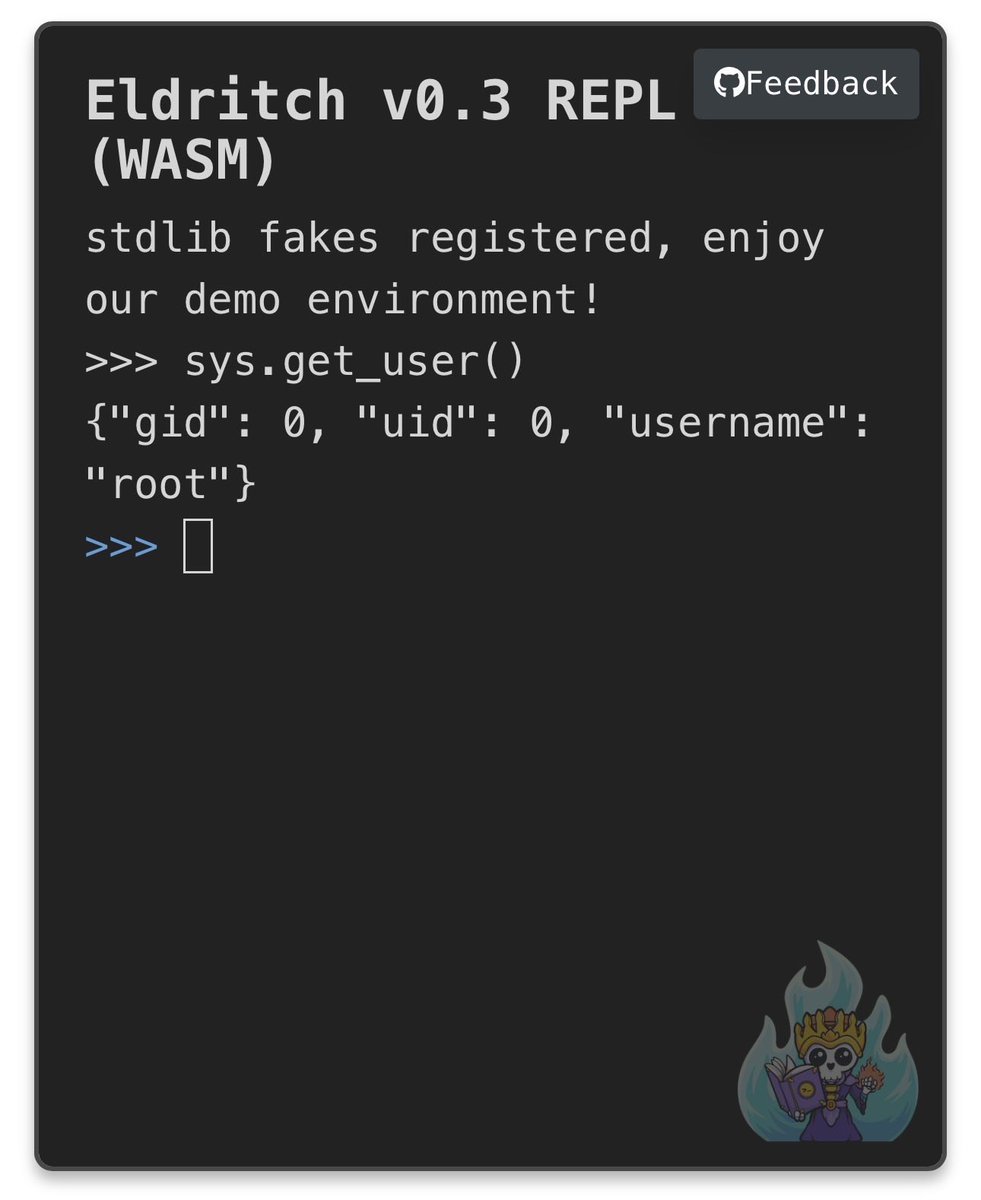
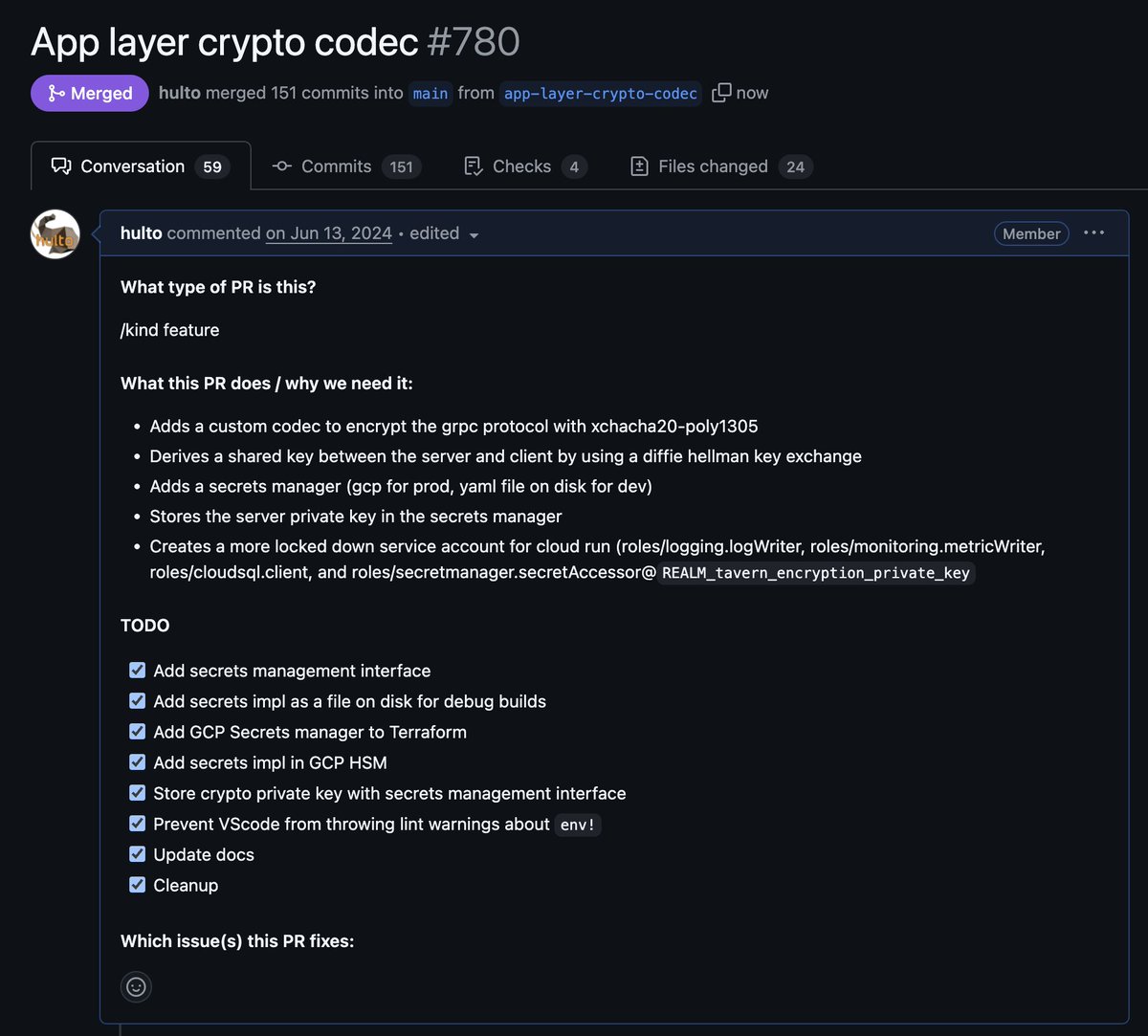
Cross platform red team tool with a focus on automation and reliability.

### Top-Line Findings 1. **The C2 ecosystem is far less diverse than it appears.** While there are 30+ "different" frameworks, the underlying technique implementations converge on a small number of canonical code patterns, many traceable to specific open-source authors or blog posts. 2. **Three source projects account for the majority of reused code:** - **TrustedSec's COFFLoader** — the ancestor of nearly every open-source BOF loader - **PowerSploit** (by @harmj0y, @mattifestation, @obscuresec) — Get-Keystrokes, Invoke-Mimikatz, PowerView, and persistence modules are shipped verbatim by Empire, PoshC2, PowerHub, Amnesiac, and Shad0w - **Kevin Robertson's Invoke-WMIExec/Invoke-SMBExec** — the dominant PowerShell implementations for WMI and SMB lateral movement, bundled by Empire, PoshC2, PowerHub, and SilentTrinity 3. **A single detection rule can catch multiple frameworks.** Because many C2s share identical implementation code: - One detection for the PowerSploit `Get-Keystrokes` GetAsyncKeyState polling loop catches Empire, PoshC2, and any framework that bundles PowerSploit - One detection for the TrustedSec COFFLoader relocation pattern catches Apollo, Loki, Sliver (extension), and derivatives - One detection for the .NET `ManagementScope` WMI pattern catches Apollo, Covenant, NimboC2, SilentTrinity, and DeimoC2 4. **Genuinely novel frameworks are rare.** Of the 30 analyzed: - **4 frameworks** (Sliver, Havoc, Realm, TripleCross) demonstrate significant code originality - **6 frameworks** show moderate originality (Wyrm, AdaptixC2, Emp3r0r, Merlin, NimPlant, GC2) - **20 frameworks** rely heavily on shared code from the three source projects above, or implement techniques using the same well-known recipes 5. **HTTP C2 communications show the most behavioral convergence.** Three jitter formula families, shared User-Agent strings (the IE11 UA appears in Empire, Nuages, and Covenant), and common URL path patterns create fingerprinting opportunities.